Law enforcement agencies keep an ear to the ground on the dark web looking for stolen data from recent security breaches that might lead to a trail to the perpetrators. Many mainstream media organizations monitor whistleblower sites looking for news. In the wake of recent headlines announcing actions against Hydra Marketplace by the U.S. and German governments, darknet markets have made an ironic entrance into the spotlight. Taking the necessary precautions makes tracing your activities on the dark web difficult.

Hacking And Cybercrime Sites
This includes using an anonymous browser like Tor, a VPN to encrypt your connection, an antivirus for protection against malware (we recommend TotalAV), and generally being careful not to reveal personal information. Having regular security check-ups and audits is great for catching vulnerabilities before they can be exploited. Public awareness and education are just as important since when people know what to watch out for; they’re less likely to fall victim to cybercrime. Changing the Tor browser settings can further boost your security levels on the dark web shops.
Most reputable darknet marketplaces employ the use of escrow systems for mutual buyer and seller protection, with step-by-step client-side encryption features leveraging PGP to ensure end-to-end privacy and anonymity is preserved. A while back I made another blog post on PGP keys which helps explain what PGP is and how it works. A dark web market is a hidden online platform where users can anonymously buy, sell, and trade illegal or sensitive items. Such markets are typically accessible through the Tor network, which anonymizes traffic by routing it through multiple relays and encrypting each layer.
In our study, we created a co-citation map to uncover the linkages between SDG as measured through citations. The proximity between SDGs indicates how similar they are in co-citation frequency, meaning that publications from two SDGs are often cited together in the same set of publications. The nodes’ size represents the SDG frequency in terms of total publications, and the thickness of the edges represents the frequency of co-citation between SDG. Based on the keywords in this cluster, as seen in Table 5, the theme of Cluster 2 is Cybercrime, Data Privacy, and Cryptography and is closely connected to the illicit drug trade on the Darknet.
Cryptomarkets are online marketplaces on the Darkweb that are used to sell illicit drugs. The research also looked at how vendors diversify and replicate across marketplaces, the number of listings they manage, and the number of cryptomarkets they are active on. This study shows the importance of online marketplaces in illicit drug trafficking and how analyzing online data can provide knowledge about criminal activities.
13 Top Funders And Associated Countries
Individuals are also at risk, as their personal information can be exploited for identity theft or sold multiple times over. After all, criminals are getting more creative and professional by the day, running their operations like businesses with customer service and even reviews. The growing shift toward more sophisticated and user-friendly criminal organizations is quickly becoming a real headache for cybersecurity firms.
We understand the curiosity to venture into the dark web, but you also need to understand that it’s never safe to venture into this portion of the internet without fully understanding what it entails. Freshtools is a unique marketplace in that it does not only provide the stolen data, but it allows criminals to purchase MaaS which can cause further damage to the victims. It is one of the most active and up to date markets and always provides new and updated malware and data. Established in 2019, Russian Market is a well-known and highly regarded data store on the dark web, specializing in the sale of PII and various forms of stolen data. Despite its name, the marketplace operates primarily in English and serves a global audience.
The Evolution Of Dark Web Marketplaces
- For example, it maintains your privacy and enables you to access untraceable content and services.
- Also, use an effective antivirus program to check threats if you decide to download files.
- To stop the marketplaces is not a walk in the park as it takes immense effort from authorities like the FBI and international law enforcement.
- All research articles published in The Indian Journal of Law and Legal Research are fully open access.
- After the Biker DLC, players can now purchase buildings for illegal drugs and counterfeit products manufacture, and distribute them through a darknet website called “The Open Road” where law enforcement cannot be notified of the player’s trade.
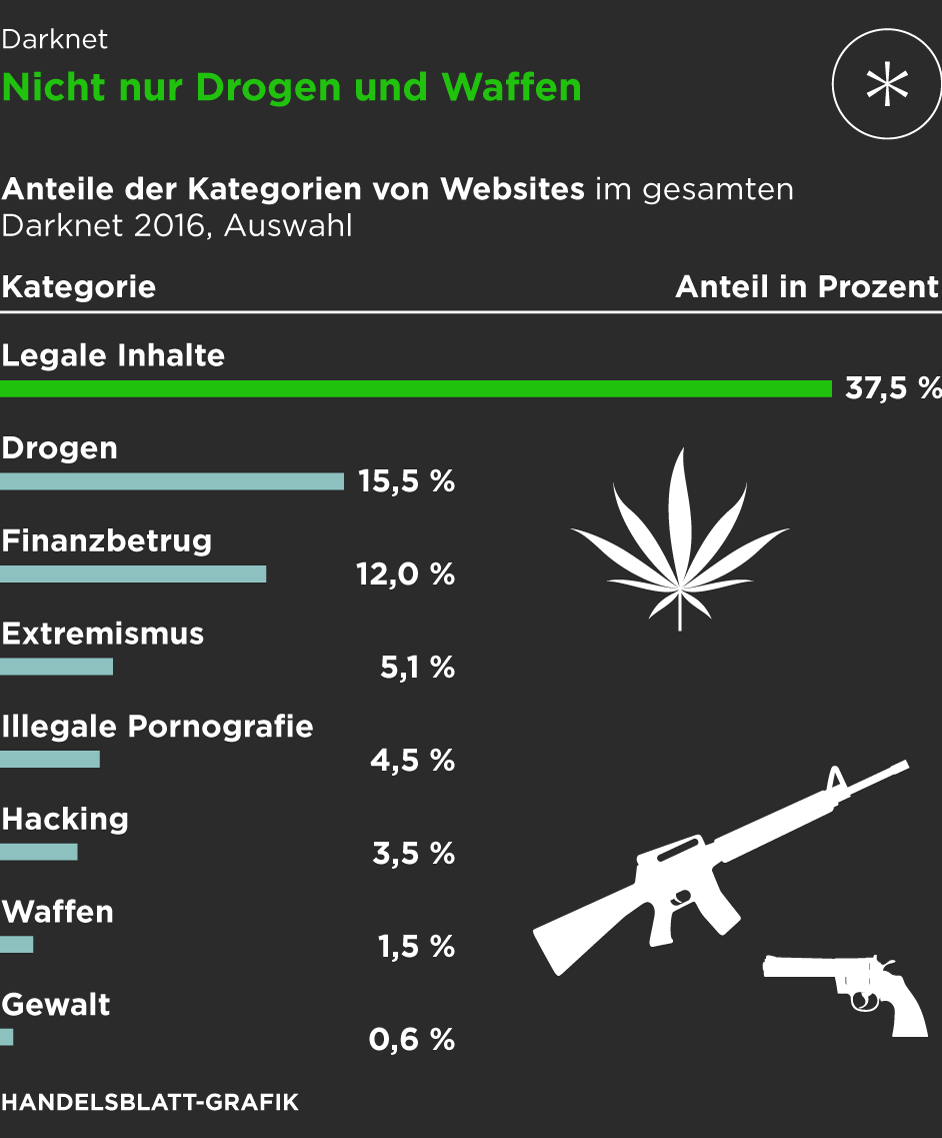
In fact, some of the most profitable illegal digital products on the dark web are crypto accounts, online banking credentials, and e-wallets. While there are legitimate products and services in the darknet markets, often, these markets deal with illicit goods and services like drugs, fake documents, and hacking services. Their presence can make you wonder why darknet markets and not just the regular online stores. The darknet is a mysterious and often misunderstood part of the internet, attracting both intrigue and concern. Darknet markets, in particular, have gained attention for their role in facilitating the exchange of illicit goods and services.
How To Find New, Active Dark Web Links
It offers a wide range of goods and services with robust anti-DDoS protection (with military-grade security protocols) and no JavaScript, ensuring privacy and uptime. As these marketplaces keep changing, it is critical to stay on top of the main platforms on the dark web worth monitoring. Monitoring dark web markets is crucial, no matter if you are a business or individual, as you can then proactively identify and mitigate potential breaches and cyber threats. Ever since Silk Road went down, several dark web marketplaces have kept coming and several of them shut down again.
Verified Social Channels And News Sites
These typically come with “.onion” after them, rather than something like “.com” as on the standard web. Not only do you need a dark web browser, you need a dark web search engine too. This search engine will get you to the sites you need, though you can also go directly to dark web addresses if you know what they are, as with standard URLs. Cybersecurity has to also cover everything physically on your computer too—which law enforcement or government authorities might have the right to seize if they come calling.
Sign-up For Secret Service News Straight To Your Mailbox
While accessing the dark web using Mozilla Firefox is possible, you must first adjust its settings. While it might appear tempting to venture into the dark web, it’s crucial to understand that the risks here are far more severe compared to the deep web. No one is hiding here—they’re just guaranteeing that people in censored countries can read the news without being flagged. Keybase is a fantastic onion website that lets you cryptographically bring your different online identities together. Another notable security trick Wasabi uses to verify transactions is the Neutrino protocol.
How To Protect Your Personal Data Online
People in countries with heavy internet censorship must get a VPN or Tor browser to access the surface web. It is easily accessible by the general public and requires no special configuration. You can find sites like Facebook, Wikipedia, e-commerce sites, YouTube, and more here. These sites are a hybrid tutorial-underground where wannabe hackers ask questions and professionals sell their services or stolen data. The anonymity provided by onion routing comes at the cost of slowing your internet considerably. As such, we do not recommend using Tor if you want to do data-intensive activities like streaming in HD, gaming, torrenting, or making video calls.
A Brief Overview & History Of Darknets & Dark Markets
We’ve also included tips for keeping your connection and data safe when visiting the dark web. HSI is a worldwide law enforcement leader in Darknet and other cyber-related criminal investigations. The DHS Cyber Crimes Center (C3) combats cybercrime, online child sexual exploitation, and criminal exploitation of the internet with state-of-the-art forensic technology.
Archived Content
One of the most popular ways to get around the dark web is not to use a search engine at all. Just like in the old days of the internet, the dark web maintains numerous indexes of sites, like The Hidden Wiki. Unlike Ahmia and Haystak, however, DuckDuckGo doesn’t search .onion sites. Use it to search the normal internet from the privacy of your Tor Browser.
The significance here lies in the potential damage to individuals and businesses. Companies must implement strong data security measures, employ encryption, and monitor for data breaches to protect customer and employee information. In Grand Theft Auto Online, players who purchase warehouses and garages for illicit cargo and stolen cars can buy/steal and sell them through trade on the “SecuroServ” syndicate website. After the Biker DLC, players can now purchase buildings for illegal drugs and counterfeit products manufacture, and distribute them through a darknet website called “The Open Road” where law enforcement cannot be notified of the player’s trade. Because of its anonymity, the dark web is filled with illegal services and is used by numerous criminal groups, including ransomware gangs.
- For example, you shouldn’t pirate copyrighted material, engage in terrorism, or share illegal pornography.
- This makes it extremely difficult to find out who you are transacting with.
- Even without monitoring your browsing activities, DuckDuckGo will offer decent answers to your questions.
- Researching the Darkweb can raise ethical considerations, particularly if it involves studying illegal activities or vulnerable populations.
- This research received no specific grant from funding agencies in the public, commercial, or not-for-profit sectors.
The consequences can be lethal to those whose data is stolen, like identity theft, emotional distress, and even financial loss. Interestingly, the hackers don’t hide, but most of them even openly advertise what they offer on the darknet forums. Therefore, you can hire them to perform a task for you, from planting malware to hacking email accounts and even breaking into various social media accounts.

Right now, you can use many cryptocurrency .onion sites to buy or sell all types of cryptocurrencies. Established in 2012, the platform is a time capsule that collects snapshots of websites. These onion addresses will remain online even if the original page disappears. It also keeps the graphical copy and text of the page for better accuracy. In some countries, such as China and North Korea, the government uses heavy online censorship and blocks many dark web websites. You will find all the necessary .onion links to access any content or service on the dark web.
A keyword co-occurrence network focuses on understanding the knowledge components and knowledge structure of a scientific/technical field by examining the links between keywords in the literature. A keyword co-occurrence network is created by treating each keyword as a node and each co-occurrence of a pair of words as a link between those two words 55,56. The nodes highlight the keywords, and the size of the respective nodes reflects the frequencies of co-occurrence of these keywords. Node size and line thickness are positively related to the keyword connection; the larger the node, the higher the frequency of the keyword, and the thicker the line, the closer the connection between the two topics. Bibliometric studies use quantitative analysis to examine the productivity, Influence, and other facets of the research environment. The PRISMA-P 2015 framework was used to build the dataset for the analysis 29.



