Grant SET LABEL privilege for the specified label on all graphs to the specified role. Revoke READ privilege on a specified property in a specified graph from the specified role. Revoke immutable CREATE ROLE privilege from the specified role. When immutable is specified in conjunction with a REVOKE command, it will act as a filter and only remove the matching immutable privileges.
What Are The Delivery Times For Your Products?
Mastering Cypher involves deciphering encrypted messages, exploring directories, and exploiting server weaknesses. By delving into this realm, you’ll enhance your ability to identify and mitigate potential security threats. Get ready to unravel the mysteries of Cypher and enhance your cybersecurity expertise.
- Grant SET DATABASE ACCESS privilege to set database access mode for standard databases to the specified role.
- Reconnaissance in HackTheBox challenges is crucial as it helps identify vulnerabilities, services, and attack vectors.
- With a user-friendly Tkinter interface, securely send and receive files over the network.
- Create varied levels of message security with different coding algorithms.
- Grant SHOW PRIVILEGE privilege to list privileges to the specified role.
Engage in discussions, follow tutorials, and leverage tools, including anyone’s email address shared by the cybersecurity community, to enhance your skills with the app. All that has been said above about node uniqueness constraints also applies to relationship uniqueness constraints.However, for relationship uniqueness constraints there are some additional things to consider. For example, MERGE can be used to specify that a graph must contain a node with a Person label and a specific name property.If there isn’t a node with the specific name property, a new node will be created with that name property. Grant DROP DATABASE privilege to delete standard databases to the specified role.
List Operators
The datetime.truncate() function truncates the given temporal value to a ZONED DATETIME instant using the specified unit. The toStringOrNull() function converts an INTEGER, FLOAT, BOOLEAN, STRING, POINT, DURATION, DATE, ZONED TIME, LOCAL TIME, LOCAL DATETIME or ZONED DATETIME value to a STRING.For any other input value, null will be returned. The toIntegerOrNull() function converts a BOOLEAN, INTEGER, FLOAT or a STRING value to an INTEGER value.For any other input value, null will be returned. The toFloatOrNull() function converts an INTEGER, FLOAT or a STRING value to a FLOAT.For any other input value, null will be returned. The toBooleanOrNull() function converts a STRING, INTEGER or BOOLEAN value to a BOOLEAN value.For any other input value, null will be returned.
- The trim() function returns the given STRING with leading and trailing whitespace removed.
- The UNION clause can be used within a CALL subquery to further process the combined results before a final output is returned.
- Mastering Cypher involves deciphering encrypted messages, exploring directories, and exploiting server weaknesses.
- Create a node property uniqueness constraint on the label Person and properties name and age.
Hydra Market Darknet
Slicing inner LIST values require two operators; the first accesses elements from the outer LIST, while the second slices or accesses elements from the inner LIST. List the running transaction (within the instance), with a specific transaction_id.As long as the transaction IDs evaluate to a string or a list of strings at runtime, they can be any expression. This example sets the property marked to true on all relationships along a path. Calls the built-in procedure db.labels inside a larger query to count all labels used in the database.
Unmasking The Dark Web Economy: Key Hubs And Cybersecurity Implications
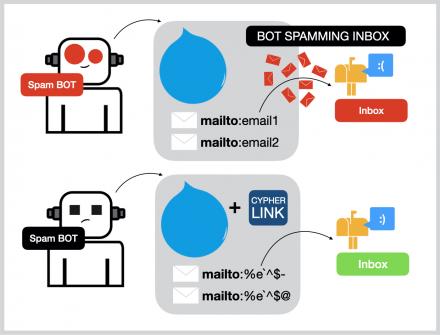
CipherLink is a lightweight, high-performance communication library designed to provide end-to-end encryption for secure data exchange between clients and servers. Leveraging industry-standard AES-GCM encryption, CipherLink ensures the confidentiality and integrity of messages transmitted over the network. The platform acknowledges its growth phase, with its administrators dedicated to implementing significant enhancements for a better user experience. Delivery times can vary depending on your location and the shipping method you choose. For more information on cypher darknet delivery times, please check our shipping policies.
What Is A Cipher Identifier? (Definition)
The Secret Code Translator has brought new life to our weekly club activities. We use it for team-building exercises and secret message competitions. The variety of encoding options keeps things fresh, and it’s really helped spark interest in cryptography among our members.
Grant MERGE privilege on all properties, on all nodes with a specified label in all graphs, to the specified role. Grant SET PROPERTY privilege on a specified property, on all relationships with a specified type in a specified graph, to the specified role. Revoke MATCH privilege on all graphs and all nodes with either foo_label or bar_label and with a secret property that is null from the specified role. Grant READ privilege on all graphs and all nodes with a secret property set to false to the specified role. Deny READ privilege on a specified property, on all relationships with a specified type in a specified graph, to the specified role. List the currently logged-in user, returns only the default outputs (user, roles, passwordChangeRequired, suspended, and home).
Node And Relationship Operators
Embarking on Cypher, a medium-difficulty Linux machine on HackTheBox, offers a rich exploration into web application vulnerabilities, network service misconfigurations, and privilege escalation techniques. This comprehensive writeup delves into each step of the penetration testing process, expanding upon initial reconnaissance with detailed analysis and exploitation. By thoroughly examining Cypher’s challenges, we not only enhance our cybersecurity skill set but also gain insights into real-world scenarios that mirror common organizational vulnerabilities.

While popular commodities like cannabis and stimulants are readily available, the marketplace excels in its ‘Other’ fraud section, presenting exclusive guides and tools. Cypher’s offerings are further enriched by unique custom hacking services, malware, and coveted data dumps, affirming its pioneering status in the darknet market space. Cypher distinguishes itself through its straightforward yet vibrant presentation. Beyond typical offerings like drugs and fraud-related goods, the marketplace is a repository of scarce and fascinating items, each detailed with compelling narratives.
Never use access links from unauthorized websites or social media. Cypher Market relies on advanced technical infrastructure to provide anonymity and good service. The site is only available on the Tor network`s hidden services using onion routing for every connection. Distributed server networks across various geographies are managed by administrative groups to achieve operational continuity and immunity against focused attacks.
Employ Python scripts and pip for automation and creating payloads within an archive of folders. Understanding basic Linux commands is fundamental for navigating systems. To mitigate risks, regularly scan for vulnerabilities utilizing tools like John the Ripper and exploit them effectively. Additionally, familiarize yourself with an instance of gogs and cryptographic concepts to decipher codes and progress through challenges more efficiently. Embrace these tools and techniques to enhance your skills in conquering Cypher challenges seamlessly.
Grant LOAD privilege on ALL DATA to allow loading all data to the specified role. Grant immutable TRAVERSE privilege on all graphs to the specified role. List all roles that are assigned to at least one user in the system.
The Downfall Of Cypher Darknet Market
The localdatetime.realtime() function returns the current LOCAL DATETIME instant using the realtime clock. The datetime.transaction() function returns the current ZONED DATETIME instant using the transaction clock. The elementId() function returns a STRING representation of a node or relationship identifier, unique within a specific transaction and DBMS. Property values of nodes and relationships can be accessed statically by specifying a property name after the . FOREACH can be used to update data, such as executing update commands on elements in a path, or on a list created by aggregation.This example sets the property marked to true on all nodes along a path.

While this suggests an increasing cybercrime threat in the region, the use of local languages and dialects may also assist law enforcement with pinpointing the location or origin of darknet users. Grant REMOVE PRIVILEGE privilege, allows the specified role to remove privileges for roles. Grant ASSIGN PRIVILEGE privilege, allows the specified role to assign privileges for roles. Grant ALTER ALIAS privilege to alter aliases to the specified role. Grant SET USER STATUS privilege to alter user account status to the specified role.
He Cypher Market uses only the Tor network architecture to offer services for users of anonymous business dealings. Most privacy experts and cybersecurity researchers investigate the marketplace to gain insight into modern darknet trade patterns. The user base on the platform is growing, reflecting rising demand for privacy-based trading platforms. The listings offered by Cypher are categorized into Drugs, Hosting & Security, Counterfeit, Software & Malware, Guides & Tutorials, and Other.



