For this reason, you cannot browse through these sites using your default search engine. You only need to upload your PGP key or let the platform create one. Use it to link your GitHub account, Twitter, Bitcoin address, and Facebook. This .onion link makes it impossible for hackers to impersonate your profile. Established in 2012, the platform is a time capsule that collects snapshots of websites. These onion addresses will remain online even if the original page disappears.
Step 5: Verifying Website Safety
However, there’s no guarantee that all the links on this site are working. Some may lead to malicious sites, downloading malware on your device. The Tor browser is the most preferred browser for surfing the dark web because it creates encrypted pathways for user traffic, ensuring all the activities are anonymous. Having trouble deciding what dark web sites are safe and reliable? For most people and use cases, using only a VPN will offer sufficient privacy with much faster speeds than Tor alone.
DuckDuckGo onion
It also keeps the graphical copy and text of the page for better accuracy. Unfortunately, it requires you to have an invitation code to create an account. This means you have to know someone who is already using the platform. Even without the code, you can visit the security section to get tips on improving your daily life privacy.
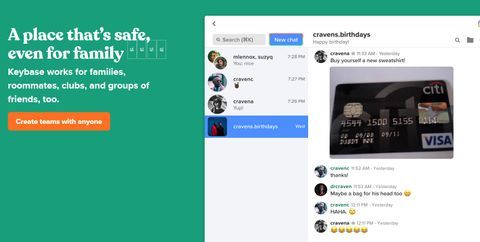
It is essentially a list of all the notable websites available on the Tor Network that is kept in a single, organized place. Your account must be older than 4 days, and have more than 20 post and 10 comment karma to contribute. Active for a decade since 2014, it is a widely used credit card shop used to source stolen credit card information such as dumps, CVVs, Wholesale Accounts. The Abacus Market links to the new dark web marketplace sections and took over much of the vacuum left by the AlphaBay takedown. If you ever decide to explore the dark web, protecting your identity is crucial. Most people start by using the Tor Browser, which hides your IP address.
Torzon Market
Cryptocurrencies such as Bitcoin have been the dark web currency even before they became available to the general public. Right now, you can use many cryptocurrency .onion sites to buy or sell all types of cryptocurrencies. This service is a good source of statistics if you have a school project requiring research on Tor and the dark web. However, note that the site only uses non-sensitive and public data for the metrics. In most cases, whistleblowers have sensitive information about the government or a company. They can be easily traced and even prosecuted if they share the information on the surface web.

Forums And Communities
The wallet is user-friendly and provides robust security, making it one of the best crypto wallets on the dark web. Finally, Wasabi Wallet is non-custodial, meaning you alone can access the encryption keys. Riseup is a dark web platform that offers secure messaging solutions. It does not store logs and is protected from interference and malicious attacks. The platform is free and is run by volunteers in the US who prefer privacy and security.
Hidden Cyber Risks Of Generative Artificial Intelligence
This is a great resource for users looking to refer to old prices or job listings that have changed or are outdated. This platform is a time capsule with content, primarily web pages. It saves a select version of each page and preserves it even after upgrades have taken effect on the original site. The site has a simple interface and offers filters to find books.
- It’s so secure and privacy-oriented that the Tor browser uses it as the default search engine.
- Of course, I absolutely don’t support underage (stuff) and illegal drugs, passport and stuff.
- It maintains a very strict level of user verification and integration with an official Telegram account to provide real-time updates to users.
- Other sites explicitly block search engines from identifying them.
- Their website is accessible on the clear web, but it also has a .onion site, allowing visitors to browse it anonymously, especially those living under oppressive regimes.
- You can easily find what you are looking for, even links to hidden dark web rooms.
We Helped Patch A Chromium Bug That Could Leak Your Real IP — Here’s How
It was originally launched in 2013 and, although it didn’t start with that name, it reinvented itself in 2018 right after one of its administrators was arrested. Since then, it adopted the name XSS, referencing the well-known Cross-Site Scripting vulnerability, and has established itself as a key meeting point for Russian-speaking hackers. Some users are looking to join ransomware groups, others brag about attacks they’ve pulled off, and some launch smear campaigns against rival forums.

Moreover, due to its popularity, many copycats of the Hidden Wiki exist. So don’t be surprised if you encounter different versions that claim to be genuine, and be very careful. Your best shot is to back up and secure vital information you have on your computer. If you’re paranoid-level cautious, pay a Cybersecurity expert to investigate your computer. When I first start taking harder drugs, I got everything from the deep web through a friend of mine who’d used it for a while and knew a lot about it.
It means you cannot access websites on the dark web with regular browsers like Firefox or Chrome. Instead, you need a specific configuration, software, or authorization, such as Tor, to access it. Blockchain even has an HTTPS security certificate for even better protection. RiseUp is a top dark web website that offers secure email services and a chat option. It was created in 1999 as a secure communication platform for people and groups working on liberatory social change. The platform is protected from government interference and malicious attacks to protect the user.
Some services are genuine; you can get what you want at an agreed fee. It’s important to note that although the dark web has many valuable services, it is also a hangout for cybercriminals. Furthermore, it’s critical to understand that Whonix is not a stand-alone browser. It is a component of Whonix, an operating system that functions as a whole inside a virtual computer. It includes all the essential productivity software, including MS Word and an email client. Be sure that your experience with Whonix will be comparable to Tor because both programs share the same source code.
This means your activities cannot be traced or your browser history exposed. The early version of Tor was created to mask spy communications. In due course, the framework was remodeled and made public as a secure browser. Initially, the dark web was mainly used by government agencies, big businesses, hackers, and cybercriminals. However, technological advancements such as encryption and privacy-focused browsers like Tor enabled the general public to access it. Some whistleblowers and journalists use these portals to safely leak information, especially when a source requires complete privacy.
When you first venture into the dark web, choosing the right search engine can significantly influence your experience. Here’s a clear overview of four trusted search engines that can help you navigate the hidden corners of the internet. Facebook is aware of attempts by many governments to restrict access to a tool that allows strangers across the web to talk and collaborate freely. While its .onion address doesn’t make it much easier to maintain an anonymous account, it does make Facebook more accessible in places where it’s censored. Russian Market has consistently remained one of the most popular and valuable data stores on the dark web. Its affordability and reliability have earned it a loyal customer base.
You can use Facebook’s services without exposing yourself to the company’s privacy-eroding tentacles. Secondly, if Facebook is blocked in your location, you can use the dark web Facebook mirror to circumvent the censorship. RAMP rose in popularity after the infamous Colonial Pipeline attack in the U.S.—an incident that triggered major tension across the dark web.