You may be concerned about teenagers visiting the Dark Web, especially as press reports often link them with dangerous or illegal online activity. However, it is not always used for illicit activity and the problem does not come from the technology itself, but rather from the ways in which people use it. Being aware of the basic facts about these parts of the internet can help you to have open and realistic conversations with your child, especially if you are concerned about them using the Dark Web. The Internet Watch Foundation (IWF) removed more than 100,000 webpages showing the sexual abuse and sexual torture of children over the last 12 months – up by a third year on year. Without immediate intervention, deepfake nudes risk becoming an entrenched digital threat young people must endure.
The goal of an anonymous and privacy network, Tor, is not to engage in the extensive collection of data. However, data is required for understanding, monitoring, and improving the network. Furthermore, data will help to detect attacks against the network and possible censorship events. The BBC news website has a special .onion site, which you need to access via the dark web.
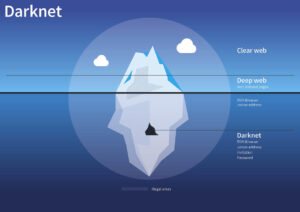
What Are The Different Parts Of The Internet?

The attorney stressed that McIntosh’s managerial role on the website was different from that of his codefendants. He said McIntosh mostly oversaw the site’s fantasy and roleplay rooms, where “sick people engage in a game” of pretend sexual abuse. While it is recognized that the darknet was initially used to create an application or modus for free speech, particularly in areas of political conflict, in reality, its anonymity has rendered much of the darknet a criminal marketplace.
Ready To Explore Web Data At Scale?
Sci-Hub is a massive database that eliminates the barriers to getting scientific knowledge. It contains millions of scientific research documents from around the world. The site seeks to liberate information by making it free to individuals and institutions. Since Hidden Wiki maintains all kinds of websites, ensure you don’t open something you don’t want to see. Even without monitoring your browsing activities, DuckDuckGo will offer decent answers to your questions. If you choose to visit the dark web, you must take the necessary measures to protect your privacy and security.
Hoaxes And Unverified Content
Overall, 41% of young people indicated they had heard of the term deepfake nudes, including nearly 1 in 3 (31%) of teens. Men and boys were more likely to have heard the term than women and girls (+9%). LGBTQ+ young people were also more likely to have heard the term than their non-LGBTQ+ peers (+20%). Deepfake nudes represent a stark evolution in image-based sexual abuse, driven by the rapid rise and accessibility of generative artificial intelligence (AI). This research sheds light on young people’s experiences with deepfake nudes, exploring their awareness, perceptions, and experiences with this growing threat. To read the complete research report and explore its findings in greater detail, please download the full report.
Finding victims depicted in child sexual abuse materials is already a “needle in a haystack problem,” Rebecca Portnoff, the director of data science at the nonprofit child-safety group Thorn, told the Post. Now, law enforcement will be further delayed in investigations by efforts to determine if materials are real or not. The access to technology and a connected community via the Internet has enabled the distribution, possession, and creation of child sexual abuse material (CSAM) to increase. Although previously seen as an unreliable, slow, and access-restrictive technology, the darknet is now an everyday tool for 2.5 million Internet users (Wise 2022). Home Internet connections and faster upload and download speeds have enabled a technology-driven revolution in the lifestyles of modern society. This is also accurate for individuals who seek to access on-demand CSAM and to communicate with likeminded persons.
The New York Times
We find that CSAM is easily available using 21 out of the 26 most-used Tor search engines. We analyse 110,133,715 search sessions from the Ahmia.fi search engine and discover that 11.1% seek CSAM. When searching CSAM by age, 40.5% search for 11-year-olds and younger; 11.0% for 12-year-olds; 8.2% for 13-year-olds; 11.6% for 14-year-olds; 10.9% for 15-year-olds; and 12.7% for 16-year-olds. We demonstrate accurate filtering for search engines, introduce intervention, show a questionnaire for CSAM users, and analyse 11,470 responses. 65.3% of CSAM users first saw the material when they were children themselves, and half of the respondents first saw the material accidentally, demonstrating the availability of CSAM. Help-seeking correlates with increasing viewing duration and frequency, depression, anxiety, self-harming thoughts, guilt, and shame.
Why Is The Dark Web Dangerous For Teens?
- Therefore, the legality of the dark web will mainly depend on how you use it.
- This article lists some of the best dark web websites you can visit securely.
- Surfshark supports unlimited simultaneous connections to protect as many devices as possible.
- The site, named Welcome to Video, was run from South Korea and had nearly eight terabytes of content involving child abuse – enough to store hundreds or even thousands of hours of video footage.
As I’ve previously said, it’s a good idea to keep your interactions with the dark web to a minimum, unless you can absolutely trust the people you’re dealing with. You’ll often see a sign in stores that says “look, don’t touch,” and it’s not a bad adage to bear in mind as you navigate around the dark web. Individual sites on the dark web look much like they do on the regular web, though a lot of them are a bit more rough around the edges. (Presentation and polish isn’t quite so important on this part of the internet.) Click on any website link, and it’ll appear on screen, with its address at the top. To get on the dark web, you need a browser built for the job, and the best in the business is Tor. Tor is a browser engineered for extra security and privacy, and can be used to navigate the normal, surface web as well as the dark web.
Types Of Online Sexual Exploitation
For example, it maintains your privacy and enables you to access untraceable content and services. The system is designed to provide enhanced security and privacy features. Its key features include kernel hardening, application firewall, package security, filesystem encryption, meta-proxy encryption, and binary integrity. Another essential security feature is that all incoming and outgoing data from the app is encrypted, including any private and public keys involved. These sites are a hybrid tutorial-underground where wannabe hackers ask questions and professionals sell their services or stolen data.
Case Studies: Child Sexual Exploitation
Overall, we have a growing understanding of the environment of these darknet forums on a technical and community level. Yet, there is an absence of research in understanding the risk and psychological profiles of these users and research to inform and design successful interventions to deter memberships to CSAM sites that encourage offending. Research on the darknet is not easy and requires a combined effort from LEA, academia, technology service providers, and non-govermental organisations.
The amount of AI-generated child sexual abuse material (CSAM) posted online is increasing, a report published Monday found. If that view gains traction, Fourth Amendment challenges about searches and seizures by the government could change how the center operates and how tech companies find and remove illegal imagery on their platforms. We propose an intervention strategy based on our observation that some CSAM users do indeed recognise their problem. Even when CSAM users are seeking CSAM, they are willingly visiting self-help pages and continuing to study cognitive behavioural therapy information.

Online Safeguarding: The Dark Web
As per the Global Commission on Internet Governance (Global Commission on Internet Governance 2015), “the darknet certainly is the seedy underbelly of the Internet. Its sordid nature is exemplified in a few stories about drugs, assassination, trolling and child abuse” (p. 2). Parents, please speak with your teens about the dangers of the darknet. If teens are sneaking around and doing suspicious things online, then start monitoring the sites being visited.