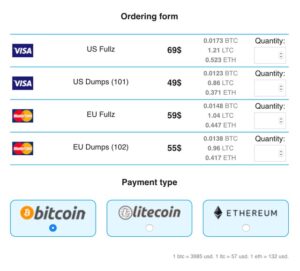
Data gleaned from ransomware and data breaches is available on the dark web. Millions of customers’ personal data, including names, addresses, bank account and credit card account information, and many other forms of sensitive data. In 2002 the dark web began to grow significantly when researchers backed by the U.S. Journalists in overly restrictive countries also appreciate the anonymity of the dark web.
However, its network is still small, and there aren’t many hidden services available yet. Don’t log into any real accounts, reuse usernames, or enter any personal details. Treat every site as untrusted unless you’ve verified it from multiple sources.
What Is The Dark Web? How To Access It And What You’ll Find
Fortunately, in Hidden Wiki, every website is followed by a brief description so that the user knows what to expect. You can also take a look at the blogs & essays section if you want to find some nifty coding resources. At first glance, Tor doesn’t look that different from your regular browser – it has a search bar, lots of quick-launch icons, the peeled onion icon smack in the middle of the screen. I strongly recommend surfing on the dark web using virtual machine software instead of your locally installed Windows. Because it’s easier to contain malware in a virtual environment, which can be fully controlled. Well, VPN over Tor is basically its opposite – instead of going through the VPN first, the signal passes through the Tor network, before going through the VPN.
But using these tools for illegal purposes constitutes a criminal act either way. Setting up NordVPN will ensure that it encrypts your connection, so your ISP cannot see that you are using Tor. Its main appeal is that it offers more privacy and supports legacy Firefox add-ons. It also eliminates data collection, telemetry, and other suspicious code modern web browsers tend to use, which are troubling at best.
What Are Onion Sites?
- Tor (“The Onion Routing” project) network browser provides users access to visit websites with the “.
- In today’s fast-paced digital landscape, IT service providers are under immense pressure to delive…
- If you want to be untraceable and undetectable, connecting to the dark web via the Tor browser is a major step towards that, but not the only step you’ll need.
- It’s not mysterious or spooky; it’s home to everyday things like scientific research, medical records, private financial information, and secure communications.
- By using Tor, and especially in combination with a VPN, your internet signal is encrypted, making it invisible to your ISP.
However, it’s important to note that this built-in VPN is not designed to connect directly to the Tor network or .onion sites. But it’s recommended that you stick to Tor Browser still for true dark web access. The browser routes your traffic through a global network of volunteer-run servers (sometimes called nodes), encrypting your data and masking your IP address multiple times. Lokinet is easier to set up than I2P, and it may run faster than Tor in some cases, especially when visiting regular websites through its secure network.
How Do I Verify An Onion Link Is Safe?
Once you are certain that you have the correct URL, save it in an encrypted note—the Tor browser will not cache it for later. Otherwise, there’s a good chance of falling victim to a phishing scam like this fake Bitcoin mixer. NordVPN is offering a fully-featured risk-free 30-day trial if you sign up at this page. You can use the VPN rated #1 for the dark web with no restrictions for a month—great if you want to try this no-log provider’s Onion over VPN servers for yourself.
Safely Browse And Verify Onion Sites

While not mandatory, using a VPN adds an extra layer of privacy and security by hiding Tor usage from your internet service provider. There are a few reasons why the dark web isn’t stopped or shut down. First, it’s difficult to track and monitor activity on the dark web since much of it is encrypted.
We recommend you only visit safe dark web links to explore such as The CIA, Facebook, DuckDuckGo, and Torch. Many services that are allegedly offered on the dark web are scams. Some services are genuine; you can get what you want at an agreed fee. Furthermore, it’s critical to understand that Whonix is not a stand-alone browser.
Guide To Accessing Tor Via Tails OS On A USB Thumb Drive:
As a general rule, it’s best to use the default settings in Tor or the Onion Browser. Changing any of the default settings can make websites misbehave or not load correctly. This scale is why newspapers and mainstream news outlets regularly trot out scare stories about ’90 percent of the internet’ consisting of the Dark Web. They are confusing the generally dodgy Dark Web with the much bigger and generally more benign Deep Web. Thus the ‘Deep Web’ includes the ‘Dark Web’, but also includes all user databases, webmail pages, registration-required web forums, and pages behind paywalls. There are huge numbers of such pages, and most exist for mundane reasons.
Carefully matching your needs to the strengths and weaknesses of each solution ensures optimal privacy, security, and usability. Download the Linux version from torproject.org, extract the file, and run the start-tor-browser script. Tor anonymizes by bouncing traffic through relays; VPN encrypts and routes through a single server.
Choose A Dark Web Search Engine

It has features to maximize your privacy, unlike standard web browsers that have less stringent privacy protections. However, using Tor has some challenges that you should be prepared for. Like NordVPN, this provider doesn’t store logs and has around 20 third-party audits to prove it. Its RAM servers and Private DNS go a step further to protect your identity online. Not to mention its Advanced Protection that blocks malicious sites, trackers, and ads.

He holds a bachelor of arts degree from the University of Washington and is now based in Boston, Massachusetts. The biggest differentiator between the deep and dark web is that dark web activity is made anonymous through a variety of encryption and routing techniques. If possible, consider using a Virtual Machine (VM) using tools like VMware or VirtualBox for additional security.

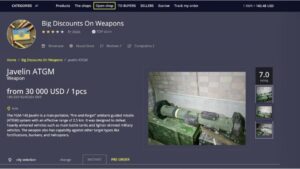
For more information, read more about the most secure email service providers in my other post. But again, your ISP won’t be able to see any of the content you’re reading or what you are sending and receiving through the Tor network. The dark web is a decentralized web, which means that the data is stored on many different servers around the world. It has been estimated that a large percentage of dark web traffic is related to illegal pornography that includes underage victims. Hacker services against banks and other financial institutions are offered there. There are a number of services and tools available on the dark web, many of which can be used for nefarious purposes.
- Researchers from the Electronic Frontier Foundation and other groups continued its development and launched the Tor project in 2006 as a tool for journalists, activists, and whistleblowers.
- I2P (Invisible Internet Project) is an open-source network designed to allow anonymous and private communication.
- You should only ever access websites you know are safe because they’re vetted by websites or other sources that you already know are safe.
- Speeds were solid for browsing text-heavy dark websites and small links.
- Some whistleblowers and journalists use these portals to safely leak information, especially when a source requires complete privacy.
- We’ll focus on secure, ethical practices tailored to cybersecurity professionals and IT leaders.
To access the dark web, you must have specialized software, such as the Tor Browser. It creates a space for staying anonymous, which itself is kind of a double-edged sword. Let’s find your key to safe access to the best dark web sites and anonymous browsing. VPN-over-Tor breaks dark web compatibility, reintroduces trust in the VPN provider, and creates unnecessary complexity.
This stops online criminals from eavesdropping on your Wi-Fi connection and intercepting any data you might be sending or receiving. Just like when navigating the surface web, the dark web has similar risks that should be taken into account when protecting your personal information. But you can face criminal charges if you use the dark web to sell or purchase illegal firearms, drugs, pornography, stolen passwords, hacked credit card account numbers, or other items. PCMag has a guide for staying anonymous as you navigate the clear web. I don’t recommend seeking out dark web content unless you have a specific reason to do so.