This is easily the largest and considered the best dark web market and Dark web marketplaces, and you can find basically anything you can think of here. Below, we’re going to explore eight of the most popular Darknet markets that are currently available right now, helping you to identify what’s out there, and get to know a bit more about each one. They can then trace the user, identify them as far down as their name and address, and act accordingly. While this is great for protecting a country, the problems arise since hackers can do the same thing.
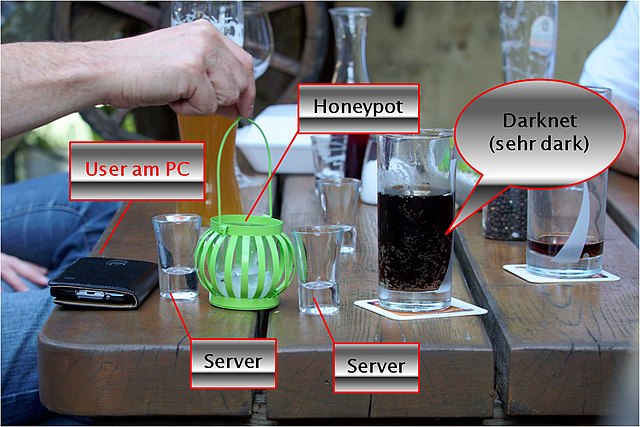
It is the dark web’s version of Wikipedia with a massive links directory. You will find all the necessary .onion links to access any content or service on the dark web. It will offer you an additional layer of encryption to access the deep parts of the internet. If you choose to visit the dark web, you must take the necessary measures to protect your privacy and security.
Detecting Tor Traffic On Your Network

However, anybody can sign up and start selling whatever they want on the website as they please. Established back in 2013, Dream Market is one of the smaller Darknet marketplaces, but it’s also one of the most thriving. All the sellers found on the site seem to be of a high-quality, and there’s a rating system among users so you can find what’s good and what’s bad. Law enforcement agencies keep an ear to the ground on the dark web looking for stolen data from recent security breaches that might lead to a trail to the perpetrators. Many mainstream media organizations monitor whistleblower sites looking for news.
Once the buyer confirms satisfaction, the funds are released to the seller. Dark markets include features similar to those found in legitimate e-commerce platforms, such as product listings, user reviews, ratings, and customer support. These features help create a sense of ‘trust’ among users, even in the criminal ecosystem. Freshtools is a unique marketplace in that it does not only provide the stolen data, but it allows criminals to purchase MaaS which can cause further damage to the victims.
Together, the software would mask IP addresses and encrypt online sessions so people could anonymously post on or browse the now non-operational Silk Road. Shortly after Xennt arrived in the Mosel Valley, his activities attracted the interest of a prosecutor named Jörg Angerer, who worked in the nearby city of Koblenz. Angerer, a genial and unassuming man who specializes in prosecuting cybercrime, encouraged a police investigation into CyberBunker. It is legal to host sites containing illegal activity, so long as the host is unaware of the content and does not actively assist the site’s owner in illegal behavior. A German police unit in Mainz spent about five years spying on Xennt, using digital and phone taps as well as undercover officers—including a man employed as a gardener at the bunker complex.
What Kind Of Content Is On The Dark Web?
With advanced dark web monitoring, threat intelligence, and brand protection services, we help you uncover hidden dangers, prevent data breaches, and safeguard your reputation. Our platform ensures that your brand stays one step ahead of cybercriminals, giving you peace of mind in an increasingly complex digital landscape. People have been organizing illicit trades via the Internet since the 1970s. Those early examples, though, were through closed networks, and the actual exchanges of money and goods generally had to take place in person. With the advent of crypto-currencies, it became not only possible to complete trades online without leaving a money trail but easy.
Government Monitoring
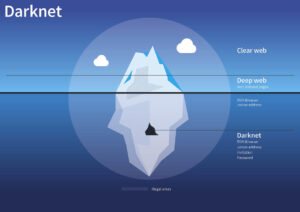
On the deep web, you can find such “private” information on web pages. So, that means that the number of pages increased by over 100 trillion in just over three years. Hypothetically speaking, Google may be aware of well over 200 trillion individual pages (these are obviously NOT all indexed in the search engine). So, even though it does exist on the internet, Google doesn’t index any of these pages or content. Radar Rundown Ad blockers are the best protection against disruptive ads.
Mega Market is a new yet popular shop on the dark web that reached a skyrocketing reputation after the closure of the Hydra market. It allows you to buy and sell a wide range of products and services with a good user experience. This site supports PGP encryption and two-factor authentication features. To access darknets, users typically need to download and configure the Tor Browser; a modified version of Mozilla Firefox that routes all traffic through the Tor network. This browser enables access to websites with .onion domain extensions, which are specific to the Tor network.
The platform is also used by governmental cyber departments to identify and track potential criminals or offenders. You can never be sure who’s really behind the other end of the line. In darknet mode, you can select friends on the network and only connect and share dark web content with them. This enables individuals to form groups and only share content in a highly anonymous network of darknet users who they know.
Cartel Darknet Marketplace
- A handful of dark web search engines that do index .onion sites include NotEvil, Ahmia, Candle, and Torch.
- Tor is a network of volunteer relays through which the user’s internet connection is routed.
- Some of the deep web sites do not use standard top-level domains (TLD) such as .gov, .com, .net, etc.
- This is the part of the internet known as the dark web, and it’s accessible via mainstream search engines such as Google.
You’re also open to threats like end-to-end correlation attacks, so while Tor is a lot more secure and private, it’s by no means completely safe. Bitcoin is also supported, and there are multiple payment methods similar to Escrow, so both the buyer and the seller are protected during the transactions, and nobody is ripped off by the other party. If you wanted to become a seller on the website, entry is open, and the marketplace will take a 2% commission on every sale with a vendor bond varying between the $0 and $250 mark. There are plenty of safety precautions as well to help protect customers.
Types Of Dark Web Sites (and What Really Goes On There)

Simply accessing the dark web and using the Tor browser may already raise government suspicion. Anyone can access the dark web, and it’s not that complicated to do so. Just remember, if you want to explore the dark web, be very careful.
ICE USWDS Footer Links
The creators assert that because their technique is so strong, even malware with root access could not determine the machine’s IP address. The only difference is that it passes your traffic through random nodes before reaching the destination. This means your activities cannot be traced or your browser history exposed.
It has an active forum and community along with an extensive user vetting process. Drugs were the most common and lucrative goods to buy on Silk Road — making up 70% of the products for sale. Other items for sale included banned energy drinks, hacking services, digital goods (such as malware and pirated software), and forgeries (such as fake licenses and other illicit documents). Legal goods and services like art, books, jewelry were also for sale. Silk Road operated via a hidden darknet feature in the anonymous Tor network.
#1 Install A VPN

Put simply, the deep web is all the information stored online that isn’t indexed by search engines. You don’t need special tools or a dark net browser to access most of the deep web; you just need to know where to look. Specialized search engines, directories, and wikis can help users locate the data they’re looking for. Onion sites aren’t really dangerous, but they could be when accessed through unfamiliar or suspicious links. Blockchain even has an HTTPS security certificate for even better protection.
He was formerly the Chief Financial Officer and a principal shareholder of Apollo Solutions, Inc., which was acquired by CNET Networks. Still, for those willing to put up with the inconvenience, the dark web provides a memorable glimpse at the seamy underbelly of the human experience – without the risk of skulking around in a dark alley. IBM Security X-Force, for example, reported that 29% of its ransomware engagements in 2020 involved REvil. The criminal groups that developed the malware gets a cut of the affiliates’ earnings, typically between 20% and 30%. IBM estimates that REvil’s profits in the past year were $81 million. The affiliates distribute the ransomware packages through the dark web.

Dark markets, on the other hand, are platforms within darknets where illicit transactions occur. These marketplaces facilitate the exchange of everything from stolen credentials and drugs to weapons and hacking tools. The anonymity and encryption provided in dark markets create a haven for cybercriminals and nation-state actors to buy and sell dangerous assets while evading detection. It was quite popular for selling a wide range of products and services. It offers impressive features, including PGP-signed addresses, payment via Monera, sticky and featured listings, and auto shops.
It encrypts your connection to prevent outsiders from being able to read your data and masks your IP address with one from a VPN server—so whoever’s looking can’t get any useful information. This process also prevents your ISP from seeing your data or where it’s going. Since the ISP can’t detect you’re accessing dark web URLs, it won’t trigger any alarms about your online activity.