By following these steps, you can better protect your identity and maintain anonymity while exploring the Dark Web. However, it is important to note that no method is foolproof, and it is essential to exercise caution and be mindful of the risks involved at all times. Law enforcement agencies, intelligence agencies, and hackers frequently monitor activities on the Dark Web. While it is difficult to trace users, there is always a possibility of being identified and targeted.
The content in this article is for general information and education purposes only and should not be construed as legal or tax advice. Stripe does not warrant or guarantee the accuracy, completeness, adequacy, or currency of the information in the article. You should seek the advice of a competent lawyer or accountant licensed to practise in your jurisdiction for advice on your particular situation. On the other hand, Litecoin and Dash will take their place next to Bitcoin as the everyday payment currencies of the dark web. At the same time, as these currencies become more readily available to a general population, malicious tools such as ransomware will also continue to evolve to take advantage of the mainstream trend. And with almost £2 billion lost to cybercrimes last year according to Action Fraud, people are being asked to stay vigilant to protect their money.
Looking ahead, the future of cryptocurrency on the dark web remains uncertain, with a growing number of hackers and an expanding accessibility to the dark side of the internet. As the dark web grew in popularity, so did the interest of malicious actors looking to exploit its anonymity and conduct illegal activities. The rise of the dark web has created a haven for hackers, who use cryptocurrencies as a means to facilitate their nefarious activities. With the increasing availability of hacking tools and tutorials, more individuals are gaining access to the dark web, making it a breeding ground for cybercrime. With the increasing adoption of privacy coins like Monero, the dark web has witnessed a shift towards more non-traceable transactions.
Step 4: Maintain Strict Operational Security (OPSEC)
This level of anonymity enables credit mules and network administrators to operate with reduced risk of detection. In the murky depths of the Dark Web, where illegal activities thrive, cryptocurrencies have emerged as the preferred payment method. With their decentralized nature and pseudonymous transactions, cryptocurrencies offer a level of anonymity that traditional payment methods simply cannot match. This has made them the go-to option for those seeking to conduct illicit transactions on the Dark Web, such as purchasing drugs, stolen data, or even hiring hitmen. In this section, we will delve into the reasons why cryptocurrencies have become the currency of choice on the Dark Web, exploring their advantages and drawbacks from various perspectives. The dark web has become a breeding ground for cybercriminals looking to profit from stolen credit card information.
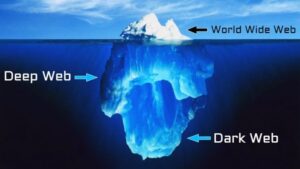
What Is The Dark Web And Why Is It Illegal

It’s important to note that the Dark Web can be a dangerous place, so exercise caution and follow best practices to protect yourself. Stick to reputable sources and communities to reduce the risk of encountering malicious actors or falling victim to scams. Additionally, many online merchants provide a specific webpage for gift card balance checking. These typically don’t have the same level of security protection as do credit card pages, so they can be easily abused by card cracking bots. Regarding the infrastructure of the dark web, it operates on hidden networks or darknets.

The Benefits Of Adopting The SBD As A Digital Payment MethodOriginal Blog
The record that a store uses is collected and can be accessed by banks, the company itself, or the government. This is why I recommend using it alongside one of the anonymous payment methods I discussed above. A virtual card generates a unique, temporary card number for online payments, so you don’t have to use your actual credit or debit card. Typically, you load funds into your virtual card account and then create a disposable card that draws from this balance. They might not be great for long-term purchases, though, since there are typically fees involved with loading or using a prepaid debit card.
The Dark Side Of Digital Currency: Money Laundering On The Dark Web
It is challenging to verify the credibility and legitimacy of sellers, putting buyers at a high risk of being scammed. The purpose of the Dark Web was originally to protect the privacy and security of individuals, especially those living in oppressive countries or engaging in whistleblowing activities. However, it has since become a thriving hub for illegal activities, including drug trafficking, hacking, counterfeit goods, weapons sales, and even hiring hitmen. Credit cards, Paypal accounts, and fullz are the most popular types of stolen information traded on the dark web, but they’re far from the only data worth stealing. Sales of passports, driver’s licenses, frequent flyer miles, streaming accounts, dating profiles, social media accounts, bank accounts, and debit cards are also common, but not nearly as popular. Hijacking a PayPal account requires a different approach than stealing a credit card number.
Card Phishing Phone Calls And Emails
Without a proactive cybersecurity strategy, businesses risk severe financial losses, reputational damage, and even legal repercussions due to compliance violations. For instance, some members might discuss the advantages and disadvantages of using physical card cloning versus card-not-present (CNP) fraud. While physical card cloning involves creating a counterfeit card using stolen information, CNP fraud typically involves making online purchases using stolen credit card details. By weighing the pros and cons of these methods, participants can determine the most effective approach for their specific circumstances. Cryptocurrencies, such as Bitcoin, Ethereum, and Monero, provide users with a certain level of anonymity. While transactions are recorded on a public ledger, the identities of the parties involved remain concealed behind complex cryptographic addresses.
Also, some vendors may require registration or personal details for online reloading or higher balances. If you want complete and total privacy, cash or gift cards are your best options — they don’t require any personal information at all. Some businesses also accept cash-by-mail, which lets you pay for online goods anonymously without needing a return address. The ease of access and navigation of Telegram carding groups is a major concern, as it allows cybercriminals to easily buy and sell compromised payment card details. Stolen credit card details can be categorized into different types, making it easier for cybercriminals to exploit them. Now that the transaction is complete, let’s explore the crucial aspect of dispute resolution with escrow services on the Dark Web.
HUMAN Protects Against Carding Attacks
Card data on the dark web is a valuable commodity, and it’s often sold on specialized marketplaces known as Card Shops. These platforms are hubs for cybercriminals to buy and sell compromised payment card details. Leaked credit cards from Telegram channels account for the overwhelming majority of compromised payment card details. These platforms serve as hubs for cybercriminals to easily buy and sell compromised payment card details, including credit card numbers, CVV codes, expiry dates, and cardholder information.
Activities On The Dark Web
- A second major leak of cards relating to Indian banks has been detected by Group-IB, with over 1.3 million credit and debit card records being uploaded to the Joker’s Stash marketplace.
- Governments are implementing stricter regulations, mandatory reporting, and Know Your Customer (KYC) policies to curb money laundering and illicit transactions.
- Card checkers are tools used by threat actors to verify the validity and authenticity of credit card information they purchase on the dark web.
- TheZ-NFC Card Emulator is an NFC card emulator that leverages Android’sHost Card Emulation (HCE) capabilities.
- However, despite the evolving technology around them, checks have not evolved much over the years, making them more vulnerable to fraud.
Unauthorized charges were not blocked for 81% of users who didn’t have the alerts turned on. FasterCapital is a global venture builder and online incubator dedicated to co-funding and co-founding innovative startups. Established in 2014, we are now #1 venture builder in terms of number of startups that we have helped, money invested and money raised. However, checks can take several days to clear, and there is always the risk of them being lost or stolen. In addition, many merchants no longer accept checks, so it is important to check with the merchant before attempting to pay with a check. When you know your medical coverage, you’ll be able to make informed decisions about your healthcare.
Before entering dark web transactions, you should be aware that cryptocurrency is the preferred payment method for many cybercriminals. Its decentralized nature allows for high anonymity, making it an ideal choice for illicit trades. Bitcoin, Ethereum, and other alternative coins facilitate quick transactions while masking the identities of users, which is important in maintaining the secrecy of illegal activities.

While Bitcoin transactions are publicly recorded on a blockchain, users can still conduct transactions pseudonymously, without directly revealing their personal identities. This basic level of anonymity, combined with widespread acceptance and accessibility, makes Bitcoin the most popular cryptocurrency for dark-web payments. On the dark web, cryptocurrency has become the preferred method of payment due to its promise of enhanced privacy, reduced traceability, and resistance to conventional surveillance.
Bitcoin has become the preferred currency on the dark web due to its pseudonymous nature, allowing users to make transactions without revealing their true identities. For cybercriminals, stolen data is a valuable asset, fueling identity theft, financial fraud, and corporate espionage. A single compromised credit card can be sold for as little as $10, while full identity profiles—often called “fullz”—can fetch hundreds of dollars. Businesses face severe consequences when their data is leaked, from regulatory fines under data protection laws to reputational damage that erodes customer trust.

This eliminates the need for intermediaries and reduces the risk of detection by law enforcement agencies. Additionally, Bitcoin transactions can be made with a certain level of anonymity, as users can create multiple addresses to obfuscate their identities. The decentralized nature of bitcoin makes it difficult for authorities to track and seize funds involved in cybercrimes on the dark web. Traditional financial institutions are not involved in bitcoin transactions, making it harder for law enforcement agencies to trace the flow of funds. Moreover, mixing services and tumblers further obfuscate the transactions, making it challenging to identify the parties involved. Another type of scam involves fake websites or marketplaces that offer illegal goods and services, such as drugs, weapons, or stolen credit card information.

Exploring the realm of credit card transactions on the Dark Web is a journey into a dangerous and illegal world. While the allure of cheap credit card details and the potential for financial gain may be tempting, the risks and consequences of engaging in such activities cannot be ignored. It is important to note that engaging in transactions on the Dark Web carries significant risks, and using payment methods that cannot be traced back to the buyer does not guarantee complete anonymity. Despite the pseudonymous nature of cryptocurrencies, law enforcement agencies and cybersecurity experts have developed sophisticated techniques to trace these transactions. Buyers must navigate through a labyrinth of fraudulent sellers and law enforcement operations targeting illegal marketplaces. It is crucial to exercise caution and take protective measures to safeguard personal information.