We also found that this mechanism should also include some sort of load balancing feature on the server side. We expect that most markets would implement this mechanism at the first point of entry to the site, but this is surprisingly not the case. Actually, CAPTCHAs could also have a somewhat protective effect on DDoS (which we describe in Sect. 4.1.4). Table 2 presents an overview of whether selected dark web markets implement specific web security mechanisms. Avoid links from forums or random websites, as these can lead to phishing, scams, or malware. It allows buyers and sellers to exchange messages securely, ensuring that sensitive details like delivery addresses or transaction confirmations remain private.
Is It Illegal To Access The Darknet?
When viewed through this lens, the dark web’s legality is based on how you as a user engage with it. You might fall to the wayside of legal lines for many reasons that are important for the protection of freedom. Others may act in ways that are illegal for the protection and safety of others. Let’s unpack both of these concepts in terms of the “dark web browser” and the websites themselves. Once access was granted, vendors and customers used Silk Road to make transactions with cryptocurrency or via an escrow (a trusted third party).
Legitimate Use Cases For The Average User

If your information surfaces in these murky depths, there’s very little you can do – but knowing the risks involved is a first step toward defence. The strategies used by law enforcement to dismantle these marketplaces involve a mix of advanced technologies and old-fashioned detective work. Advanced data analytics and powerful machine learning algorithms play an important role in tracking transactions and identifying patterns that point to illegal activities. On March 20, 2024, U.S., German, and Lithuanian law enforcement agencies seized Nemesis’ servers in a joint operation. Since the takedown of Nemesis, Parsarad has discussed setting up a new darknet marketplace to take the place of Nemesis with vendors that were once active on the marketplace.
- Activists and government critics prefer to remain anonymous, fearing repercussions if their identities are revealed.
- In some countries, evading government restrictions to seek new political ideologies is punishable.
- There was also a listing titled, “Ransomware Pack with Source Code,” that claimed to offer nine different types of ransomware, including CryptoLocker, BasicLocker and Jigsaw ransomware among them.
- As you might expect, these websites sometimes host explicit, gory, harmful, and illegal content.
- There are also other case-by-case solutions that work for certain market websites.
Privacy Protection

Similarly, this year’s growth in darknet market revenue also comes after a 2022 decline in revenue. That decline was driven largely by the shutdown of Hydra, which was once the world’s most dominant market by far, capturing over 90% of all darknet market revenue at its peak. While no single market has yet emerged to take its place, the sector as a whole is rebounding, with total revenue climbing back towards its 2021 highs. Crypto hacking, on the other hand, is much more difficult for criminals to hide, as industry observers can quickly spot the unusual outflows from a given service or protocol when a hack occurs. As we’ll discuss later, the decline in stolen funds is driven largely by a sharp dropoff in DeFi hacking. That dropoff could represent the reversal of a disturbing, long-term trend, and may signify that DeFi protocols are improving their security practices.
Mastering Identity And Access For Non-Human Cloud Entities
In Georgia, on its southern border, where more than 100,000 Russians have fled, there is Matanga, a local Russian-speaking darknet market offering the same “treasure hunt” buying system as back home. As of October 2022, the largest volume of drugs purchased at two large marketplaces – BlackSprut and Mega – were for cathinones such as mephedrone and alpha-PVP. These white, synthetic stimulant powders that mimic cocaine and MDMA are highly prevalent in Russia, eastern Europe and the Balkans because they’re cheap and easy to manufacture locally. Some of these sites have turned to influencers to boost their publicity campaigns. Earlier this month a Kraken employee told Russian news website Lenta.ru that the market had a dedicated PR department.
Fake online casinos and social networks are common methods for distributing malware. To avoid infection, it’s best to avoid downloading anything from untrusted sources or websites. Hacked social media accounts are evidence that cybercriminals have a diverse appetite for Dark Web data products. Despite a recent push for security awareness and forcing people to implement 2FA, a huge number of people still become victims of cybercriminals who manage to steal their online payment accounts. As a result, your dark web use may draw unwanted scrutiny from your ISP or law enforcement.
- The goal of an anonymous and privacy network, Tor, is not to engage in the extensive collection of data.
- As cyber threat intelligence professionals monitor these markets, they gain insights into emerging threats and malicious activities that can impact organizations and individuals.
- “Some claim they don’t do it, then don’t police vendors; some claim they don’t do it, but then they do. Some will be selling precursor products but not finished products.”
- Tor’s network performance can cause the market server to take significantly longer to respond than over the I2P network.
- Dark web search engines exist, but even the best are challenged to keep up with the constantly shifting landscape.
- Background research tasks included learning from past drug lords, researching legal matters, studying law enforcement agency tactics and obtaining legal representation.
Boost Your Privacy When Browsing The Web With A VPN
As rapidly developing business, dark web markets are undergoing changes all the time. The current literature on them has covered well various important features, providing valuable insights for the understanding of how dark web markets operate. For instance, Christin 9 collected and analysed data for eight months (between late 2011 and 2012) for a longitudinal study in the most notorious dark web market at the time—Silk Road. Van Wegberg et al. 32 analysed no less than six years of longitudinal data from eight dark web markets. Both works find out that the business models of these markets is maturing.
Dark Web Search: The Best Dark Web Search Engines In 2025
There are many markets that offer a variety of options (i.e. two or more currencies) to provide flexibility for users and vendors. The market usually has a real-time exchange rate for currency conversion, even though most item prices are shown in US dollars. That means the buyer will pay the corresponding cryptocurrency according to the exchange rate. Additionally, Litecoin (LTC) and Tether (USTD) are also available in some markets, but in a very small percentage.
Typical web browsers reveal their unique IP (Internet Protocol) address, making them traceable by law enforcement. But a dark web browser issues a false IP address, using a series of relays, to mask the user’s identity. Law enforcement faces a challenge both in acquiring relevant technical data and in turning it into evidence understandable to the public, members of which sit on juries deciding the guilt or innocence of those charged with dark web crimes.
A Guide To The Silk Road Website
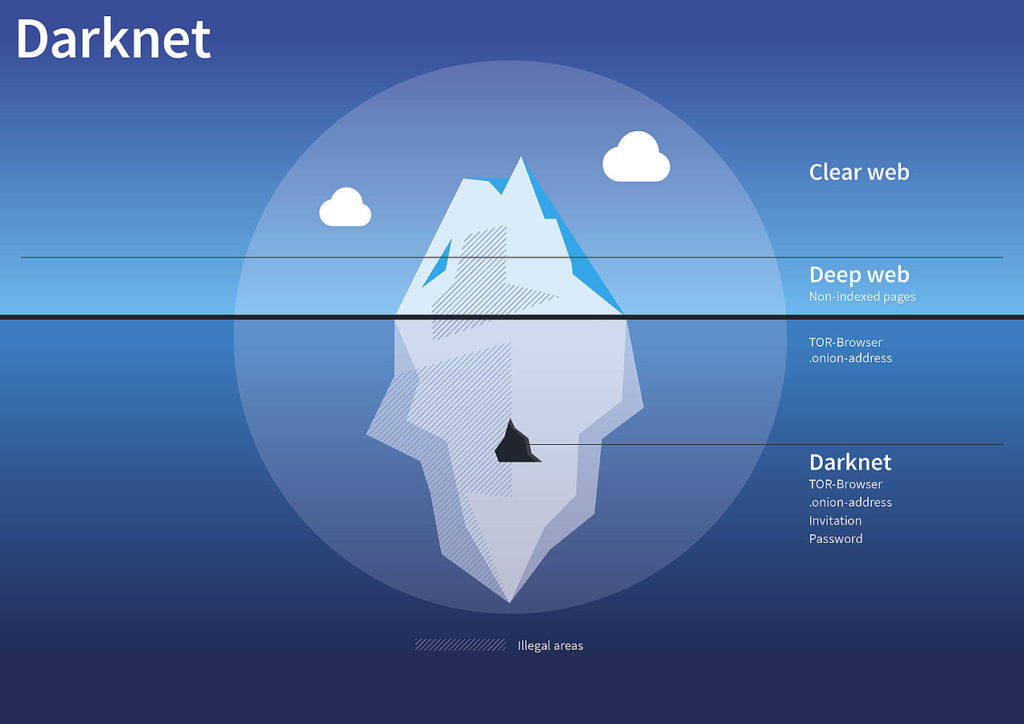
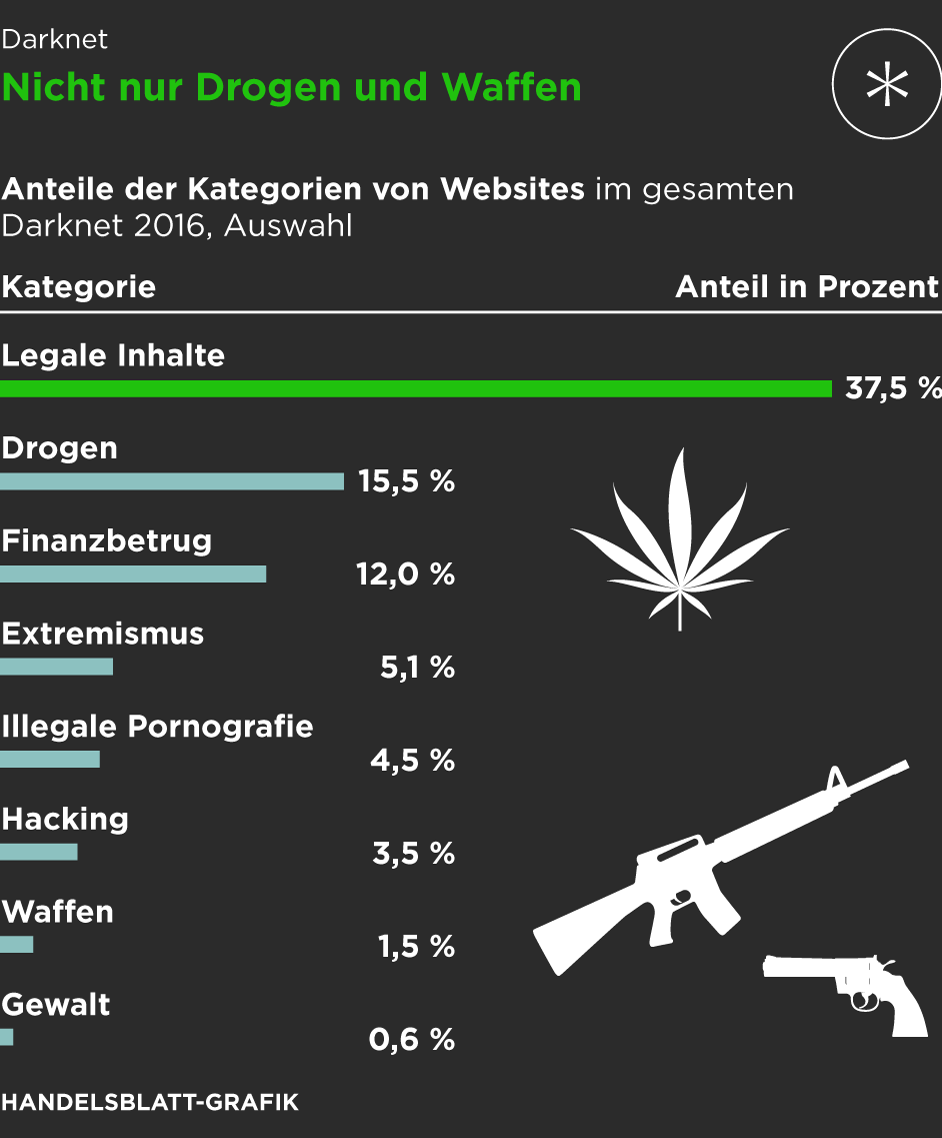
These addresses cannot be resolved by conventional DNS servers, contributing to the hidden nature of darknets. By 2026, darknet markets will likely integrate quantum-resistant encryption, complicating takedowns. Cybersecurity training must adapt to include post-quantum cryptography and AI-augmented threat hunting. Others are looking for stolen data, hacking services, or even banned books and political content. Some are looking for illegal stuff they can’t buy elsewhere, like drugs or counterfeit documents.
SecureDrop is one of the most reliable file-sharing sites on the deep web. SecureDrop helps whistleblowers anonymously send sensitive material to media outlets via a unique SecureDrop URL. ZLibrary hosts free file-sharing access to academic texts, scholarly articles, and general-interest books.
Cryptocurrency Wallets For Safe Transactions
Accessing darknet markets safely isn’t just about the tools you use — it’s also about the way you behave online. By following simple but effective OPSEC strategies, you can protect your identity, avoid scams, and reduce unnecessary risks. Transactions within dark markets predominantly involve cryptocurrencies like Bitcoin, Monero, or Ethereum. These digital currencies provide a degree of anonymity, as transactions are recorded on a public ledger but do not directly link users to their real-world identities. To purchase illicit goods or services, users deposit cryptocurrency into an escrow system or directly to the seller, and the cryptocurrency is held until the buyer confirms the satisfaction of the transaction. In response, cybersecurity professionals, law enforcement agencies, and policymakers around the world are working to combat this growing menace.
Dark Web Statistics For 2025: Key Trends And Threats
Although the dark web still accounts for just a fraction of all illicit sales online, it appears poised for rapid growth, according to the report. Ruheni Mathenge specializes in writing long-form content dedicated to helping individuals and businesses navigate and understand the constantly evolving online security and web freedom worlds. Many dark net sites do not undertake the necessary measures to protect users like most websites on the surface web. As a result, you can be exposed to different malware types, including botnets, ransomware, keyloggers, and phishing.
It’s been a constant back-and-forth between cybercriminals and law enforcement, with each new site trying to be smarter and more secure than the last. In 2019, there were approximately 8,400 active sites on the dark web, selling thousands of products and services daily. Telegram channels supplement traditional onion sites, blurring lines between the dark web sites and more mainstream communication tools. Today’s cybercriminals spread their activities across multiple platforms, making them harder to track and shut down. Naval Research Laboratory in the 1990s and released to the public in 2002. Participants noted that officers responding to criminal activity need to develop the ability to recognize items, such as login information, that could help link suspects to dark web sites, the report said.
Sites on the deep web also use Tor (or similar software such as I2P, the “Invisible Internet Project”) to remain anonymous, meaning you won’t be able to find out who’s running them or where they’re being hosted. Understanding that the nature of the internet meant a lack of privacy, an early version of Tor was created to hide spy communications. Eventually, the framework was repurposed and has since been made public in the form of the browser we know today.
Information is gathered either while running a customised crawler or manually accessing the markets. The next subsection provides an overview of the customised crawler we implemented for conducting this research. While the crawler is helpful in certain scenarios, such as aiding in the understanding of rate limiting, sometimes its utility can be limited during investigations, such as when testing CAPTCHAs and account security. In these cases, manual interaction is generally more effective and precise, allowing for a deeper understanding of the implementation quirks of security mechanisms. In a narrow sense, the term “dark web markets” meant a marketplace on the Tor network.
Some, such as Julia Finess, have become popular and also made a name for themselves on TikTok. “They show an affluent lifestyle with expensive apartments, luxury brands, but with a touch of illicit intrigue.” Many of Telegram’s Russian drug bloggers are most likely sponsored by new darknet drug shops. They often wear clothes with shop logos and publish price lists and post links. Even in the occupied territories of Ukraine, Russian troops entering Mariupol were closely followed by Telegram bots offering hash, mephedrone and alpha-PVP, peddling their wares even before the ruined city had running water returned. It’s not established yet how the drugs were brought to occupied Ukraine but the dealing network likely has some connection with Russian soldiers or non-combat staff. But amid the scramble for power and wealth, experts have told VICE World News that the huge profits being generated by these platforms are being fuelled by money from gangs involved in increasingly sinister crimes.



