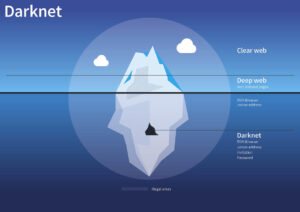
From Social Security numbers to bank logins and medical records, cybercriminals buy and sell stolen data every day. Criminals can steal your credit card numbers through formjacking—the practice of creating fake online forms to capture sensitive information. These forms may appear on legitimate-looking websites but are designed solely to steal your data. Crucially, she also outlines what service providers—including telcos, financial services, and insurers—can do to help protect consumers from carding in today’s shifting cyber threat landscape. When a hacker writes up new malware, steals a database, or phishes someone for their credit card number, the next step is often toward dark net marketplaces. These black markets allow buyers and sellers to make anonymous transactions using a combination of encrypted messages, aliases, and cryptocurrency.
How To Use Tools To Detect And Flare Up Potential Fraud
Enter your email(s) to receive a free exposure report detailing what information criminals have in hand and learn what you can do to protect yourself. Those details are useful for tactics like spearphishing specific people to try to steal their login credentials for personal or work accounts, researchers say. A Russian-language dark web shop known as BidenCash recently attracted attention from cybersecurity researchers by posting a leak — for free — of 2 million stolen payment card numbers. All information, including rates and fees, are accurate as of the date of publication and are updated as provided by our partners.
Which Darknet Markets Are Still Open
For example, requiring additional verification for purchases that deviate from a customer’s normal pattern, rather than forcing verification for every single transaction. We’re not just looking for individual red flags, we’re building comprehensive risk profiles based on dozens of different indicators. Businesses pass fraud-related costs on to consumers through higher prices. Automatic payments get declined, travel plans get disrupted, and sorting everything out with the bank can take hours. The Magecart group pioneered this technique, compromising thousands of online stores by exploiting vulnerabilities in popular e-commerce platforms.
Inside The Cybercrime Economy: How Threat Actors Operate Like Businesses
“By the time the data is in the underground, it’s gone through a number of stages to get there. So … how do we stop the data from ever being exposed or compromised in the first place, before it can be accessible by any criminals? … That’s’ where things like 3DS 2.0 and tokenization really come into play. So that if data is potentially compromised at an e-merchant site, for example, that data has no value if it’s compromised,” he explains. The card skimmer illegally captures the credentials of cards inserted into the machine.
Skimming Information From Fake Online Forms
Well, it is mostly misused by attackers for their criminal activities or it ends up on the dark web for sale. Cybercriminals often use the stolen financial data to make fraudulent purchases online or to compromise other accounts via credential stuffing attacks. Most scammers obtain credit card numbers and other financial data from various darknet forums. While stealing card data can sometimes be relatively easy, successfully using it is far more difficult. Transactions can be quickly flagged or blocked, making fraud attempts risky and unreliable. As a result, carding communities are developing new strategies to leverage existing online platforms and withdraw money from stolen credit cards.
Cyberint, the Impactful Intelligence company, reduces risk by helping organizations detect and mitigate external cyber threats before they have an adverse impact. A team of global military-grade cybersecurity experts work alongside customers to rapidly detect, investigate, and disrupt relevant threats – before they have the chance to develop into major incidents. The dataset included a mix of debit and credit cards, mainly from MasterCard and Visa, but also included American Express and JCB. This incident highlights the persistent threat of financial fraud on illegal platforms and underscores the urgent need for enhanced cybersecurity measures. Modern credit card fraudsters rely on specialized software frameworks to automate their operations.
Protect Yourself From Tax Scams
The proceeds from sales of card numbers are used for enabling organized crime and gang activities, weapons exchange, trafficking drugs and guns, and many other illegal activities, he says. Millions of customers’ card data have been compromised in the past decade. No matter how vigilant you are, there is nothing you can do to prevent a data breach on a merchant’s website, but using a virtual card can shield your actual card data from being exposed. Most banks and credit card vendors offer you the option to receive fraud alert notifications—email or text alerts—warning you of potential card theft. Scammers start by prompting users to download malware, which is often disguised as a harmless email attachment. Once it starts running on your machine, the malware collects data such as used keystrokes, browser history, and shopping habits.
If your card is linked to auto-pay services or has a high spending limit, the damage can escalate quickly—often before your bank even flags it as suspicious. To minimize the risk of payment data exposure, only shop from reputable retailers, use digital payment methods or one-time private cards, and protect your accounts with two-factor authentication. The shop offers stolen card data from around the world for as low as $0.15 per item and uses verification and automated checks to check the validity of the cards people put up for sale on the platform.
In fact, the overwhelming majority of leaked credit cards in past months originate from Telegram channels. Carding groups and channels reach up to tens of thousands of members, as they are easy to navigate and readily accessible. This stolen information is exploited by threat actors for financial gain through unauthorized charges, account takeover, and identity theft. The resulting financial loss is tremendous not only for the individual victim but also for the financial provider and any involved organizations. Yes, you should be concerned if your credit card number is found on the dark web as it puts you at a higher risk of fraudulent transactions and financial theft. However, being proactive by cancelling the compromised card, monitoring your financial statements, and setting up alerts can mitigate the risks.

For fledgling criminals who don’t know how to use stolen credit cards, there are plenty of free and paid tutorials for carding on the dark web. These details often land there after data breaches, phishing attacks, or malware infections that steal information from unsuspecting users. If your credit card number appears on the dark web, it means someone has likely leaked or stolen it—and now it could be traded, sold, or used without you even knowing about it. Stolen credit card numbers refer to the unauthorized details of credit or debit cards that have been obtained through various means, often illegal. These numbers allow thieves to make fraudulent transactions, leading to significant financial losses for individuals and businesses alike.
Carding is packaged and sold like a legitimate business within criminal communities—often mimicking the tone, structure, and customer service you see in e-commerce. Credit card hacking can take many forms, and it’s essential to understand the different types to protect yourself. Data breaches have become a fact of life, but taking proactive steps can help minimize the damage.
- The news that thousands of Australians have been affected by a credit card data dump online comes amid heightened fear of hackers in the wake of the Optus cyber attack.
- Here’s a breakdown of what your personal details might go for on underground marketplaces, according to the Dark Web Price Index by Privacy Affairs.
- Our platform alerts security teams when an organization’s sensitive data is found.
- Only through collective efforts and advancements in cybersecurity can we hope to mitigate the impact of these nefarious activities and safeguard the digital landscape for future generations.
Million Devices Hit By Infostealers—Bank Cards Leaked To Dark Web
We help millions of individuals and nearly 200,000 corporate clients protect what matters most to them. Hackers often monitor unencrypted public Wi-Fi networks for opportunities to intercept sensitive information. Logging into your bank or shopping online while connected to public Wi-Fi can expose your credit card details. Credit cards, Paypal accounts, and fullz are the most popular types of stolen information traded on the dark web, but they’re far from the only data worth stealing. Sales of passports, driver’s licenses, frequent flyer miles, streaming accounts, dating profiles, social media accounts, bank accounts, and debit cards are also common, but not nearly as popular.

Learn how our savings accounts and other financial products can support your financial goals while keeping your money safe. Due to limited data on credit cards from other countries, we were unable to adequately compare prices for credit cards from different places. The average price of a cloned, physical card is $171, or 5.75 cents per dollar of credit limit. You can also limit your risk by being picky about your ATMs, where criminals sometimes install card skimming devices. These are hard to detect, but only using ATM machines inside banks or other physical buildings offers some protection, Thomas says. Some of the more sophisticated underground shops even have a money-back guarantee on some of the data they sell.
Or they’ll commit “card-not-present fraud,” by hacking a website and stealing the online card information that gets entered into the checkout page. BOWLING GREEN, Ky. (WBKO) – A homeless man told police that he had spent last month using stolen credit card numbers to stay in a hotel, according to court records obtained by WBKO. The threat actors announced the credit card dump yesterday on new URLs BidenCash launched late last month in response to DDoS (distributed denial of service) attacks, so it could be a way to promote the new shop domains.
One Million Credit Cards Leaked In A Cybercrime Forum For Free
Collecting used keystrokes is how hackers typically guess credit card numbers, PINs, and passwords. Credit card details can be sold as digital items on the dark web, with the basics costing around $17.36. Physical cards, on the other hand, are cloned from stolen online details and can be used to withdraw cash from ATMs. These checkers are often offered and sold on the dark web, and are complimentary tools that individuals and organizations use to verify credit card information.

Payment networks like Visa and Mastercard keep lowering the thresholds for chargeback and CNP credit card fraud and hold merchants accountable with increasing fines and penalties. And payment processors can block all transactions if carding attacks are not handled quickly, which can result in lost revenue to the retailer. Financial data can leak in many ways—through phishing attacks, data breaches at online services, or poor account security. Even in regions like the EU, where banks are legally required to implement strong customer authentication, criminals continue to find ways to bypass these safeguards. Card-not-present (CNP) fraud occurs when hackers use stolen credit card numbers to make online purchases.
Category #1: Details Needed For Fraudulent Online Purchases
In the ever-evolving landscape of cyber threats, businesses face not only financial losses but also significant reputational damage when targeted by fraud actors on the dark web. Monitoring the deep and dark web becomes imperative for proactive defense against such threats. Lunar, our dark web monitoring tool is designed to empower individuals and businesses in this battle against cybercrime. With features like real-time alerts, data breach monitoring, and comprehensive dark web post monitoring, Lunar helps organizations stay ahead of deep and dark web threats in an increasingly hostile digital environment. Regularly review your credit card statements and bank transactions for any unauthorized activity.
Monitoring The Dark Web
Several new cybersecurity scams and malicious activities originate from these underground forums. Threat actors discuss and share knowledge on new hacking techniques and tools. Some senior threat groups even provide tutorials and share their attacking procedures to the budding hackers. Threads is a feature-rich platform, and threat actors are clearly using Threads’ features and functionality, including taking advantage of suggested content, polls, and trending social tags to promote stolen financial data. In most cases, actors post the details of a limited number of stolen cards as a way to advertise that they have a larger and constant stream of fresh cards available for purchase.