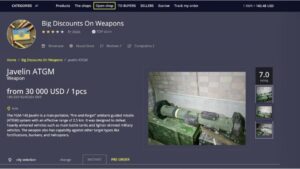
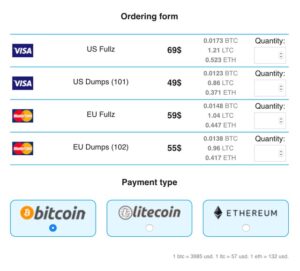
Notifications hint it will allow the sale of everything except illegal porn and firearms (weapons). Extremely transparent vendor-details displayed for legitimacy-verification. As stated above there are other areas and goods that are sold on this market. Drugs are another area of the site which appears to be popular. There are currently 50 listings in this section, second only to gadgets, which sells products such as phones and computers.
Cyble Partner Network (CPN) Join Us
- However, due to copyright infringement, Sci-Hub is considered illegal and banned in many countries.
- This further complicates monitoring efforts because now you need to search for the related Telegram channels and track activity there and on the marketplace itself.
- It offers top-of-the-line security and fast speeds for a smooth browsing experience on the dark web.
- Other risks, such as frauds perpetrated by customers and exit scams, were considered inevitable on the dark web, but also manageable.
Both under- and over-sampling methods were implemented in python using the package “imblearn” (Lemaître et al., 2017). Next, we utilized the “LinearSVC” classifier with an “l2” penalty (the default regularization parameter used to reduce complexity in the model and avoid overfitting) using a tenfold cross-validation procedure. The test performances were evaluated using the average accuracy, and the weighted average of precision, recall, and F1 scores across all folds, as shown in Table 3. The python package “scikit-learn” (Pedregosa et al., 2011) was utilized for training, testing, and evaluating the classifier.
IPhone Or IPad
Thus, estimation of product origins from dark markets and measures of seized goods might also vary because they capture products at different supply chain stages. While the study is based on historical data, we showed that examining dark market counterfeits in more detail can contribute to our understanding of the counterfeit market. With an increasing emergence of darknet markets and single vendor shops, offers of counterfeits are also likely to increase. Thus, examining current dark market data would be valuable in future analyses of IP crime, which would provide us with more up-to-date insights. Collecting data from dark markets to gather intelligence could be done manually and automatically and would probably be very cost-effective compared to (border) seizures.

Can You Access The Dark Web With A VPN?
Get the latest in privacy news, tips, tricks, and security guides to level-up your digital security. Inside the Tor network, sites cannot use regular domain names. These domain names are not registered with a central authority but are instead derived from cryptographic keys.
Established in 2012, the platform is a time capsule that collects snapshots of websites. These onion addresses will remain online even if the original page disappears. It also keeps the graphical copy and text of the page for better accuracy.
Essential Tools For Safe Darknet Market Access
This is an estimated reading time to let you know how long it will take you to read all the content on this particular PrivacySavvy.com page. However, it has a sneak peek, easy guide steps, and/or a quick list providing quick in-page navigations and easily-found answers if desired. Farwa is an experienced InfoSec writer and cybersecurity journalist skilled in writing articles related to cybersecurity, AI, DevOps, Big Data, Cloud security, VPNs, IAM, and Cloud Computing.
Holding And Placeholder Prices
Markets that lack proper security often become targets for law enforcement, scammers, or cyberattacks. While Tor provides anonymity, combining it with a reliable VPN adds another layer of protection. A VPN hides your real IP address from your Internet Service Provider and ensures your Tor usage is not easily detected. This is especially important in regions where Tor is monitored or restricted. Since its inception, the market has catered to criminals looking for high-quality counterfeit items, such as fake IDs, passports, and branded luxury goods. The platform is favored by cybercriminals seeking access to accounts that can be exploited for fraud or sold to others.

Can WiFi Owners See Your Internet History?
If you don’t have NordVPN account then buy here $2.75/Month (77% discount). If you have been login successfully then connect your computer with any Onion over VPN server. If your connection has been established then you are ready for next step. If you are still interested to explore this deepest internet place/darknet then you need to prepare your workstation with some requisites.
What Exactly Is Sold On These Marketplaces?

A further analysis is invited which treats the counterfeit notes as part of an actor-network. In this perspective the discourse around it, the production and distribution system, is part of a set of practices that produce the product as a workable entity. In the late 1990s, a powerful tool – the Onion Router (or Tor, for short) – was built to protect military operations, particularly in hostile zones where secrecy can mean the difference between life and death. It quickly outgrew its military roots, emerging as the Tor browser, a free gateway to the dark web’s digital back alleys. It is now one of the most widely used browsers to access the dark web.
We then focus on counterfeit product types and product origins and compare our measures with estimates from audits of goods seized by law enforcement at borders. Lastly, we evaluate the monetary value of offered and sold counterfeits and the generated sales volume of vendors. Inspired by previous research (Wegberg et al., 2018), we used the annotated listings to train a multiclass classifier to predict the labels of the remaining unlabeled counterfeits. We generated text features from the merged product title and description to train the classifier. However, we first lowercased the texts and removed all punctuation. We then tokenized the text, removed all English stop words, and stemmed the remaining words.
Real-World Examples: Data Breaches Feeding Dark Web Black Markets

But let’s be realistic, the best defence isn’t just playing detective after the fact. It’s making sure your sensitive information never lands there in the first place. I wanna provide labelled products, good advice and service, like a real business. Not sit in a shitty car park selling $10 bags from a car window all day.
Also, anybody can sign up to sell or buy; you just need to make an account through the open entry registration form. Are Wi-Fi hosts and owners able to see what you’re doing online? Using a dark web-specific browser such as Tor or I2P itself is legal in virtually all countries. But using these tools for illegal purposes constitutes a criminal act either way. A VPN like NordVPN provides an additional level of encryption and shields your use of Tor from your Internet Service Provider. Brave is a browser based on Chromium that, by default, blocks ads and website tracking.
Therefore, you must run an IP leak test to ensure that the VPN is working completely fine and is not risking your digital security. In 2013, the FBI shut down the Silk Road, but it was later relaunched in 2014 with the new name of Silk Road 2.0, but the German authorities shut it down in the same year. Other than the Silk Road 2.0, similar marketplaces also emerged, but they all went down sooner or later. Below are the best marketplaces on the dark net that we hand-picked after going through multiple shops and doing extensive research.