It’s divided into commercial links (from crypto services to gambling sites) and non-commercial links (like social media). As always, use Tor Links with care, as it includes onion links to dubious or illegal activity. Despite the uncertainties surrounding the future of cryptocurrency on the dark web, it is crucial to remain vigilant in combating illegal activities online. Law enforcement agencies and cybersecurity experts must stay one step ahead, constantly adapting and evolving their strategies to counter the ever-changing tactics employed by malicious actors.
Notable Crypto Money Laundering Cases
The dark web isn’t just one sketchy marketplace hiding in a corner of the internet; it’s more like a messy, unregulated community with everything from freedom fighters to full-blown cybercriminals. The Dark Web is the part of the deep web that is not indexed by search engines, like Google or Bing. For this reason, you cannot browse through these sites using your default search engine. Just like Google, the dark web has some search engines present on it. Though they have their limitations, most of the time you’ll see irrelevant or spammy links for your search results. Using the ProtonMail .onion site offers security and privacy advantages.
Is It Illegal To Enter The Dark Web?

This absence of the placement stage enables criminals to bypass one of the riskiest stages of money laundering. It also presents a significant challenge for authorities and compliance professionals trying to detect and prevent cryptocurrency money laundering. BitConnect and OneCoin are two notorious cases of cryptocurrency fraud that resulted in massive losses for users. BitConnect, which promised users substantial returns through a Ponzi scheme, collapsed in 2018 due to legal issues with US-based regulators. The dark web comes with its own set of tools and services, including web browsers and search engines (which I’ll get on to in a moment).
Verified Social Channels And News Sites
- You won’t find any “hidden” stories here—it’s the same content as the normal web edition—but users in countries with government censorship will appreciate having a secure way to access it.
- A site founded by a Swedish anti-copyright group used for large file sharing of digital content such as entertainment media and gaming.
- They know how to process the information and get it to the correct law enforcement agencies internationally.
- The Torrez market is one of the biggest dark net marketplaces, also called a community-driven marketplace.
- Law enforcement agencies around the world are cracking down on illicit activities conducted through cryptocurrency transactions.
Xinxi Wang is a director of Litecoin Foundation, Developer of Litecoin Core and CEO of Coinut Exchange. We speak about price predictions, MimbleWImble, Monero and a lot more. Given that the underlying technology has matured enough, the Litecoin team just started to work on CT. Its impact on Litecoin can be huge, and these QAs should answer many of your questions. However, the implementation of these recommendations has been met with varying levels of success. While some countries quickly adopted the guidelines, others lagged.
Telegram channels supplement traditional onion sites, blurring lines between the dark web sites and more mainstream communication tools. Fortunately, researchers stumbled on a poll with hundreds of votes on one of the most popular Dark Web criminal forums. The poll showed that forum users would have preferred the site to support Monero and Dash as payment systems in the future, showing Monero’s rising popularity. Most legitimate users are transitioning from viewing Bitcoin as an alternative digital payment system to a commodity, and the same can be said for cyber-criminals.
Litecoin News
Whether you’re looking for marketplaces, discussion forums, or other resources, Daunt Link is your go-to directory. “I don’t know that I have an immediate aversion to privacy coins. I do, however, feel like there needs to be some regulation around it,” he said. Cryptocurrency analytics firm CipherTrace filed two patents in 2020 for Monero tracing technology and released “tracing virtualization” tools last summer for qualified government agencies and financial institutions.

Government Monitoring
Also referred to as fraud pack, darknet pack, starter pack; Collection of technical resources to learn how to start crime on the darknet. A cryptographic protocol offering privacy and security by end-to-end encrypting instant messages with additional security measures. Acronym for OPerational SECurity; The standards and process a person or organization should implement to ensure that a security breach does not occur.

Darknet Market
Part of what makes the dark web the dark web is that you can’t access it through your normal web browser, nor can you look something up on it via a Google search. The dark web, which is what I’m discussing here, is a small subset of the deep web, and refers to websites that are specifically trying to stay out of sight. Initially released in 2014, Monero (also known as XMR) is a type of cryptocurrency often referred as a “privacy coin”; it has been built first and foremost with privacy in mind. It also has a substantial development community and maintains a strong base of privacy advocates and cypherpunks. Unusually enough, the brainchild of Charlie Lee, Litecoin, is also gaining popularity on the dark network.
However, most are outdated and have not kept up with the changing landscape. For example, DuckDuckGo is the most popular but often shows repetitive results and is sometimes unrelated to the question. The VPN will protect your traffic when you connect with military-grade AES 256-bit encryption. This is high-level protection; no one can intercept your data or activities.
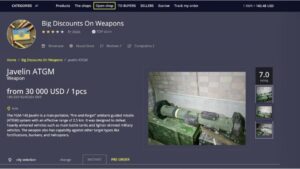
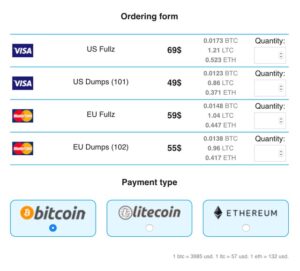
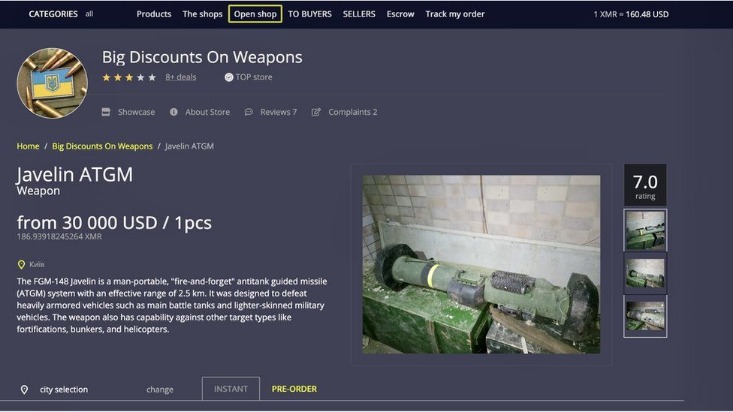
Cryptocurrency is ideal for illegal operations, providing the necessary level of anonymity. Tracking a wallet’s owner is extremely difficult, despite the fact that in the blockchain everything is transparent and open. There’s a significant risk to dark web users of being exposed to malware (malicious software) infections. There are several programs that hackers frequently use on the dark web. These high levels of anonymity increase the opportunity for the “bad guys” to sell drugs, stolen IDs, credit cards, weapons, and many more compromised products or information.
Does Tor Hide Your IP Address?
For a local machine configuration, he recommends a computer purchased for cash running Linux, using a local Tor transparent proxy. For operations security he suggests avoiding storing conversation logs, varying writing styles, avoiding mobile phone-based tracking and leaking false personal details to further obfuscate one’s identity. The months and years after Silk Road’s closure were marked by a greatly increased number of shorter-lived markets as well as semi-regular law enforcement takedowns, hacks, scams and voluntary closures. Finally, once the relevant sites have been located and access gained, there is still the serious challenge of monitoring the dark website to effectively gather usable intelligence.
Internet forum that centers around the posting of images and comments around a specific topic where identity is kept anonymous, see chan. Acronym for Individual Identification Number; used in reference to bank and/or credit accounts. Practice of taking data and inputing it into a cryptographic hash function to produce a hash value. An individual who uses technical knowledge to solve problems, gain access, break into systems, or take information for nefarious purposes or social-good motivations for themselves or on behalf of a group or government.
Naval Research Laboratory mathematicians and computer scientists in the mid-1990s. The U.S. Army developed “onion routing” to protect intelligence communications online. But human trafficking, illegal pornography featuring underaged victims, money laundering, and assassinations are also examples of the darkest corners on the dark web. That means that only 0.024% of all the known pages are findable in Google’s search engine. The users only have access to a fraction of the available data and web pages. Dark web forums are online platforms that can only be accessed using anonymous networks, mainly Tor….
While people and organizations do host legitimate and useful sites on the dark web, it’s still best to tread cautiously. Despite Tor’s privacy-focused design, malicious entities are more likely to target your data in transit and on .onion sites. Using Tor to access dark web links isn’t illegal, but your ISP will notice, and others may too. It’s, ironically, more conspicuous than using popular browsers and sites. It’s a hidden collective of sites that you could only access through a special browser.