So, it’s only natural to find ways to keep in touch with your darknet buddies and/or customers. There are several email and IM services which you can use, and it’s highly recommended to pick one if you want to step up your dark web game. You should stay away from everything labeled “porn”, “card skimming services”, “PayPal hacks”, “firearms”, “real fake IDs and passports”. Believe me – there are plenty to go around and each and every one of them are being kept under surveillance. Not to mention the fact that you’ll get exposed to some stuff that will definitely make you take several cold showers.
Is AliExpress Legit And Safe To Use In 2025?
You can never be sure who’s really behind the other end of the line. These high levels of anonymity increase the opportunity for the “bad guys” to sell drugs, stolen IDs, credit cards, weapons, and many more compromised products or information. Next, disable Javascript in your Tor browser to prevent malicious scripts from attacking your browser sessions.
If you choose to visit the dark web, you must take the necessary measures to protect your privacy and security. The hidden web (also known as the deep web or deep net) is the largest part of the internet. It comprises websites that aren’t easily accessible mainly because they are non-indexed, password-protected or paywalled. The dark web is a small subset of the deep web comprising purely non-indexed websites and services. Being hidden doesn’t translate into being completely protected from the possibility of tracking, or, when it comes to illegal activities, of risk.
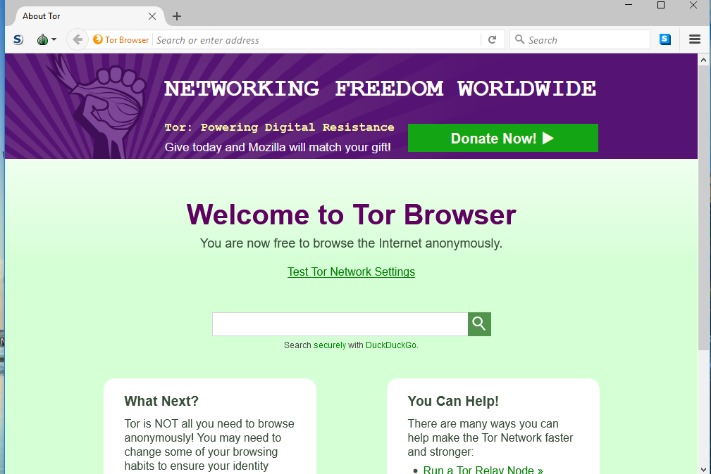
The Safer option disables all potentially dangerous website features, while the Safest option enables only the features necessary for basic website functions. By default, Tor has stricter privacy settings than most standard web browsers. Users can take further steps to maximize privacy when browsing with Tor. To use a new circuit, click the circuit button next to the domain. Then, click on New Tor circuit for this site, as illustrated below.
- You can also find a few free VPN services, but be aware of the risks if you’re still using legacy VPNs in your organization.
- ProtonMail is a Swiss-based email service that is very easy to use.
- Accessing it without proper protection exposes you to surveillance, tracking, and potential security risks.
- DuckDuckGo is the best dark web search engine, as it offers an excellent user experience akin to surface web search engines.
- This dual layer of security allows you to explore the dark web with confidence.
- No, simply accessing the dark web using Tor or other anonymizing browsers is not illegal.
Secure Your System And Mental Well-being
This is a great way to improve your privacy because Tor isolates each website you visit, meaning third-party trackers and ISPs can’t reveal your identity. Established in 2012, the platform is a time capsule that collects snapshots of websites. These onion addresses will remain online even if the original page disappears. It also keeps the graphical copy and text of the page for better accuracy.
Myth 4: The Dark Web Is Inherently Dangerous To Visit
These browsers offer the best security and privacy for browsing the dark web on mobile devices. The dark web is full of malware, phishing scams, and other malicious threats that can compromise your device and personal data. Cybercriminals often disguise harmful files as legitimate downloads, making it easy to get tricked. However, since iOS browsers are required to use WebKit (Apple’s built-in web rendering engine), the Onion Browser doesn’t have the same level of privacy as the Tor Browser on desktop or Android. To ensure your traffic is properly routed through the Tor network, you’ll also need to install Orbot, which helps secure and anonymize your connection.
Caution: Safety Comes First When Visiting Dark Web Links

If you want to mitigate that possibility, downloading a VPN is the best way to do so – it funnels your traffic through a private server and keeps your IP address hidden. There are plenty of services that offer a VPN over onion feature, which will keep you secure and private online. The dark web presents various threats, including malicious software and computer viruses, posing risks to users’ systems and data security. Users also face the potential danger of government monitoring and surveillance — or scams and fraud, and other activities that can lead to financial loss and identity theft. Dark web browsing is not as simple as regular web surfing, but there are some tools you can use to chart your journey.
HTTP Vs HTTPS: What Are The Differences To Know?
You can also find email messages, online bank statements, and much more information on the deep web – information that is usually private and inaccessible by the public on the surface web. Pixel Privacy believes in digital privacy and does not believe in using it for heinous and/or illegal activities, and so the focus of this article will be on legal activities. Be aware, however, that there are sites for absolutely everything, from the benign to the very illegal. There are some websites you can absolutely get in legal trouble for even visiting, so proceed with the utmost caution.
Find The onion Address You Want To Access
Just remember, if you want to explore the dark web, be very careful. This allows you to use the computer without the risk of corrupting your computer’s normal operating system with viruses or malware. Tails also protects you from possible malware, viruses, or keystroke loggers that may have already infected the computer, as it doesn’t run the operating system already installed on the device. The advantage of using a dedicated computer just to browse the dark web is that your main computer isn’t exposed to any of the threats or risks tied to entering the dark web. In case of an attack, you can be sure that any of the data or information stored on your main computer will be safe.

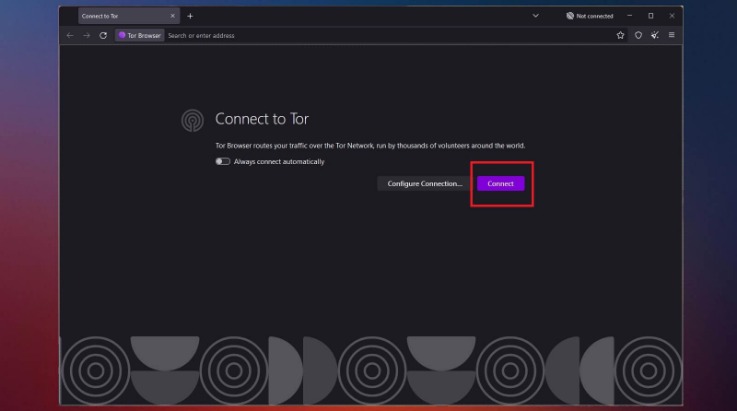
As explained earlier, you won’t be able to access the dark web the same way you would the surface web. You can’t type dark web addresses into your usual browser or search for them via Google. Instead, you have to use a specialist browser, designed to navigate the dark web. A phishing website or link is one that appears legitimate but is actually a trick designed to make you hand over your personal information to hackers and other bad actors. Often, these sites are made to look just like real, trusted platforms, such as banks, social media sites, or email providers.
Lewis points to the “first contact problem”, when an attacker spots when someone moves from non-private tools to private ones, noting it’s been used to identify whistleblowers. Your traffic is relayed and encrypted three times as it passes over the Tor network. The network is comprised of thousands of volunteer-run servers known as Tor relays. This internet space can be dangerous but you can safely get on it by using a VPN and then connecting to Tor.
One more thing before we move on – accessing the dark web is LEGAL. Selling drugs or hiring a hitman to kill your ex will get you into trouble. However, you can browse forums, watch videos, and chat with other people just fine. Browser fingerprinting and online tracking are virtually impossible when you’re connected to the dark web via Tor Browser. That means your browsing behavior and traffic patterns can’t be collected and sold by data brokers or used by third-party advertisers. Others were casual users—people buying fake IDs, stolen credit card numbers, or drugs.
Here’s a step-by-step guide to setting up Tails on a USB thumb drive and using it to access Tor. Whether you’re a journalist, a privacy advocate, or just curious, this guide will walk you through how to access the dark web safely and responsibly. Buy login credentials to a $50,000 Bank of America account, counterfeit $20 bills, prepaid debit cards, or a “lifetime” Netflix premium account.
- Malware, ransomware, and hacking tools are widely sold in underground forums.
- It might sound weird that Google doesn’t index these pages, but it does carry some logical sense.
- Finding these can prove a challenge, as searching on the dark web can be irritation – visually and operationally.
- In this instance, too, it is important to use a logless VPN and pay with Bitcoin if you can to stay anonymous.
- When you use the Tor network, your traffic is layered in encryption and routed via a random relay, where it’s wrapped in another layer of encryption.
So, even though it does exist on the internet, Google doesn’t index any of these pages or content. Microsoft Word is one of the best word processors around, allowing you to craft powerful documents with an intuitive interface. If you know how to use Microsoft Word, you’re typically working with large files that span multiple pages.

Each address also contains cryptographic information that enables a dark web browser to connect to the site. That allows .onion sites to be accessible anonymously without services like DNS. The dark web is a murky part of the internet that isn’t accessible via a normal browser — and can be dangerous to visit if you don’t know what you’re doing.
This could include sites not automatically available to the public, such as those which require a password. Examples of this might be e-mail accounts or registration-only forums. Why else would the police in Brazil, Germany, and the United States need to raid dark web e-shops like the Wall Street Market and the Silk Road? Charging the operators with a long grocery list of crimes ranging stolen data, drugs, and malware. These things do happen on the dark web, but they are one piece of the jigsaw. Content on the Dark Web exists on overlay networks that use the Internet and special tools and configurations to sustain security and privacy.
I possess a keen interest in exploring and understanding the intricacies of malware, Advanced Persistent Threats (APTs), and various cybersecurity challenges. My dedication to continuous learning fuels my passion for delving into the complexities of the cyber world. Well, there’s a reason why it’s recommended to browse with a minimized or rescaled window – you can be tracked based on your active window’s dimensions (yeah, they really can do that). So, do yourself a favor and rescale that Tor window as much as you can before proceeding. We already went through VPNs, anonymizing web browsers, and disposable operating systems, so I won’t bother reminding you about those.



