
Dark web markets are online platforms that operate on the dark web and facilitate the buying and selling of various illegal goods and services. These markets function similarly to legitimate e-commerce websites, with sellers listing their products and buyers placing orders using cryptocurrencies like Bitcoin. Dark web markets offer a wide range of illicit items, including drugs, weapons, stolen data, hacking tools, counterfeit money, and more. Aside from physical products, dark web markets also host the sale of digital goods and services.
Ready To Explore Web Data At Scale?
Today, darknets are populated by a vast array of users, ranging from privacy-conscious individuals to cybercriminals, hacktivists, and nation-state actors. These hidden networks provide a platform for illegal activities that include the sale of stolen data, hacking tools, weapons, counterfeit currency, and narcotics. One of the most common risks when accessing darknet markets is ending up on a fake or cloned site. Cybercriminals create convincing imitations of popular dark markets to trick users into entering their login details or sending cryptocurrency to fraudulent addresses.
Added Security: Use A VPN
- The final relay before your traffic goes to the destination website is known as the exit node.
- Most dark markets have user review systems and vendor ratings to establish trust.
- Dark web marketplaces offer a range of both legal and illicit goods.
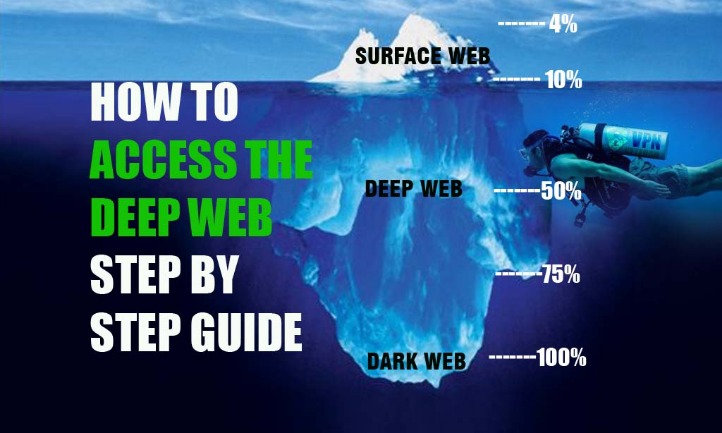
- The deep web is basically all the content that you can’t find using Google or Yahoo search.
- You could consider the clear or surface web the “top” and visible layer of the internet, easily accessible using a browser such as Safari, Chrome, Edge, or Firefox.
Many people install a VPN as well, but then you’re putting your trust in an additional third party to not track your activities or report them to anyone else. As I’ve mentioned, the dark web isn’t just a place of eternal torment, teeming with drug dealers, human traffickers, and a hitman. It’s also used by journalists, advocacy group members, and political refugees in hiding. Reuters, Fox, NBC, CNN – all of them keep open dark web channels to receive anonymous tips from whistleblowers.
When you install a VPN, all of your activities on the dark web will be hidden from unwanted snoops from your ISP or the FBI. The VPN is a second layer of extra protection, on top of the protection that the Tor network already offers. The “Hidden Wiki” (which can be accessed in a normal browser) offers a large collection of dark web links, but be careful, as many of those links are to dangerous websites. The same anonymity that publishers enjoy on the dark web can be utilized by users who want to read the available information. Again, people who live in countries where the freedom of the internet is limited, for example in China, can really benefit from using Tor.
However, these currencies, due to their decentralised and counter-economic nature, are often restricted by centralised platforms from purchase and practical use. To access the darknet you’ll need to download and install the Tor (the onion routing) browser. Of course, such marketplaces were designed to present a whole range of illegal or semi-legal products and services. Here are some of the most popular categories the dark web can present. First, let’s get the definitions and conceptual framework that we operate in straight.
How Do Dark Web Markets Work?
Thus you will need to be careful not to be tricked into downloading a cloned version of Tor for iOS. In attempting to access the Dark Web, there’s an invisible line that a person acknowledges they’re crossing – or maybe they don’t. Either way, no one is accessing the Dark Web with a sense of optimism. It offers outstanding privacy features and there is currently a discounted rate available through this link. In combination with that data, and data gathered by other methods and/or tactics may in fact lead to complete exposure and could eventually lead to the police standing at your doorstep. As I mentioned previously, the dark web is quite popular with journalists, political bloggers and news publishers, and others who run the risk of imprisonment in countries like Iran and others.
Tor Browser’s Great – But For More Complete Privacy Protection, You Need To Add This
It has built a reputation for being a reliable source of stolen credit card data and PII. Renowned for its extensive inventory of financial data and sophisticated operating methods, Brian’s Club is a key player in the underground economy of financial cybercrime. Next, select a dark web search engine like DuckDuckGo that can help you find dark web websites that cannot be indexed by traditional surface web search engines, such as Google or Bing.

Stay One Step Ahead – Protect Your Data From The Dark Web
The site allowed users to buy and sell drugs, weapons, and other illegal goods using cryptocurrencies such as Bitcoin. The Silk Road was shut down by law enforcement in 2013, but other dark web marketplaces have since emerged to take its place. The dark web refers to encrypted online content that is not indexed by traditional search engines. It requires special software, such as the Tor browser, to access. It is worth noting that not all items or services available on darknet markets are inherently illegal or unethical.
Install The Tor Browser
- That said, anonymity comes with a dark side since criminals and malicious hackers also prefer to operate in the shadows.
- Established in 2019, Russian Market is a well-known and highly regarded data store on the dark web, specializing in the sale of PII and various forms of stolen data.
- Dark markets provide a one-stop-shop for cybercriminals, offering a wide range of services such as hacking tools, stolen data, ransomware, and Distributed-Denial-of-Service (DDoS) attacks for hire.
- By using Tor, and especially in combination with a VPN, your internet signal is encrypted, making it invisible to your ISP.
It makes up about 6% of the internet, and it’s where you find everything from illegal marketplaces to forums for whistleblowers. Avoid links from forums or random websites, as these can lead to phishing, scams, or malware. OPSEC (Operational Security) involves following strict online practices to protect your identity.
As well as phishing scams, a multitude of other scams operate across the dark web. There are many fake marketplaces and platforms that might offer to sell you goods or services but actually take your money without providing anything in return. Since the dark web is unregulated, there’s almost nothing scam victims can do to seek justice or compensation. As explained earlier, you won’t be able to access the dark web the same way you would the surface web. You can’t type dark web addresses into your usual browser or search for them via Google. Instead, you have to use a specialist browser, designed to navigate the dark web.

While these hidden networks can be used for legitimate purposes, they are equally significant as vectors for cybercrime and illicit activities. Darknets and dark markets have propelled the growth of cybercrime by offering a platform for the sale and exchange of malicious tools and services. Cybercriminals use these platforms to traffic in stolen data, execute targeted ransomware attacks, and collaborate on advanced hacking techniques. Nation-state actors, too, leverage darknets for espionage and cyber warfare, capitalizing on the obscurity and untraceability they provide.
When viewed through this lens, the dark web’s legality is based on how you as a user engage with it. You might fall to the wayside of legal lines for many reasons that are important for the protection of freedom. Others may act in ways that are illegal for the protection and safety of others. Let’s unpack both of these concepts in terms of the “dark web browser” and the websites themselves. The reputation of the dark web has often been linked to criminal intent or illegal content, and “trading” sites where users can purchase illicit goods or services.

Some of these sites can be found through regular web browsers, but you’ll then need to switch over to Tor once you’ve got the onion links you want to follow. This part of the internet is notorious for illegal activities, facilitated by the anonymity it offers. Crimes range from data theft and selling illegal goods for cryptocurrencies to human trafficking and more severe offenses.
This is another reason it’s best to use a VPN and be careful on the dark web to preserve anonymity. This infects a user’s device and essentially blocks them out of it until they pay a “ransom,” usually in the form of cryptocurrency (so it’s harder to track and recover). Users could accidentally fall victim to ransomware just by clicking the wrong link or downloading a file on the dark web. If you’re in the U.S., you can make use of helpful tools like ExpressVPN’s Identity Defender to inform you if and when any of your data ends up on the dark web. This will allow you to take action right away and reduce the risk of any further damage to your data or identity.
A lot of transactions are handled via cryptocurrencies such as Bitcoin, which is relatively (but not completely) private and anonymous. Another private cryptocurrency you’ll find being used is Monero, which prides itself on being untraceable. To get on the dark web, you need a browser built for the job, and the best in the business is Tor. Tor is a browser engineered for extra security and privacy, and can be used to navigate the normal, surface web as well as the dark web. It blocks trackers, prevents user fingerprinting, encrypts data, and reroutes your browsing so no one can see where in the world you are. The dark web, for the uninitiated among you, is a virtual neighborhood beyond the borders of the normal, everyday internet (which includes the website you’re looking at right now).
While visiting any of the sites you find on those Wiki sites, do not maximize your browser, as it can help identify you by your monitor resolution. However, it’s very difficult and would require extensive resources, meaning that the average person’s identity is unlikely to be uncovered. Before entering the dark web, you need to download a dark web browser—most people use Tor (The Onion Router) or I2P (The Invisible Internet Project). Always tread carefully whenever crowdsourcing information on how to navigate the dark web. For example, ProPublica—a renowned investigative journalism non-profit— uses the dark web to communicate with whistleblowers and ensure readers can access content without facing retaliation. That is important for those who may fear persecution for their actions or live in areas where access to information is regulated.



