It’s been a constant back-and-forth between cybercriminals and law enforcement, with each new site trying to be smarter and more secure than the last. Today’s cybercriminals spread their activities across multiple platforms, making them harder to track and shut down. Besides this, ensure the tool offers a range of extra features, such as search filters and results, free consultation, and reports that ensure a hassle-free experience.
Quick Links
Despite using a VPN, there’s always a risk of the VPN leaking your IP address through DNS or WebRTC leaks or misconfigurations when on a dark web forum or marketplace. Therefore, you must run an IP leak test to ensure that the VPN is working completely fine and is not risking your digital security. Tor2door Market is among the largest dark net shops you must visit in 2025 if you’ve decided to visit such sites. On average, the marketplace consists of more than 11,000 items and 1000 vendors. Besides this, it supports wallet-less transactions and accepts payments through Bitcoin, Litecoin, Monero, and Zcash. However, you must wait some time to reassess this marketplace because it’s been shut down.
Why Using Trusted Directories And Security Tools Is Important
In 20 days, I got the psychedelics at almost half-price compared to the initial order. Established in 2019, Russian Market is a well-known and highly regarded data store on the dark web, specializing in the sale of PII and various forms of stolen data. Despite its name, the marketplace operates primarily in English and serves a global audience. It has gained a reputation for being a reliable source of high-quality data for cybercriminals. Based on our observations from analysis on dark web data using Lunar, we’ve identified the top 7 marketplaces on the dark web in 2025.
Why You Need Automated Dark Web Monitoring
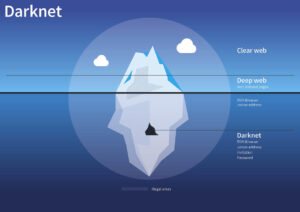
While some .onion sites provide essential services like secure communication and censorship-free journalism, others spread malware or run scams. With this in mind, finding verified links is crucial for avoiding threats on the dark web. In addition, Darknetlive has a list of dark web vendors, which is very convenient — it offers detailed information about each vendor, including .onion addresses (in alphabetical order) and FAQs.
Supply And Demand Dynamics: Meeting Market Needs
Russian Market has consistently remained one of the most popular and valuable data stores on the dark web. The platform’s activity has increased significantly over the past year, indicating its growing influence and market share in the underground economy. STYX Market focuses specifically on financial fraud, making it a go-to destination for cybercriminals engaged in this activity. This happened after Cazes unintentionally doxxed himself by publishing including his personal email address in the header information of the AlphaBay welcome email. We’ve seen dark web vendors listing everything from pirated eBooks and software to counterfeit electronics and fake gold bars. Some are full-fledged criminal enterprises that ship illicit drugs and banned chemicals to their clients from secret production facilities around the world, or engage in fraud and cyber crime on a global scale.
Having possession of the two private keys, PGP Key and Bitcoin Key would easily prove to the feds that the arrested (if arrested) is the vendor on the site. So, the dark web vendor needs to protect those keys very well, and thus he is required to store them both on a little USB flash drive. – Remain cautious of vendors with no or limited feedback, as it becomes more challenging to assess their credibility and reliability. – Take note of any patterns or recurring issues mentioned in the feedback, such as inconsistency in card quality or lack of response from the vendor.
It is one of the most active and up to date markets and always provides new and updated malware and data. Freshtools was established in 2019 and offers various stolen credentials, accounts, and host protocols like RDP. It is considered a go-to site for malware purchasing, providing keyloggers, trojans, and other Malware as a Service products. Torzon Market has established itself as a significant player in the darknet ecosystem, offering a secure, user-centric platform for anonymous trading. Its commitment to privacy, diverse product offerings, and robust security measures make it a preferred choice for users seeking discreet transactions within the darknet.
Verify All onion Links

This not only causes immediate financial loss but also disrupts supply chains and operational efficiency. The lifeblood of these virtual bazaars pulsates through the veins of its vendors. These individuals or groups offer the goods and services on underground dark web markets, shaping the marketplace’s appeal and attracting customers.

What Can Be Found On Deep And Dark Web Credit Card Shops?
KEY TAKEAWAYS Packet loss reduces the speed and amount of data that flows through the network. KEY TAKEAWAYS Vulnerability management tools scan and detect weaknesses within the network that hac… It is advisable to use the best password managers that generate strong passwords and store them in a secure encrypted vault. As a whole, EcoSec is a great tool for using the deep and dark web and gaining visibility and alerts on insights into discovered data theft practices. ZeroFox analyzes text images and videos and remediates threats faster by employing the industry’s advanced AI-powered engine. It enables Digital Risk Protection and easily integrates into SIEM, SOAR, TIP, Business Intelligence, and other technologies.
Tumbling Services
Also a contributor on Tripwire.com, Infosecurity Magazine, Security Boulevard, DevOps.com, and CPO Magazine. You can find featured listings on the homepage and browse the products of your choice. There’s also a search bar that you can use to search for any particular product or vendor. It doesn’t use JavaScript, meaning the website won’t track your activities or exploit vulnerabilities. The website allows a personalized searching experience, where you can search according to your geographical location, country-specific, and keyword or price-specific search results. Since the dark web can be accessed through the Tor browser, use a VPN with the Tor browser to ensure increased protection.
A recent arrest in the Southeast Asia region marked the first time JS-sniffer operators have been caught anywhere in the world. The data was entered into a spreadsheet for analysis, allowing researchers to calculate statistics and identify trends. Adding fullz to a card purchase increases the price by about $30 for a physical card and under a dollar for digital card info. A quick guide for developers to automate mergers and acquisitions reports with Python and AI.
However, delving into the Dark Web comes with significant risks and challenges. Buyers must navigate through a labyrinth of fraudulent sellers and law enforcement operations targeting illegal marketplaces. It is crucial to exercise caution and take protective measures to safeguard personal information. It’s important to implement methods to remove old and inactive listings/vendors.
Cobweb Technologies is the perfect choice for large-scale enterprises working at private and governmental levels. Anyone who wants automated Al and ML-based web monitoring features in their dark web security solution must try this tool. The tool collects and analyzes thousands of database dumps and pastes the information about billions of leaked accounts. This dark net monitoring tool is best suited for all mid-sized to corporate-level organizations. As it is a paid security solution, organizations can directly request a demo or contact the team to hear about the pricing plan. Please check your local laws to ensure your use of VPN complies with statutory requirements.

These vendors are often small businesses or individuals who have turned to the darknet as a way to reach a wider audience or to sell products that may be controversial or difficult to find elsewhere. Legit darknet vendors can be found on a variety of darknet marketplaces, such as Dream Market, Wall Street Market, and Empire Market. By using reputable marketplaces, asking for recommendations, and checking vendor ratings, you can increase your chances of finding trustworthy sources for legal products and services on the dark web.
- The use of JavaScript-sniffers, also known as Magecart, has led to a significant increase in stolen payment card data.
- This is because suppose you get caught by the cops and they take your computer and open it and they can just see that you’re logged in as a vendor on the site.
- “A global law enforcement operation coordinated by Europol has struck a major blow to the criminal underground, with 270 arrests of dark web vendors and buyers across ten countries,” Europol said on Thursday.
- This safeguards vendor conversations from interception and enhances privacy.
- In addition to converting their cryptocurrency into cash using this method, they also exchange their Bitcoin for Monero, which is more private and harder to track.
Firstly, I select a drug category I am interested in and sort goods by the newest first. For example, on WHM, I found 16 MDMA listings at a price less than $2, excluding shipping payment. The cheapest MDMA I discovered cost $1.18 per gram with free delivery and 100% refund – a piece of cake, in my opinion. By supplying stolen data, these dark web links fuel many online scams and identity theft operations, playing a critical role in the darker aspects of the internet. The first category includes classic marketplaces, which serve as one-stop shops for a wide range of illegal goods. These platforms sell everything from drugs and fake IDs to weapons and hacking tools, resembling a digital black-market bazaar.
It deploys AI and ML technologies to analyze data across different web layers. In addition, this platform generates actionable insights and real-time threat alerts that let analysts respond to threats more efficiently and effectively. Ecosec Beacon Systems is one of the leading publicly available information (PAI) and open-source intelligence (OSINT) providers. The service leverages Machine Learning to classify threats, send custom alerts that disqualify noise, and draw the company’s attention to serious issues. It locates compromised passwords, hijacked financial data, and personal data leaked on the web. The security solution includes machine learning technology that detects abnormal behavior within the network.