The hope is that everyone can use advanced technology like artificial intelligence (AI) responsibly, but this simply isn’t the reality. Businesses must prioritize cybersecurity by implementing Dark Web scanning tools, strengthening access controls, and educating employees about emerging threats. Identifying security vulnerabilities before cybercriminals exploit them is essential for maintaining operational integrity. Despite using a VPN, there’s always a risk of the VPN leaking your IP address through DNS or WebRTC leaks or misconfigurations when on a dark web forum or marketplace. Therefore, you must run an IP leak test to ensure that the VPN is working completely fine and is not risking your digital security.
These platforms sell everything from drugs and fake IDs to weapons and hacking tools, resembling a digital black-market bazaar. Purchasing and using fake IDs or fraudulent documents from the dark web is a high-risk endeavor that carries severe legal, technical, and ethical consequences. Although counterfeit documents might initially seem attractive due to perceived convenience or anonymity, the dangers far outweigh any temporary benefits. Users face significant legal penalties, including hefty fines, criminal charges, imprisonment, and permanent damage to their personal and professional reputations.
Tor2door Market
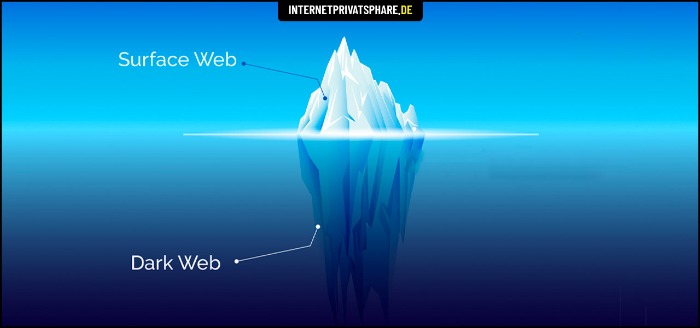
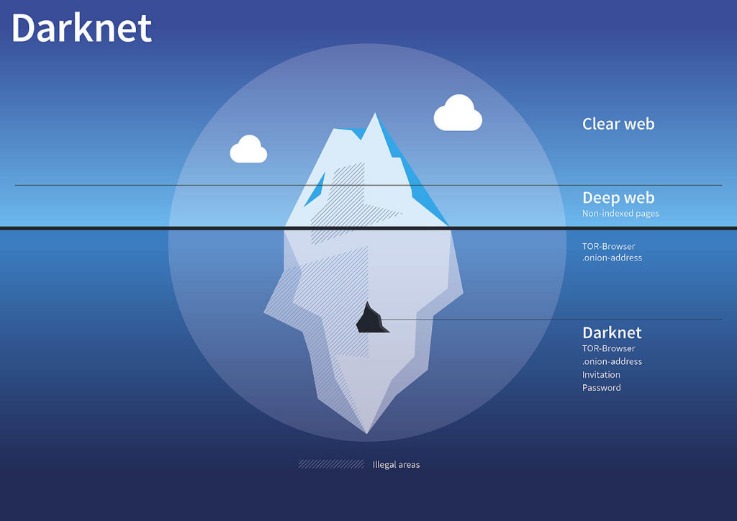
In the Welcome to Video case (2019), investigators traced Bitcoin transactions directly from the dark web back to individuals across the globe, resulting in hundreds of arrests and convictions for illegal activity. During the investigation, law enforcement seized cryptocurrency valued at $75 million at the time of the seizures, as well as cash and precious metals. That is the easiest way for a hacker to gain access to your accounts. Old accounts can be compromised and used for password resets or similar attacks. The darknet is basically an overlay network that exists within the internet and can only be accessed with specific configurations, software, and usually uses certain customized communication protocols. The dark web is only accessible through specific software like Tor (The Onion Router).
Threat Brief: Escalation Of Cyber Risk Related To Iran (Updated June

In Texas, for instance, possession of a fake ID is a Class C misdemeanor, punishable by up to 180 days in jail and a $2,000 fine (Doug Murphy Law Firm, 2024). Producers face even stricter penalties, with the possibility of felony charges and prison time (Theoharis, 2024). Yet, the profitability of this underground economy allows it to persist.
Credit Score:
Its user base is primarily English-speaking, and it appeals to more sophisticated cybercriminals. Darknet traders don’t want full decentralisation — they want convenient anonymity with dispute resolution. That’s hard to get without some form of centralisation, which always becomes a target. Image of counterfeit ID card and underground economy tools Artificially generated image. A study by the National Library of Medicine found that 40.1% of underage college students owned or had owned a fake ID (IDScan.net, 2023). In addition to previous statistics, a 2024 report found that nearly half (45%) of U.S. young adults aged know someone who has successfully used a fake ID to access age-restricted products or venues (Scandit, 2024).
Optical Technologies And The War On ID Counterfeiting
Use anti-virus software such as AVG on your personal computer to scan for malware and make sure that it is set to update automatically. If you need to log in to an account on a network you don’t trust, such as a coffee shop, use a VPN to encrypt all connections. The high value of accounts combined with the abundance of BTC ATMs for anonymous cashing makes cryptocurrency accounts a very valuable target for hackers.
Here’s What Your Data Sells For On The Dark Web
Stick to cryptocurrency, avoid downloading anything, and don’t share any personal info. Book A Demo with AiPrise to see how the platform fits into your workflow and helps you stay secure and compliant. Once the identity becomes risky to use (e.g., flagged or reported), it’s either resold at a discount or discarded. Digital ID fraud happens when someone steals or fabricates personal data to impersonate an individual online. This could include their name, email, passwords, biometric details, or even device information. Ultimately, addressing fake document usage necessitates more than law enforcement—it requires broader societal reflection and moral education emphasizing integrity, accountability, and the importance of shared societal values.
Unlike the regular internet which has websites indexed and tracks where you go, this anonymous network keeps many criminals from being identified by encrypting their location and movements. A special browser, which you have to download, is needed to access it. Selling information for financial fraud and scams is one of the most rampant problems on the dark web, with Artificial Intelligence tools leading the way as one of the biggest threats.
By applying Becker’s framework and game theory to peer-driven college dynamics, future studies could provide valuable insights into risky behaviors and inform interventions designed to reduce harm while fostering safer social interactions. While some of these markets were shuttered by law enforcement agencies – some took the easy way out with exit scams. Here are some of the now-defunct dark web markets that were notorious for cybercrime. Others are looking for stolen data, hacking services, or even banned books and political content. For sellers, it’s often about making money while staying off the radar. By supplying stolen data, these dark web links fuel many online scams and identity theft operations, playing a critical role in the darker aspects of the internet.
- Let’s take a walk down the (encrypted) alleyway of darknet market evolution.
- Let’s get this straight — not everything on the dark web is illegal or harmful.
- It’s an ever-evolving ecosystem—constantly shifting, reinventing itself, and adapting.
- Tor encrypts internet traffic through multiple layers, making it difficult to trace users, while cryptocurrencies like Bitcoin and Monero enable pseudonymous financial exchanges, reducing the risk of detection by authorities.
- In 2013, the FBI shut down the Silk Road, but it was later relaunched in 2014 with the new name of Silk Road 2.0, but the German authorities shut it down in the same year.
- In the past, getting a fake ID that’s compelling enough to bypass identity verification and know-your-customer (KYC) checks has not been impossible, though it’s not always been successful.
Tracing Cryptocurrency Transactions
Just a few years ago, such a scenario would have been a far-fetched plotline reserved for the Netflix series “You”. But recently, the dark web has made it extremely easy for anyone wanting to start a new life to simply buy themselves a brand new identity. By leveraging automated dark web monitoring, organizations can mitigate risks, and take preventive measures before the leaked data is exploited. In addition to its emphasis on stolen credentials, 2easy Market offers a variety of cybercrime tools, such as hacking services, exploit kits, and other resources for conducting cyberattacks.
A woman in New Brunswick had her account hijacked; what started as a simple Facebook login ended with her friends being scammed out of thousands. The scammer used her digital identity by sending fake messages to her contacts, collecting payments fraudulently, and then disappearing without a trace. Additionally, communities facing rampant document fraud often see declining public trust in institutions, businesses, and even interpersonal relationships. When citizens perceive that fraud is widespread or tolerated, social cohesion weakens, damaging overall community resilience and stability.
Cybersecurity Awareness Explained: Importance & Best Tips 2025
The cost is higher if there is a confirmed high balance or if it is a premium card (platinum, business, corporate, gold). Some of the costs can be much higher if they come in a bundle and may also include how-to tutorials on making the most out of the credit cards to conduct fraud. Many of the credentials advertised for sale on the dark web are genuine — meaning they were stolen from a bona fide citizen and illegally sold to a new identity seeker. For over a decade, darknet markets have existed in a murky underworld of anonymity, cryptocurrencies, and illicit trade. From drugs and fake IDs to hacking tools and weapons, these marketplaces promised decentralised freedom from the oversight of banks, governments, and corporate middlemen. Launched in 2023, STYX focuses on financial crime, providing stolen credit card data, hacked bank accounts and access to various cryptocurrency laundering tools.
Germany’s Federal Criminal Police Office Takes Down Hydra Darknet Marketplace
The consequences can be lethal to those whose data is stolen, like identity theft, emotional distress, and even financial loss. Nevertheless, most of the items in the darknet markets are illegal or heavily regulated. In fact, according to a study that was done in 2020, over 57% of the websites found on the Tor network contained illegal content. Markets like AlphaBay and Hansa adopted stronger encryption and expanded offerings to include hacking tools and stolen data. However, these platforms often faced law enforcement takedowns, technical issues, or exit scams, where operators vanished with user funds.
- You’ve probably seen news feeds full of such headlines more than once, but where does all that stolen information go next?
- Creating a bank account starts at US$70, obtaining a new credit card starts at US$45, and the minimum cost of fixing credit history is US$200 — very low prices for some of the most important components of a person’s financial identity.
- When a hacker steals another person’s identity and resells it, the victim of the identity theft is left devastated — their bank accounts get depleted, their credit rating gets destroyed, and their lives become ruined.
- We recommend using NordVPN as it offers top-notch security features, including dark web threat protection.
- To expand their reach, some marketplaces established parallel channels on Telegram.
Want To Protect Your Business From Fraud?
The darknet markets are a hotbed for selling stolen personal information. The stolen data can be just anything from full names, credit card details, passwords to social media accounts, bank account information, and social security details, among others. In 2019, two illegal marketplaces called Richlogs and Genesis were identified for selling “stolen fingerprints” of 60,000 online users, giving the holder complete access to the victim’s online presence or web activity. The fingerprint details were mainly acquired through malware attacks, which provided Genesis operators with account passwords and full browser history. It is not a surprise to see ‘credit cards’ being sold in the darknet markets as they are further used to commit fraud and are also used by cybercriminals to finance their requirements and make profit.
Incognito’s got a slick vibe—easy to roam, packed with oddball stuff like hacked accounts. Takes Bitcoin or Monero, and last week I snagged a deal that shipped in three days flat. Archetyp’s all about the drug game—ships worldwide, keeps fees low (1-4%). Their anti-phishing tricks saved me once when a fake link popped up; the real site’s clean layout sealed the deal. While this topic may seem distant for most people, understanding how these spaces operate is crucial. It helps us stay more vigilant, better protect ourselves, and make informed decisions online.

All of this has made it one of the most reliable markets still active in 2025. Darknet markets are websites which are hosted on the deep-web and can be accessed typically using the Tor network. Fake IDs and fraudulent documents refer to identity materials produced or altered illegally, which are widely traded through the hidden marketplaces of the dark web. These counterfeit documents include driver’s licenses, state identification cards, passports, social security cards, birth certificates, visas, and even professional certifications or diplomas. The dark web, a concealed portion of the internet accessible only through specialized software like Tor, provides an ideal platform for such illicit trade due to the enhanced anonymity it offers buyers and sellers.



