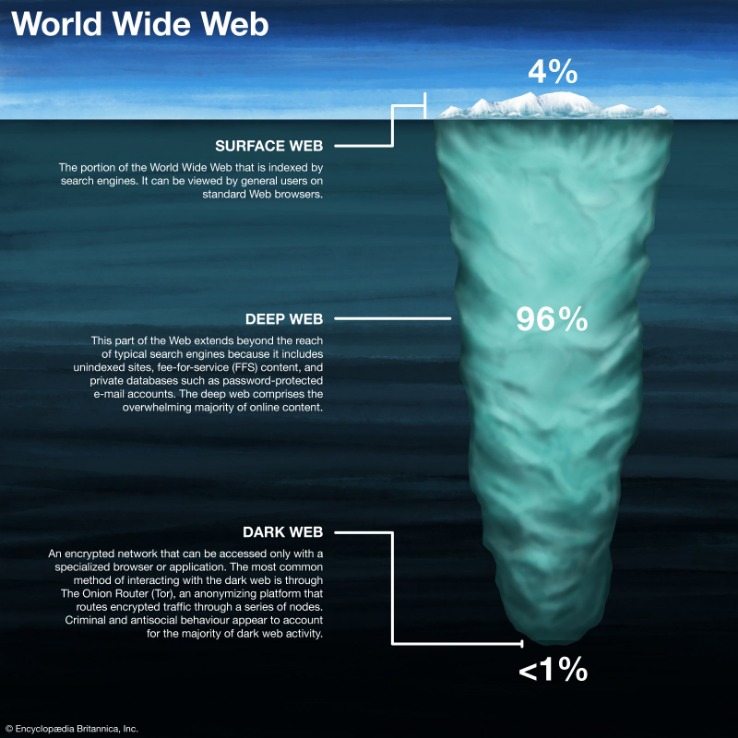
In fact, a recent judgment by the US Supreme Court denoted that simply using Tor was sufficient probable cause for law enforcement to search and seize any computer around the world. So, if you want to know how to access the dark web safely, you need to understand that the vast majority of the dark web, or dark net, is only accessible through the Tor browser. It’s like an iceberg – The visible tip above water, known as the “surface web” represents the familiar, searchable content. But lurking beneath lies the expansive, mysterious “deep web” or“dark net” – the gigantic submerged part that remains invisible to standard searches.
Some hospitals even have classified medical records you can’t access just like that. You might’ve heard of the domain extension called “.onion“, which sits at the end of each dark web website. Indeed, these websites use “atypical” names and domains to present themselves.

Legitimate Use Cases For The Average User
With its reputation for hosting illegal content, many wonder about the legality of accessing this hidden part of the internet. This topic is significant as it touches on privacy rights, cybersecurity concerns, and legal boundaries in an increasingly digital world. It’s challenging to quantify exactly how many people use the dark web, as it operates on anonymity. The Tor network, which provides access to both the deep and dark web, has millions of daily users globally, but not all are using it to access dark websites. In 2023, however, it was estimated that the dark web had more than 2.5 million daily visitors.
I like testing new software for work, but I’m less “plugged in” to the internet than I used to be. I tend to read app privacy policies to see what kind of data companies collect, and as a result of those findings, I don’t use many mobile apps. In a similar vein, I was an early adopter of many social media platforms, but now I’m just an infrequent Reddit lurker. Always use an abundance of caution when interacting with anything or anyone on the dark web. Use a computer that is not connected to your home’s internet to protect other computers on your network from malware infections or privacy intrusions.
How To Change The Tor Browser’s Security Settings On Android
The threat can extend to your entire network of devices connected to the internet. Simply put, accessing and browsing the dark web is perfectly legal. For example, it maintains your privacy and enables you to access untraceable content and services. The Dark Web is the part of the deep web that is not indexed by search engines, like Google or Bing. For this reason, you cannot browse through these sites using your default search engine.
Download Tor Browser
The creators assert that because their technique is so strong, even malware with root access could not determine the machine’s IP address. While accessing the dark web using Mozilla Firefox is possible, you must first adjust its settings. Initially, the dark web was mainly used by government agencies, big businesses, hackers, and cybercriminals. However, technological advancements such as encryption and privacy-focused browsers like Tor enabled the general public to access it.
Components Of DOT Security’s Services
Knowing if your information is on the dark web is a critical part of protecting yourself from threats. Dark web monitoring tools are similar to a search engine (like Google) for the dark web. The most common of these browsers is Tor, which launched in 2002 and serves millions of users. Another is the Invisible Internet Project (I2P), which specializes in the anonymous hosting of websites on the dark web.

It means you cannot access websites on the dark web with regular browsers like Firefox or Chrome. Instead, you need a specific configuration, software, or authorization, such as Tor, to access it. To find what you’re looking for, you may need to try multiple search engines or visit directories of trusted .onion links.
- Though these browsers are effective at serving up dark web search results, the experience is reminiscent of browsing the web in the late 1990s.
- You’ll need an overlay network to facilitate your dark web access.
- ActiveX and Java frameworks are susceptible to being exploited by hackers.
- It protects your real IP address even if Tor leaks, is easier to set up, and works with most major VPN services.
- The beginning of the dark web is generally seen as coinciding with the release of Freenet in 2000.
- For one, the VPN can’t see your online activities because of VPN encryption.
Step 4: Boot Into Tails OS From The USB Drive
The GDPR imposes strict requirements on data controllers and processors, with substantial fines for non-compliance. This has increased the risk for dark web operators mishandling personal data. Explore the legal nuances of accessing the dark web, including potential penalties and jurisdictional differences. The dark web was created not long after the first message was sent in 1969 over the original internet, ARPANET. Covert networks — or darknets — emerged quickly and provided users with private networks to communicate. Browser fingerprinting and online tracking are virtually impossible when you’re connected to the dark web via Tor Browser.
The Three Layers Of The Internet
- Much of it is tucked away in databases that Google is either uninterested in or barred from crawling.
- It includes all the essential productivity software, including MS Word and an email client.
- You may not think your Netflix login is a big deal, but reused passwords across accounts can be a goldmine for hackers or a clue about how you construct all your passwords.
- You can download the Tor Browser for Windows, MacOS, Linux, and Android.
This time, you should do it, as you’re already hidden by NordVPN’s encryption. From real-time alerts vetted by Cyble’s Security Operations Center (SOC) to AI-driven risk tagging, Cyble enables faster, more informed response decisions. Its deep insights into cybercrime forums, compromised card databases, and exposed assets give security teams a critical edge. Look for features like real-time alerting, coverage of multiple dark web forums and marketplaces, credential and data leak detection, and integration with your existing security stack. Strong vendor support, customizable alerts, and compliance alignment are also key to ensuring the tool delivers actionable insights, rather than just noise.
How To Remain Safe While Using The Dark Web – Essential Tips
Get Avast BreachGuard for Mac to protect your privacy and keep your personal data from falling into the wrong hands. Get Avast BreachGuard for PC to protect your privacy and keep your personal data from falling into the wrong hands. By monitoring known dark web marketplaces, Avast BreachGuard will alert you immediately if and when your data is found. That way, you can change your passwords and lock down your accounts to help block scammers from using your data against you.
Stolen Data And Identity Theft
Regular dark web visitors know that it’s possible to exploit the sketchy reputation of the space and the services offered. And though some dark web marketplaces offer user reviews, not all do. Lack of regulation by authorities or other users makes it easy for cybercriminals to carry out scams. Fraud and scams run rampant on the dark web, including offers too good to be true and fake services requiring upfront payment. Hackers sell access to email accounts, social media profiles, or other information that can be used for identity theft. If you use Tor to access the dark web or unblock websites, connect with a VPN for extra security.

Therefore, you should stay cautious and avoid clicking when accessing the dark web. Doing so will protect you from accidentally accessing illicit content or becoming a victim of malware. Using a VPN alongside Tor adds an extra layer of security by hiding your IP address from Tor entry nodes and encrypting your traffic. This prevents anyone—including your ISP—from knowing that you’re using the Tor network. The Deep Web includes unindexed content like private databases and password-protected sites accessible with standard browsers. Many people use it for privacy-focused communication, whistleblowing, or accessing restricted information in censorship-heavy regions.



