A top-of-the-line VPN network that ensures maximum security while accessing dark sites online. This includes military-grade 256-bit encryption reinforced with a 2048-bit DH key and SHA2-384 authentication to ensure your traffic arrives at its destination safely. This adds extra protection since opening Tor itself encrypts your traffic. The most interesting thing about NordVPN is its built-in Onion over VPN feature. It encrypts your traffic at the entry node and changes your IP address.
Verified Social Channels And News Sites

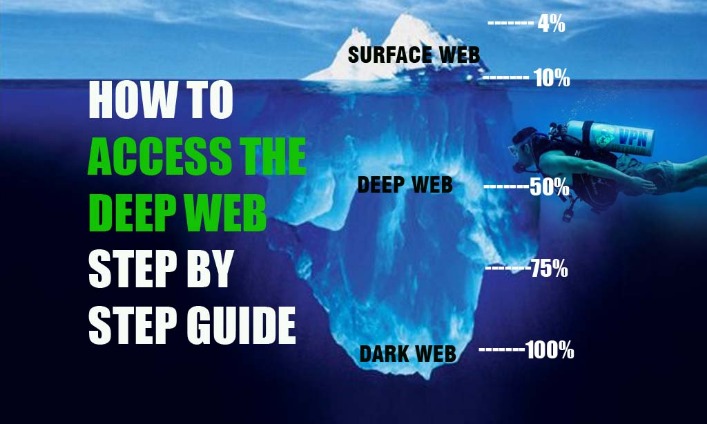
Many dark websites are set up by scammers, who constantly move around to avoid the wrath of their victims. Even commerce sites that may have existed for a year or more can suddenly disappear if the owners decide to cash in and flee with the escrow money they’re holding on behalf of customers. All this activity, this vision of a bustling marketplace, might make you think that navigating the dark web is easy. The place is as messy and chaotic as you would expect when everyone is anonymous, and a substantial minority are out to scam others. The dark web is a subset of the deep web that is intentionally hidden, requiring a specific browser—Tor—to access, as explained below. No one really knows the size of the dark web, but most estimates put it at around 5% of the total internet.
Why Should I Use A VPN Before Tor?
In the deep net, web crawlers are blocked from accessing web pages to gather information for indexing, so the content remains hidden. Some content and services on the deep web are indexed by search engines, but paywalls or password protection prevent access. Content and services on the deep web are accessible through a regular browser. The dark web isn’t something you can just stumble upon, and that’s a good thing.
Tor anonymizes by bouncing traffic through relays; VPN encrypts and routes through a single server. The silver lining is that VPNs work on iPhones so you can mitigate the risk by connecting to one beforehand. This method is far more complex but we’ll still explain it for those too curious. As opposed to the previous situation, here, you’re first connecting to Tor and then the VPN. Not many providers support this, so a manual and sometimes tedious configuration is needed.
Best Practices For Safe Tor Usage:
Go to the directory where you downloaded the Tor Browser installation file. Right-click on the downloaded file and select “Extract Here.” Once the Tor Browser setup files have been extracted, double-click on “Tor Browser Setup” to install the browser. Go to the directory where you saved the downloaded Tor Browser installation file.
She is enthusiastic about educating people about their rights to online freedom and provides actionable ways to protect their data. While such stories can cast the dark web in a negative light, it’s worth noting that there are numerous legal and beneficial activities accessible through it. I advise sticking to well-known, reliable sites and taking extra precautions to ensure your security. Hackers on the dark web can easily access your personal data using trojans, phishing, and other types of fraudulent websites or programs.
Ensure Your Privacy

With over 15 years of experience in content creation and digital publishing, he knows how to craft informative, useful content, with thorough research and fact-checking to back it up. He strives to make complex cybersecurity topics accessible and understandable to the broadest audiences. In his spare time, Michael likes writing fiction, reading murder mystery novels, and spending time with his family. A phishing website or link is one that appears legitimate but is actually a trick designed to make you hand over your personal information to hackers and other bad actors.
From in-depth reviews to the latest news and how-to guides, PCMag is the go-to source for staying ahead in the digital world. There are many legitimate uses for dark web services and communication. As search engine crawlers do not catalog these pages, you would need to know the exact link to access a website in this area of the internet. This could include government services to access your records, health care services, members-only areas, intranets, or corporate resources.
Risks Of Accessing The Dark Web:
That is why you should only use a reliable VPN like ExpressVPN or NordVPN for additional security and privacy. If the above average Joe’s explanation isn’t enough for you, below are some legitimate reasons to use the Dark Web in a bit more detail. Simply put, accessing and browsing the dark web is perfectly legal. For example, it maintains your privacy and enables you to access untraceable content and services.
Examples Of Legal And Useful Dark Web Content
- To minimize the risk, research and verify sites before visiting them.
- It is difficult to determine the exact size of the dark web, as it is not indexed by traditional search engines, and its contents are often hidden behind layers of encryption and anonymity.
- Well, relying on Tor to keep you anonymous online is a good recipe for disaster – we’ll see why soon.
- Obviously, finding these .onion websites is the first challenge, as they won’t show up in Google search results.
- The Tor Project says that of the 2 million people using Tor every day, only 1.5% of them are accessing hidden or dark websites (that’s 30,000 people).
The internet as most people know it represents only a small fraction of what truly exists online. Beneath the surface lies the Deep Web and its even more elusive subset, the Dark Web—a hidden realm where anonymity reigns supreme. While the Dark Web offers opportunities for privacy and legitimate uses, it also harbors significant risks, including cybercrime, illegal marketplaces, and the sale of stolen data. This article explores what the Dark Web is, how to access it, and most importantly, how to stay protected from its dangers. However, some activities on the dark web — such as illegal marketplaces or hacking forums — can be against laws in many jurisdictions.
It is an excellent option if you want to surf the web anonymously. Even without monitoring your browsing activities, DuckDuckGo will offer decent answers to your questions. This article lists some of the best dark web websites you can visit securely. Some of these sites are very helpful (but unseen as Google doesn’t show them), while others are just for fun. Dark web forums are online platforms that can only be accessed using anonymous networks, mainly Tor…. Using a VPN with Tor (commonly referred to as “Tor over VPN” or Onion over VPN”) adds an essential layer of protection.
Exiting Safely
If you have a legitimate or viable need to access the dark web, you’ll want to make sure you stay safe if you decide to use it. Some alleged services like the professional “hitmen” may just be scams designed to profit from willing customers. Reports have suggested the dark web offers many illegal services, from paid assassinations to trafficking for sex and weapons. As such, the dark web has attracted many parties who would otherwise be endangered by revealing their identities online. Abuse and persecution victims, whistleblowers, and political dissidents have been frequent users of these hidden sites.
Best Practices For Accessing The Dark Web
You can also find email messages, online bank statements, and much more information on the deep web – information that is usually private and inaccessible by the public on the surface web. So, sites that contain a domain extension like .com, .org, .net, .biz, .info, etc. can be found on the surface web. In addition, the content on the pages don’t need any special or custom configuration to access.
- The invisible web is made up of data and information that is not indexed and cannot be searched for by using traditional search engines.
- With RAM-based servers in 90+ countries and features like WireGuard, IPv6 leak protection, and a kill switch, worries are over.
- Tor can be used together with a VPN to provide overlapping layers of privacy and anonymity.
- While Bitcoin and other cryptocurrencies provide some level of anonymity, blockchain analysis tools can trace illicit transactions.
- Any online activity can carry breadcrumbs to your identity if someone digs far enough.
- From here, you can visit any Onion website and enjoy the dark web safely and without worries of ISP tracking and surveillance.
Avoid fraudulent Tor-like browsers that compromise your online security. The browser is free to download and works on multiple operating systems. Open up Tor, and you won’t suddenly see the dark web staring back at you. Not only do you need a dark web browser, you need a dark web search engine too. This search engine will get you to the sites you need, though you can also go directly to dark web addresses if you know what they are, as with standard URLs.



