
In conclusion, navigating the Dark Web can be a daunting task for beginners. However, with the right knowledge and precautions, it is possible to explore this hidden part of the internet safely. Understanding the Dark Web and how it works is crucial in order to protect oneself from potential risks. By using a VPN for anonymity and the Tor browser as a gateway, users can enhance their privacy and security. It is important to be cautious of scams and malware, and to protect personal information while interacting with online communities.
The Danger Of Tor Network
The major advantage of using a live OS such as Tails is that, on shut down, the OS wipes itself from the thumb drive you’ve installed it. Tor has an in-build slider which lets you adjust the level of security. This means that the JavaScript will be disabled by default on every website and some symbols and images will not be displayed. In terms of functionality, I don’t think there are too many differences between regular IMAP, POP3, and SMT services and the stuff you can use to communicate on the dark web. For instance, if you want to buy a laptop or a smartphone, you can try your luck in one of these shops. Sure, you can use other cryptocurrencies if Bitcoin’s not your cup of tea.
What Is APKPure And Is It Safe To Use On Android?
Rather, you’ll need to visit dark web aggregators that share links to various pages, or wikis where users can add dark web links manually. There are both free and paid VPN services, but if you’re planning on accessing the dark web, you’re going to want to opt for a high-quality paid VPN that offers you plenty of protection. To do so, enter a .onion URL and you’ll be taken to the dark web page being served at that address. Regular dark web visitors know that it’s possible to exploit the sketchy reputation of the space and the services offered.
- Indeed, most nations; including the United States, the United Kingdom, and India, allow access to the dark web as a lawful activity.
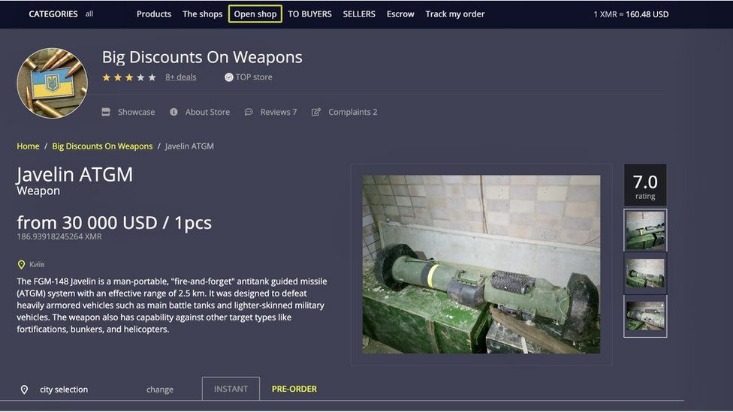
- There are often copious amounts of how-to articles, software exploits, and hacked credentials for sale.
- It can access the regular internet through “outproxies,” but that’s not its strongest suit.
- Moreover, ransomware-as-a-service (RaaS) has emerged as a significant threat, with criminal groups like REvil and GandCrab offering sophisticated malware through the dark web.
Accessing The Dark Web With Tor Browser And VPN
ZeroBin is a wonderful way to share the content you get from dark web resources. It is a reliable messaging tool where you copy/paste a text or image and send it to your addressee. Unfortunately, it requires you to have an invitation code to create an account. This means you have to know someone who is already using the platform. Even without the code, you can visit the security section to get tips on improving your daily life privacy.
How To Access The Dark Web Using Tor Browser (2025 Guide For Beginners)
Ruheni Mathenge specializes in writing long-form content dedicated to helping individuals and businesses navigate and understand the constantly evolving online security and web freedom worlds. His articles have appeared in many respected technology publications. This will help you to remain anonymous and secure at all Tor entry and exit nodes.
We provided a step-by-step guide on how to access the Dark Web securely, emphasizing the use of a VPN and the Tor Browser. We also highlighted the importance of understanding onion websites and navigating the Dark Web safely. Onion websites are websites that are only accessible through the Tor network. The “.onion” extension signifies that the website is hosted on the Dark Web and relies on the Tor network’s encryption and anonymity features to protect user identities.
What Is The Dark Web & How To Access It Safely In 2025
Therefore, the legality of the dark web will mainly depend on how you use it. You can quickly get into trouble for acting illegally, such as infringing on other people’s safety and freedom. The system is designed to provide enhanced security and privacy features. Its key features include kernel hardening, application firewall, package security, filesystem encryption, meta-proxy encryption, and binary integrity.
So not only is your web activity hidden, but you can mask your IP address by connecting via a wide range of global VPN server locations. I2P (Invisible Internet Project) is an open-source network designed to allow anonymous and private communication. Although it’s not as widely used as Tor, I2P can provide robust anonymity and is well-suited for peer-to-peer file sharing. While Tor is the most common method for accessing the dark web, I2P and Hyphanet offer alternative options for secure and private browsing.
Do I Need A VPN To Access The Dark Web On My Phone?
Since using Tor can itself draw suspicion, a VPN masks the fact that you’re using it. It also adds a crucial layer of encryption before your traffic even enters the Tor network. Talking about the fundamentals, the dark web and the darknet guarantee privacy and anonymity.


Unlike the clear web, where websites are often rated or reviewed, most dark web sites are unregulated. This is why it’s important to visit only well-known, reputable sites with a history of providing safe, reliable information or services. If you want to learn all about privacy protection or cryptocurrency, the dark web has plenty to offer. There are a variety of private and encrypted email services, instructions for installing an anonymous operating system and advanced tips for the privacy-conscious.
Friends & Links
Let’s look at two popular browsers you can use to access the dark web on desktop computers and laptops. Sites often have simple black or dark-themed backgrounds and minimal design elements. Do not log into any of your personal accounts, such as social media platforms, email inboxes, or bank accounts, when exploring the dark web. Before we look at how to access the dark web, it’s important to have a thorough understanding of what it is, as there are many misconceptions about it. Content on the Dark Web exists on overlay networks that use the Internet and special tools and configurations to sustain security and privacy.
While it might appear tempting to venture into the dark web, it’s crucial to understand that the risks here are far more severe compared to the deep web. Therefore, if you do decide to explore it, exercise extreme caution. Some whistleblowers and journalists use these portals to safely leak information, especially when a source requires complete privacy. Some markets are relatively short-lived (thanks to law enforcement), but others are notorious enough that they survive, for instance, Silk Road, AlphaBay, and Hansa. These are the primary sources of what the general public thinks of as “dark web.” Online marketplaces selling hacked credit cards, fake passports, malware kits, untraceable drugs, anything.
Should I Only Use A VPN To Access The Dark Web?

Then, simply click the operating system that you are using and download the file. While an iOS version of the official Tor browser is not available, there are Tor-compatible browsers available in the App Store. Make sure that when you download the Tor file, it’s from their official website. The majority of the users on the dark web use the Tor (The Onion Router) browser. A vast number of URLs have domain endings such as “.onion”, which means that the URLs are only accessible by Tor users. Absolutely no one knows who’s surfing on the dark web, who is selling, who is buying or anything like that – as long as you take the correct safety and online privacy precautions.



