DigDeeper offers in-depth analysis of technology and privacy topics rarely covered by mainstream media. The website’s articles focus on digital rights, surveillance, and security research. I found their technical explanations clear and well-researched, though the site updates less frequently than other news platforms.

Steps On Configuring And Connecting To Tor
- Ultimately, the dark web can be a place of great intrigue, but it’s essential to approach it responsibly.
- The advantage of this version is that you can effectively create a Facebook account anonymously or use this social media platform in a restricted region.
- In a world where online privacy is constantly under threat, the Tor Browser offers a powerful tool for safeguarding your identity and protecting your digital footprint.
- Since you’ve now installed the Tor browser, you can safely browse dark web websites and other (previously) hidden websites.
- Be aware that The Hidden Wiki has links to material you might find objectionable, that there’s no longer a single official site, and that many fake sites claim to be the real thing.
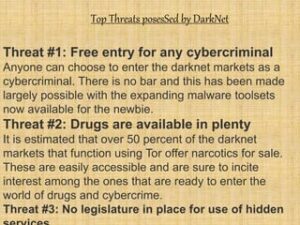
This is because law enforcement often actively monitors these sites. You risk being targeted for attacks if you explore the dark web without protection. The threat can extend to your entire network of devices connected to the internet.
How Do Onion Routing And Tor Work?

By default, Tor has stricter privacy settings than most standard web browsers. Users can take further steps to maximize privacy when browsing with Tor. To connect manually for the first time, click on the Connect button on the homepage and wait for Tor to establish a connection. Since its public release, researchers have discovered various vulnerabilities in Tor, which have been quickly patched.
Originating Traffic
Reuters, Fox, NBC, CNN – all of them keep open dark web channels to receive anonymous tips from whistleblowers. People mostly use it for covert communication, anonymous tips submission, and stuff like that. In terms of functionality, I don’t think there are too many differences between regular IMAP, POP3, and SMT services and the stuff you can use to communicate on the dark web. So, it’s only natural to find ways to keep in touch with your darknet buddies and/or customers.
Step 5: Find Verified Onion Links
Downloading tainted files or clicking suspicious links can install malware on your device, so be cautious when surfing the web. A traffic correlation attack takes serious resources, but it’s doable for advanced actors with sufficient motivation. The performance of entry, middle, and exit nodes can vary, and some are slower than others.
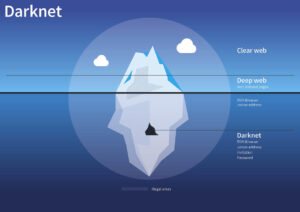
Next, open the Tor browser app and wait for it to connect to the Tor network — this usually takes 5–10 seconds depending on how fast your internet connection is and how overloaded the Tor network is. That authoritarian states want to control the internet as completely as possible is obvious. However, even in democratic countries, investigators want to monitor what is distributed on the dark web through the Tor network. This is because of the wide-ranging content on weapons and drugs and for pedophiles that appear on the dark web. Tor is a network that allows users to surf the Internet anonymously.
Do I Need A VPN If I Access The Dark Web On My Phone?
If you must download something from the dark web, only download files and run them using a completely isolated virtual machine. Understanding and knowing how to safely access this part of the internet is an important digital skill for today’s era. Fun fact is that Tor Browser (Tor network is a different thing than the browser) is built from Firefox ESR (Extended Support Release), a modified version of Firefox.
Is It Safe To Browse The Dark Web?

Tails is a privacy-focused live operating system that you can boot from a USB stick. It is designed to be used without leaving a trace on your computer. It forces all internet connections to go through the Tor network. It also comes with several secure pre-installed software programs, including the Tor Browser.
- One example is OnionShare, a service that uses Tor to share files securely and anonymously (you can imagine that this would be important for journalists communicating sensitive information, for example).
- Taking the necessary precautions makes tracing your activities on the dark web difficult.
- This malware can be concealed within seemingly harmless files, and even simply visiting a compromised website might lead to an unintentional download and installation of malicious software.
- That authoritarian states want to control the internet as completely as possible is obvious.
This could include government services to access your records, health care services, members-only areas, intranets, or corporate resources. It provides great privacy and security, and it’s good for secure streaming, torrenting, and gaming. And because VPNs encrypt your traffic but are much faster than Tor, they’re also good for bypassing bandwidth throttling. That said, the Tor browser also has some security issues, so it can’t 100% protect users’ privacy. Plus, some people still don’t know how to get and use the Tor browser, despite it being pretty accessible and user-friendly.
Best Free Firewall Software In 2025
Yes, many organizations monitor the dark web for cybersecurity intelligence—always in line with legal compliance. Experienced blogger with a strong focus on technology, currently advancing towards a career in IT Security Analysis. I possess a keen interest in exploring and understanding the intricacies of malware, Advanced Persistent Threats (APTs), and various cybersecurity challenges. My dedication to continuous learning fuels my passion for delving into the complexities of the cyber world.
Brave is a browser based on Chromium that, by default, blocks ads and website tracking. This creates a faster and privacy-focused browsing experience without any configuration. It is perhaps the most secure way to run applications anonymously. If you want a strong setup that has no leaks, Whonix might be the best dark web browser solution on the market.
To help find functioning .onion URLs, look to dark web directories and forums — Reddit users recommend tor.taxi, tor.watch, daunt.link, or one of the Hidden Wikis. Finally, you need to enter website addresses to access content on the dark web since you can’t browse by entering a search query as you can on the clear web. Suppose you share your name, social security number, or any other personally identifiable information on any dark website. In that case, there is a high chance that your data will become accessible to cybercriminals.