Here are some examples of dark web prices based on data from Statista and Merchant Fraud Journal. In short, even with Tor, there’s no perfect anonymity online, but there are efforts to claw back our power online, says Lewis. There are other ways for spies, hackers or other adversaries to target Tor. Lewis points to the “first contact problem”, when an attacker spots when someone moves from non-private tools to private ones, noting it’s been used to identify whistleblowers. There’s no such thing as perfectly private or secure on the internet. It’s still possible to track someone’s traffic pinging through the Tor nodes, though it is difficult.
This will help you avoid scams and protect yourself from potential harm. Another important step is to use a different email address specifically for dark web activities. By creating a separate email, you minimize the risk of your personal or professional accounts being compromised. First and foremost, make sure you have reliable antivirus software installed on your device. This will help prevent any malware or viruses from infiltrating your system.

LEGAL SOLUTIONS
The dark web offers a platform for secure collaboration, allowing journalists to report on important issues while safeguarding their sources. If you have been arrested for accessing illegal websites on the dark web, our criminal defence solicitors are on hand to lend their expertise. The dark web is often used for illegal criminal activity, which is why it is important to clarify exactly what it is and what the potential risks are for anyone using it. And if you have cyber skills, then my plea is that you’re generous with them.
Are Sites On The Dark Web Illegal To Use And Visit?
Although content on the dark web is not as ‘indexed’ compared to the one on the clear web, you can still use search engines to find stuff. By using Tor, and especially in combination with a VPN, your internet signal is encrypted, making it invisible to your ISP. Navigating the dark web requires extra layers of privacy, not just because of its content but due to legal scrutiny.
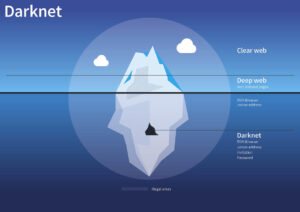
Taking on the mining tunnel metaphor, the Dark Web would be the deeper portions of the Deep Web that require highly specialized tools or equipment to access. It lies deeper underground and site owners have more reason to keep their content hidden. Ransomware-as-a-service (RaaS) kits have been available on the dark web for several years, but those offerings have become far more dangerous with the rise of specialized criminal groups like REvil or GandCrab. These groups develop their own sophisticated malware, sometimes combined with pre-existing tools, and distribute them through “affiliates”.
- The Camouflage Mode is intended for people living in countries with heavy internet censorship, like China.
- Hence, if you participate in them, whether knowingly or unknowingly, you can end up putting criminal charges on yourself, and in some extreme cases, even imprisonment.
- Not only does Tor’s encryption system keep your activity anonymous, it keeps host websites hidden too.
- The reason was so that they could stay anonymous – it would be harder to distinguish the government’s messages between spies if thousands of other people were using the same system for lots of different things.
- Most of the digital content in the world is not accessible via web search engines.
The CSO Guide To Top Security Conferences
Surfshark supports unlimited simultaneous connections to protect as many devices as possible. Also, try its services risk-free with the 30-day money-back guarantee. A budget-friendly VPN service allowing users to access dark web safely anytime, anywhere, and on any number of devices they want.
Report It To The Authorities (if It’s Safe To Do So)
The dark web has flourished thanks to bitcoin, the crypto-currency that enables two parties to conduct a trusted transaction without knowing each other’s identity. “Bitcoin has been a major factor in the growth of the dark web, and the dark web has been a big factor in the growth of bitcoin,” says Tiquet. All this activity, this vision of a bustling marketplace, might make you think that navigating the dark web is easy. The place is as messy and chaotic as you would expect when everyone is anonymous, and a substantial minority are out to scam others. The launch follows a similar approach by the U.S.’s Central Intelligence Agency, which published videos on social media channels to target potential Russian spies in 2023. The portal will be available from Friday, with instructions on how to use it publicly available on MI6’s verified YouTube channel.
Why Is It A Safeguarding Concern?
It also keeps the graphical copy and text of the page for better accuracy. In some countries, such as China and North Korea, the government uses heavy online censorship and blocks many dark web websites. This is where an Onion website, like the Tor browser, comes in handy. Hence, if you participate in them, whether knowingly or unknowingly, you can end up putting criminal charges on yourself, and in some extreme cases, even imprisonment. The dark web is a part of the internet that you only step into with a specific tool (Tor, more on this later in the article). Though people usually think of dark websites as the wrong online place, that’s not the complete truth.
My own father was the victim of fraud and I know from personal experience the importance of supporting those who have been victimised through no fault of their own. And now that it’s happening online, it’s happening to even more people. That’s why today I’m pleased to announce that we will be investing over £50 million over the next year to bolster cyber capabilities within law enforcement at a national, regional and local level. And just yesterday this government launched a new world-fist £13.5 million Cyber Innovation Centre in London to help secure the UK’s position as a global leader in the growing cybersecurity sector. It’s not just the Wannacrys we need to protect ourselves against, but the cyber scams that put money into the pockets of organised criminals because they think they have easy targets.
Domestic ABH Allegation – No Further Action Taken Following Expert Legal Representation – Wembley Police Station (May
Many people install a VPN as well, but then you’re putting your trust in an additional third party to not track your activities or report them to anyone else. Tor is like the public-facing door to the dark web, and there are even mobile apps for Android and iOS. While there are other browsers you can use to get on the dark web, Tor is usually recommended as the best for most people in terms of the features it offers and the ease with which anyone can make use of it. To get on the dark web, you need a browser built for the job, and the best in the business is Tor. Tor is a browser engineered for extra security and privacy, and can be used to navigate the normal, surface web as well as the dark web.

It can only interact with the gateway, the most effective method by which the browser protects user applications from learning a device’s IP address. I2P, or the Invisible Internet Project, allows you to access the ordinary and dark web. Specifically, the I2P darknet is accessible, while the Tor network is accessible through the Orchid Outproxy Tor plugin.

Do Police Ever Catch People Using The Dark Web?
VPNs are often recommended as protection in such cases, but Whited disagrees. When you use the Tor network, your traffic is layered in encryption and routed via a random relay, where it’s wrapped in another layer of encryption. Indeed, Facebook, The New York Times and now even the CIA have sites on the dark web, hosting “onion” versions of their pages that can be accessed via the Tor browser. The spy agency is hoping to securely and anonymously collect tips, though its entire website, including job listings, are available on the onion service.
Fill out this form to request a meeting with our cybersecurity experts. Based on Mozilla’s Firefox, this browser hides all that pinging about in the background. “It’s a web browser. Use it like one. It’s that simple,” says Muffett. That’s the desktop edition, but there’s a version for Android and an unsupported onion browsing app for iOS. Nathan Bake is branded a “serious danger” to children after acting as head moderator of the website. You can contact us 24-hours a day, seven days a week for an immediate free initial consultation, expert legal advice and representation.
Other sites explicitly block search engines from identifying them. There are often copious amounts of how-to articles, software exploits, and hacked credentials for sale. Not every visitor is a criminal, but this is where most cybercrimes begin. With the onion browser, you can access ordinary HTTPS websites on the web.
No user names are tied to actual identities, and no moderation like one may find on Reddit. Users leverage these platforms to organize protests, whistleblow, share survival guides, or share files P2P. Some markets even sell privacy tools, but you are more likely to run across counterfeit prescription pills and stolen identities.
- Because as it becomes possible to connect more devices to the internet and we continue to build the internet of things – from toasters to washing machines – the number of avenues for hackers widens.
- This anonymity has attracted criminals seeking to avoid detection by law enforcement agencies.
- American student, David – not his real name – explains why he chooses to buy illegal drugs on the so-called ‘dark web’.
- This public distrust has led to many technology companies pushing back when it comes to accessing users’ devices.
- The dark web and the browsers used to access its sites are not illegal.
There can be a long wait for forensic results, as there is a large backlog of cases from the rise in cyber-crime during the pandemic. However, as noted above, anyone who has fraudulently accessed your computer will not be too concerned about leaving traces of your details for the police to find. Evidence can be recovered digitally by the police, both from the internal storage of a computer and in the cloud network. There is more than one platform offering anonymous internet browsing – a few examples being I2P (Invisible Internet Project), Freenet, and Tor (The Onion Router).
Although the social application is known for collecting data on its platform, it does not like sharing the information with others. The website has an advanced search filter and an easy-to-use interface, which makes it easy to find what someone is looking for. It is the dark web’s version of Wikipedia with a massive links directory. You will find all the necessary .onion links to access any content or service on the dark web.

Is It Illegal To Access The Dark Web?
Because of this, some people use it to get around government restrictions, while others use it for illegal activities like smuggling drugs and weapons. Unlike other search engines, it does not collect or share web activities and personal data of users. The dark web contains much of the internet’s illicit content, ranging from drug trafficking to child pornography sites.