This includes your email inbox, online banking dashboard, private cloud storage, and even internal networks like an intranet. Many people use Tor to avoid surveillance by government agencies, ISPs, or other entities monitoring online activities. Similarly, people in countries with strict internet access and usage regulations must use Tor clients or virtual private networks (VPNs) to access some public websites. This portion of the internet can be accessed using search engines such as Google, Bing, or Yahoo.
Social Media Algorithms: How They Control What We See
Keep in mind that you’ve to use very specific keywords when searching. And most importantly, be patient as you’ve to sort through a lot of useless results. These search engines work best if you already know what site you’re looking for, not for general browsing. Just like Google, the dark web has some search engines present on it. Though they have their limitations, most of the time you’ll see irrelevant or spammy links for your search results. Established in 2012, the platform is a time capsule that collects snapshots of websites.
Understanding The Dark Web: Privacy, Security, And Legal Concerns
These services are used to obfuscate the origins of cryptocurrency transactions, making it harder to trace them. Users can mix their digital currencies to break the connection between the sender and the receiver. While visiting any of the sites you find on those Wiki sites, do not maximize your browser, as it can help identify you by your monitor resolution. Despite its legitimate uses, cryptocurrency’s untraceable payment nature has raised concerns around money laundering and illicit trade, driving regulatory scrutiny.

If you need a way to organize as an activist or you want to discuss censored topics with others, my first suggestion is to stick to offline meetups. The second, less secure option is to use encrypted messaging apps with ties to specific non-profit or activist organizations. For example, Briar is an extremely private chat app designed to help journalists communicate anonymously with sources. Signal is our Editors’ Choice for private messaging apps because it does a great job of blending privacy and social media functionality for a highly customizable chat experience.

Illegal Streaming Sites
Therefore, you should stay cautious and avoid clicking when accessing the dark web. Doing so will protect you from accidentally accessing illicit content or becoming a victim of malware. Additionally, much of the materials on the dark web are illegal, and unknowingly downloading such content can implicate you in criminal activities punishable by laws. If your device is infected with malware, read our guide to remove malware from your computer.
Your Data Can End Up Landing Anywhere

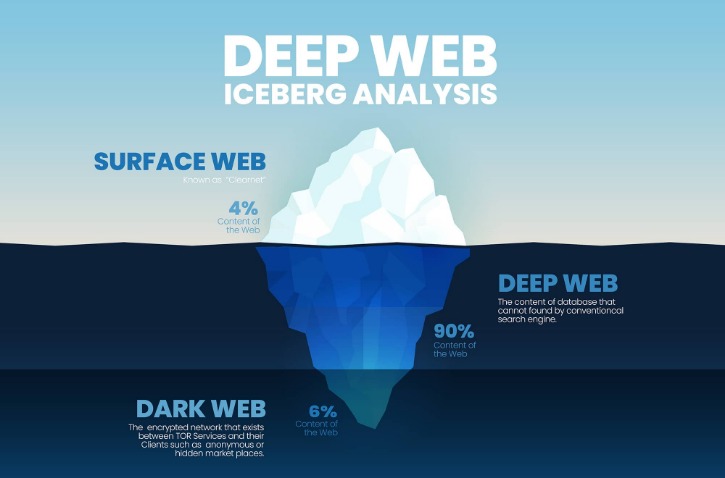
The area of the internet we access daily is known as the clear or surface web. The internet opened the door to a realm of possibilities that permanently changed the business landscape and our personal lives. In a world of bulk data collection, surveillance, and personalized ad tracking, it’s up to us to take control of our personal privacy. This information can be used to target ads and monitor your internet usage. Also, there’s a vast amount of unsavory content on the dark web, as well as a significantly high number of hackers and scammers looming on the platform. This type of government surveillance applies mostly to countries with environments that are hostile to free speech.
Tor Browser’s Great – But For More Complete Privacy Protection, You Need To Add This
As well as the bad, there is also good (or at least, safe) to be found on the dark web. That groundwork was the basis for the Tor Project, which was released in 2002 and launched a browser in 2008. With the creation of Tor, users could now browse the internet completely anonymously and explore sites that were deemed part of the “dark web.”
So, is the dark web a lawless underworld or a misunderstood frontier for privacy and free expression? Deep sites also include company intranets and governmental websites, for instance the website of the European Union. You may be able to search such pages but you do so using their own internal search function, not a search engine like Bing or Yahoo. If you log into personal accounts on the dark web or visit websites with tracking scripts, then your activity may be tracked. Similarly, unless you’re using a VPN, your IP address will be visible to the first relay node you connect to. Regular dark web visitors know that it’s possible to exploit the sketchy reputation of the space and the services offered.
Use Encrypted Communication Tools
The platform is protected from government interference and malicious attacks to protect the user. Unlike other search engines, it does not collect or share web activities and personal data of users. There are multiple search engines on the dark web that can help you find what you’re looking for. DuckDuckGo’s no-track dark web search service can be accessed in the Tor browser and is an excellent resource for information about the dark web. If your work or lifestyle requires you to use the dark web, however, there are ways to protect yourself. Just as you need the right tools to access the dark web, you also need the right protections to be able to stay safe on it.
These techniques, over time became public and thus led to the emergence of the hidden networks. As the features of dark web tools developed, the criminal mind saw the possibility of anonymous trade, leading to markets. Another challenge of finding dark web sites is that they don’t often last long. Many sites become defunct quickly, either because they are shut down due to illegal activity, their founders lose interest, or they change addresses and names to avoid detection.
It allows you to search for images, maps, files, videos, social media posts, and more. This means you can visit the site anonymously using the Onion browser, especially if you live under an oppressive regime. Since Hidden Wiki maintains all kinds of websites, ensure you don’t open something you don’t want to see. Even without monitoring your browsing activities, DuckDuckGo will offer decent answers to your questions. A VPN will mask your location and stop the online breadcrumbs that can lead back to you.
- The dark web refers to a concealed part of the internet that cannot be accessed through standard web browsers like Chrome or Safari.
- Obviously not all Tor users, but you never know whether someone might be looking into you.
- However, new technology like encryption and the anonymization browser software, Tor, now makes it possible for anyone to dive dark if they’re interested.
- This dark web monitoring will help you track illicit activities and minimize the risks of cyber-attacks.
- The Tor network began as an anonymous communications channel, and it still serves a valuable purpose in helping people communicate in environments that are hostile to free speech.
The sharing of illegal pornography and discussion of illegal sex acts account for a significant portion of dark web traffic. The extent of the problem became clear in 2015, when the FBI shut down a dark web site on Tor named Playpen that hosted 23,000 sexually explicit images of minors. Not all mass thefts of data facilitated by the dark web have been motivated by money. The publicizing of Snowden’s actions led to a global spike of interest in Tor and a resulting rapid expansion of the network’s user base.

Keep yourself informed about the latest security tips and potential risks by following cybersecurity blogs or forums. Agencies also trace crypto transactions, scrape data from seized servers, and sometimes deploy malware to reveal users. In short, you can get some privacy, but you can’t get total anonymity. If you’re doing something illegal, there’s a real chance someone’s watching. The Hidden Wiki is a curated directory of .onion links that helps you find popular sites quickly. It organizes links by category, like forums, email services, blogs, and file-sharing tools, which makes browsing easier and more efficient.
CISA 2015 Cyber Threat Info-sharing Law Lapses Amid Government Shutdown
Instead, users must use specialized browsers designed to provide a high level of anonymity. Using a dark web-specific browser such as Tor or I2P itself is legal in virtually all countries. But using these tools for illegal purposes constitutes a criminal act either way. In your browser settings (like the NoScript extension in Tor), you will want to disable JavaScript and other active scripts.
The dark web is a hidden part of the internet that requires specialized software like the Tor Browser to get access. Unlike the surface web, which consists of websites indexed by search engines, dark web websites are not searchable through standard browsers. It operates on a separate network that anonymizes users by routing their traffic through a series of encrypted servers, making it difficult to trace activities or identify users.
Staying Cautious And Protecting Your Information On The Dark Web
Corporations and governing bodies alike currently participate in unauthorized surveillance of online activity. Some simply don’t want government agencies or even Internet Service Providers (ISPs) to know what they’re looking at online, while others have little choice. Users in countries with strict access and user laws are often prevented from accessing even public sites unless they use Tor clients and virtual private networks (VPNs).
Illegal cyber activity cannot necessarily be stumbled upon easily but tends to be much more extreme and threatening if you do seek it out. Before we unpack the dark web’s threats, let’s explore how and why users access these sites. “The true value lies in proactive dark web monitoring to identify compromised credentials, leaked data, and emerging threats in real time. Equally important is maintaining strong operational security by using trusted Tor browsers, VPNs, dedicated devices, and disabling scripts that could expose identity,” says Currie. The primary gateway to the dark web is the Tor browser, which stands for “The Onion Router.” Developed by the U.S. Navy and released to the public in 2004, Tor is favored for its unmatched security and privacy features.
The dark web’s anonymity has also led to cybersecurity threats and various data breaches over the last few decades. Millions of regular internet users access private databases such as email inboxes and credit card accounts daily. These pages are not indexed by search engines and are protected behind security walls, authentication forms, and passwords on the deep web. The dark web is a small section of the internet intentionally hidden from traditional search engines and accessible only with special tools, such as the Tor browser. Unlike the surface web, which is open and indexed by search engines like Google, the dark web operates on encrypted networks that provide a high level of anonymity. The privacy offered by the Tor browser is important in the current digital age.