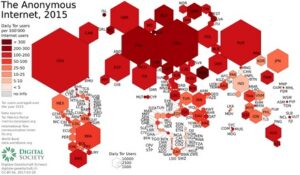
It aims to preserve the internet’s scientific and cultural heritage. SecMail is one of the most popular email services on the dark web. While this is not much compared to standard email services, it is enough for PGP-encrypted messages. The BBC news website has a special .onion site, which you need to access via the dark web. Its goal is to offer anonymous access to the content without being censored, no matter where you live. The good news is that the BBC Onion site is an international edition.
Plus, the ISP won’t see that you’re using Tor, which is excellent. We also prefer this method because of VPN’s all-encompassing security. The entry node encrypts your traffic and it bounces across several nodes in the Tor networks until it reaches the exit node.
Unfortunately, it requires you to have an invitation code to create an account. This means you have to know someone who is already using the platform. Even without the code, you can visit the security section to get tips on improving your daily life privacy. It allows you to search for images, maps, files, videos, social media posts, and more. It aims to advance research on terminal illnesses like cancer with access to unbiased scientific publications.
- Ruheni explains complicated technical concepts clearly and simply.
- In fact, create new throwaway accounts and documents if possible.
- Unlike traditional browsers, this will route your internet traffic through an anonymising network and mask your IP address.
- Before accessing the dark web, install strong security software to help keep your device protected.
Not only do you need a dark web browser, you need a dark web search engine too. This search engine will get you to the sites you need, though you can also go directly to dark web addresses if you know what they are, as with standard URLs. Cybersecurity has to also cover everything physically on your computer too—which law enforcement or government authorities might have the right to seize if they come calling.
- Charging the operators with a long grocery list of crimes ranging stolen data, drugs, and malware.
- This scale is why newspapers and mainstream news outlets regularly trot out scare stories about ’90 percent of the internet’ consisting of the Dark Web.
- It then depends on you, as the user, how you surf the dark world.
- We also prefer this method because of VPN’s all-encompassing security.
- Although the underground internet world is rife with everything bad, it also hosts positive elements.
Marketplaces & Forums
This is because law enforcement often actively monitors these sites. You risk being targeted for attacks if you explore the dark web without protection. The threat can extend to your entire network of devices connected to the internet. Many dark net sites do not undertake the necessary measures to protect users like most websites on the surface web. As a result, you can be exposed to different malware types, including botnets, ransomware, keyloggers, and phishing. These sites are a hybrid tutorial-underground where wannabe hackers ask questions and professionals sell their services or stolen data.
And yes, unfortunately, those seeking to perform criminal acts also use it. Follow this step-by-step guide carefully to ensure safe, anonymous, and secure access to the Dark Web using Tor. Understanding the Dark Web and its access tools, such as Tor, is crucial for anyone considering exploring these hidden parts of the internet safely and responsibly. To help find functioning .onion URLs, look to dark web directories and forums — Reddit users recommend tor.taxi, tor.watch, daunt.link, or one of the Hidden Wikis. Install Norton 360 Deluxe to help secure your device, block scams, and stay private online.
Legitimate Use Cases For The Average User
There’s no broad consensus on dark web safety, but you at least need to use Tor and VPN together. Once you have those, there are several ways to tunnel through the dark web. Read our posting guidelinese to learn what content is prohibited.
Beyond this “surface web” is the deep web, and within the deep web is the dark web. Then, use data breach monitoring software to help find out if your personal data has leaked onto the dark web. While accessing the dark web isn’t necessarily wrong or illegal, it’s important to know how to navigate this part of the internet safely.

Is It Illegal To Visit The Dark Web?

As explained earlier, you won’t be able to access the dark web the same way you would the surface web. You can’t type dark web addresses into your usual browser or search for them via Google. Instead, you have to use a specialist browser, designed to navigate the dark web. As a general rule, never download anything at all from the dark web. There are all sorts of threats on the dark web, and it’s all but impossible to verify whether a file is legitimate, so you’re likely to inadvertently download malware to your device. A phishing website or link is one that appears legitimate but is actually a trick designed to make you hand over your personal information to hackers and other bad actors.
Surfshark supports unlimited simultaneous connections to protect as many devices as possible. Also, try its services risk-free with the 30-day money-back guarantee. A budget-friendly VPN service allowing users to access dark web safely anytime, anywhere, and on any number of devices they want. Unfortunately, others are fake and fraudulent websites that exploit the reputation of the dark web to con people.
How To Get On The Dark Web Using Tor Browser
Check onion links through trusted directories, user reviews, and reputation checks. Use directories like The Hidden Wiki or Dark.fail, which list verified and regularly updated onion links. Install Tor Browser from the official website, adjust security settings to “Safer” or “Safest,” and only use trusted onion links from verified directories. For journalists, students, researchers, and security professionals, it’s a powerful tool when used ethically and safely.
Advantages Of VPN Over Tor
This will allow you to take action right away and reduce the risk of any further damage to your data or identity. As well as phishing scams, a multitude of other scams operate across the dark web. There are many fake marketplaces and platforms that might offer to sell you goods or services but actually take your money without providing anything in return.
The Ultimate 2025 Guide To The Tor Browser
The Tor browser routes your online requests through multiple nodes to obscure them from prying eyes. It conceals your location and other personal data that are exposed when using standard browsers. While often used interchangeably, Tor and Tor Browser aren’t the same thing. Tor is a network designed to route traffic through multiple servers.
How To Access The Dark Web On A Phone (Step-By-Step Guide)

You’ll need a purpose-built browser that uses The Onion Router (TOR) to access dark web content. Because of their anonymity, dark web sites are breeding grounds for illegal activity and transactions. On the other hand, the dark web hosts marketplaces and forums where illegal goods and services—such as drugs, weapons, and stolen data—are traded, making it a hotspot for criminal activity. Despite its negative reputation, not all activity on the dark web is malicious; some users rely on it as a tool for freedom of expression or to circumvent restrictions. These platforms provide services related to illegal activities, such as hacking tools, malware, ransomware, or services for hire (e.g., DDoS attacks, identity theft).
While Tor offers anonymity on the dark web, your online activities leave breadcrumbs that can reveal your identity. That is why you should only use a reliable VPN like ExpressVPN or NordVPN for additional security and privacy. With rising online privacy concerns in the current digital age, the Tor network’s anonymity is becoming essential. It is a good way to prevent third parties from tracking online activities. People in countries with heavy internet censorship must get a VPN or Tor browser to access the surface web.
Is The Tor Browser Safe Without A VPN?
Imagine a vast, shadowy expanse of the internet where the usual search engines dare not tread — this is the dark web. It’s a hidden layer of the internet, shrouded in secrecy, that you can’t access using traditional search engines like Google or Bing. Unlike the websites you browse daily, the dark web requires special tools to access and explore. It’s like a secret alleyway (say Diagon Alley from “Harry Potter”) in the sprawling city of the internet, known only to those who seek it out. Tor over VPN requires you to place some trust in your VPN provider but not your ISP, and is best if you want to access .onion websites. VPN over Tor requires you to place trust in your ISP but not your VPN and is best if you want to avoid bad Tor exit nodes.
Deep sites also include company intranets and governmental websites, for instance the website of the European Union. You may be able to search such pages but you do so using their own internal search function, not a search engine like Bing or Yahoo. This means content of such sites isn’t accessible to web crawlers.

Malicious actors and government agencies can run Tor nodes, compromising privacy and security. In fact, there have been instances where attackers controlled hundreds of Tor nodes. Law enforcement agencies in many countries monitor the dark web to combat illegal activities.