According to Recorded Future research1, out of 55,000 onion domains discovered, only 8,400 have a live site. Though the dark web offers anonymity for journalists and activists in oppressive regimes, it raises many ethical concerns. Knowing about various types of ransomware and common hacks can help you better prepare to spot cybersecurity threats on the dark web.
Get Out Of The Audit Committee: Why CISOs Need Dedicated Board Time
Our rigorous research and testing have revealed revealing truths and busted myths. We’ll navigate this intricate maze with you, uncovering its secrets while ensuring your online safety. Download Tor Browser to experience real private browsing without tracking, surveillance, or censorship.
How Do I Access Onion Sites?
If you ever decide to explore the dark web, protecting your identity is crucial. Most people start by using the Tor Browser, which hides your IP address. The story of dark web marketplaces kicks off with Silk Road, launched in 2011.
How Did We Select These Best onion Sites?
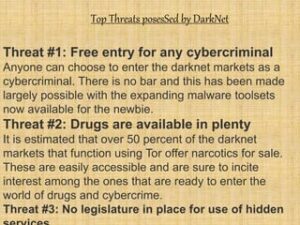
Since most Tor websites are non-indexed and unregulated, the probability of scams is much greater on the dark web. Malicious actors can prey on unsuspecting users without leaving much of a digital footprint on Tor, so it’s often just a matter of time before you run into one. The Tor Browser can take you to all kinds of questionable, dangerous, and potentially illegal content.
Legitimate Use Cases For The Average User
However, not all the forums and social media sites are legal on the dark web and often include shocking conversations and pin boards by anonymous users. Dark web sites are hidden by non-indexing, making them completely anonymous. You’ll need a purpose-built browser that uses The Onion Router (TOR) to access dark web content. Because of their anonymity, dark web sites are breeding grounds for illegal activity and transactions.
It’s only possible to access onion sites through the Tor browser or by setting up some special network configurations. SecureDrop is a really awesome Tor service that can be used to share information without revealing your identity. Many news publications (including many of the ones listed above) use SecureDrop on their .onion sites.
Radar Rundown Hiding your IP address is one of the best ways to protect your online activities from … The deep web is not a series of sites but a storehouse of records, including email accounts, medical records, private messages, and more. It saves a select version of each page and preserves it even after upgrades have taken effect on the original site. Accessing tunnels is illegal and dangerous, which is why records of these “adventures” can only be found on the dark web. If you want to access this site, do it only for fair purposes and with proper security measures.
Then individual applications must each be separately configured to work with I2P. You’ll need to configure your browser’s proxy settings to use the correct port on a web browser. Another vital precaution is to ensure that your .onion URLs are correct. Onion URLs generally contain a string of seemingly random letters and numbers. Once you are certain that you have the correct URL, save it in an encrypted note—the Tor browser will not cache it for later.
These search engines work best if you already know what site you’re looking for, not for general browsing. One option is to try DuckDuckGo’s .onion version, which is great for privacy. Other options include Ahmia and NotEvil, which focus on listing .onion links. Using the ProtonMail .onion site offers security and privacy advantages.
- Freenet was originally intended to provide a way to anonymously interact online, providing ways to communicate, exchange information and files, and to otherwise communicate incognito.
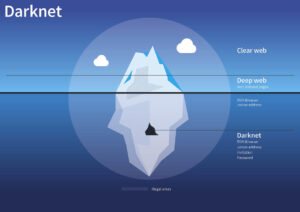
- The dark web, by contrast, is configured on darknets — online networks that can be accessed only with special software and techniques.
- Additionally, I2P doesn’t rely on hidden directories that serve as a resource for .onion domains.
- Without further ado, let’s take a look at some of the best tor and onion links for you to check out, in no particular order.
- Some popular marketplaces include AlphaBay (before it was taken down) and Hansa.
Anonymity Is In Your Hands
If this sounds similar to The Wayback Machine, the concept is indeed the same. However, The Wayback Machine allows website owners to block their sites from being archived, while archive.today does not. ProPublica has a reputation for unwavering investigative journalism. In 2021, they showed how tax rates benefit the rich, and they relied on stolen or leaked IRS documents to do so. In addition to the surface web, ProPublica also hosts their site on the dark web, because they want to make sure that everyone can access their reporting. Additionally, check the Block pop-up windows and Warn when websites try to install add-ons settings.
What Is A Cloud Access Security Broker?
Ensure you have used prepaid and unidentifiable credit cards when purchasing on the dark web. Furthermore, it’s critical to understand that Whonix is not a stand-alone browser. It is a component of Whonix, an operating system that functions as a whole inside a virtual computer.
While Tordex aims to provide unrestricted access to dark web content, you should exercise caution as the lack of censorship may lead to exposure to sensitive or illegal material. If you get a reliable vendor, you should procure the services to stay safe when accessing the dark web. You can also run a dark web scan to see if your information has been leaked on the dark web. This dark web monitoring will help you track illicit activities and minimize the risks of cyber-attacks.
That’s “a special-use top level domain suffix designating an anonymous hidden service reachable via the Tor network,” according to Wikipedia. Browsers with the appropriate proxy can reach these sites, but others can’t. The terms “deep web” and “dark web” are sometimes used interchangeably, but they are not the same. Deep web refers to anything on the internet that is not indexed by and, therefore, accessible via a search engine like Google. Deep web content includes anything behind a paywall or requires sign-in credentials.
Marketplaces
Millions of customers’ personal data, including names, addresses, bank account and credit card account information, and many other forms of sensitive data. Naval Research Laboratory mathematicians and computer scientists in the mid-1990s. The U.S. Army developed “onion routing” to protect intelligence communications online. Later on, the underlying Tor code was released into the wild under a free license, leading to the formation of the Tor Project. In 2008, the first Tor Browser was released, making it easier for any internet users to access the dark web. The users of the dark web are typically aiming to block governments from snooping on them.
When you install a VPN, all of your activities on the dark web will be hidden from unwanted snoops from your ISP or the FBI. The VPN is a second layer of extra protection, on top of the protection that the Tor network already offers. The same anonymity that publishers enjoy on the dark web can be utilized by users who want to read the available information. Again, people who live in countries where the freedom of the internet is limited, for example in China, can really benefit from using Tor.
Is Accessing The Dark Web Illegal?
It can only be used to access hidden services specific to the I2P network. I2P cannot be used to access .onion sites because it is a completely separate network from Tor. 2014 saw the continued growth of the dark web, a collection of underground websites that allow people to engage in often-illegal activities beyond the reach of law enforcement. Here’s what the dark web is, how it works, and why it’s not going away any time soon. The Hidden Wiki is a surface website offering a collection of dark web links. Before visiting any dark websites, get comprehensive cybersecurity software to help protect yourself from threats you may encounter.
Scammers and criminals are lurking everywhere to take advantage of the unwary. Follow the pointers below to avoid becoming a victim if accessing the dark web. I also like that the security guides are user-friendly — the format is easy to scan, complicated terms are explained very well, and there are videos and screenshots.