Launched in 2023, STYX focuses on financial crime, providing stolen credit card data, hacked bank accounts and access to various cryptocurrency laundering tools. Silk Road quickly grew into the largest darknet market, handling hundreds of millions in transactions. But in 2013, law enforcement traced Bitcoin activity, monitored DPR’s forum posts, and exploited server vulnerabilities to identify Ross Ulbricht. He was arrested in a San Francisco library while logged in as site admin. Darknet marketplaces emerged around 2011, with Silk Road setting the standard for how these platforms operate. Built on Tor, these sites mask IP addresses by routing traffic through encrypted relays, ensuring anonymity for both buyers and sellers.
Silk Road Assets And Bitcoin
In addition, it ensures that no record of communication is stored. The deep web is the part of the internet you can’t access through search engines like Google and Bing. Also referred to as “non-indexed” content, it’s any content hidden behind some kind of access control such as a log-in or code word. It contains 7,500 terabytes of information, compared with only 19 terabytes of information in the “surface” web. To look at it in a different way, it makes up between 90% and 95% of the internet.
Avoid Downloading Dark Web Files
Use it to search the normal internet from the privacy of your Tor Browser. Torch is one of the oldest and most popular onion search engines on the dark web, serving over 80,000 requests per day. Torch is funded primarily through advertising—purchased in BTC, of course—which is why you’ll find the front page blanketed with old-school banner ads of dubious origins. The three nodes separate your IP address from your destination and enable two individuals to communicate without either party, or any middleman, knowing who the other is.
The threat can extend to your entire network of devices connected to the internet. Since malware lingers across the dark web, your device can easily become infected, even if you are an unsuspecting user. In some countries, evading government restrictions to seek new political ideologies is punishable. For example, China uses the Great Firewall to block access to Western sites. Accessing blocked content can result in being placed on a watch list or imprisonment.
Features Of Archetyp Marketplace

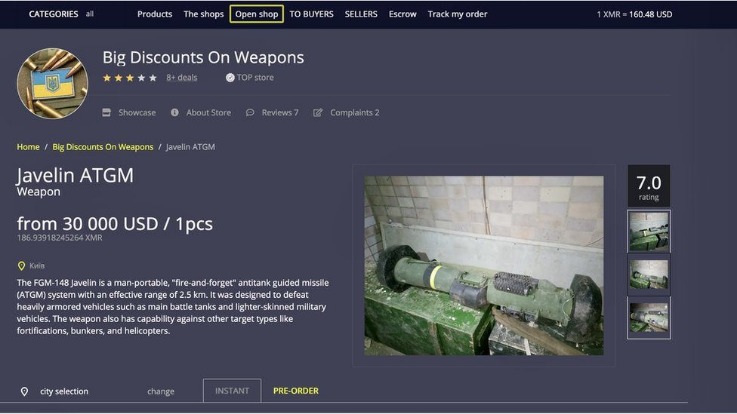
But anything that’s against the law on the regular web or offline is also illegal on the dark web. This includes buying or selling illicit goods, illegal transactions, and downloading copyrighted material. Tor Metrics is a set of tools and data provided by the Tor Project that offers insights into the performance, usage, and activity of the Tor ecosystem and its nodes.
Hidden Services Directories, Hosting, Portals, And Information
If you are looking for dark web links that deal in drugs, you can consider this one as it is dedicated to only drugs. Before making an order with them, check reviews about Green Road in other dark web forums. Liberty6o7lubin4t2nzyebylmk4l4xfw6kk2o5xhg3fahqoatfiprqd – Darknet Market – Liberty Market – It was launched in January 2021. Can be used to buy everything except weapons, illegal porn, Fentanyl and personal info.
Archive, Index And Torrent
A VPN can mask your Tor usage from your Internet Service Provider (ISP), but be cautious — some VPN providers keep logs that could compromise your anonymity. Updates often include security patches that protect you against vulnerabilities and potential breaches. While browsing online, you might have noticed that the websites you are visiting have URLs starting …
- Keep in mind that while Tor anonymizes your browsing activity, it is not foolproof.
- We understand the curiosity to venture into the dark web, but you also need to understand that it’s never safe to venture into this portion of the internet without fully understanding what it entails.
- A favorite of journalists and their anonymous sources, SecureDrop makes it easy to share confidential information without revealing your identity.
- Blockchain.info (now Blockchain.com) is a popular cryptocurrency wallet and blockchain explorer service (one of the first sites to launch on the dark web).
- The dark web is filled with phishing sites, clones, and scams designed to steal your funds or compromise your identity.
- When you try to connect to a .onion website, Tor will route your traffic through three or more randomly chosen nodes before it reaches your destination website.
Also, set up two-factor authentication (2FA) to add an extra layer of protection in case someone manages to figure out your password. Moreover, if you must use public Wi-Fi, ensure that you use a VPN to mask your browsing activity and keep yourself secure. The fact that there are no real regulations as well as authorities to monitor transactions, you’re always on your own, and you’re a potential target and victim of a scam or fraud. The dark web is famous when it comes to hosting as well as spreading explicit and illegal content.
Noteworthy features included a lack of withdrawal or deposit limits, a 5% fee for sellers (with no fee for buyers), and private listings for custom orders or discounts. WHM also emphasized security through measures like end-to-end encryption for messages, mandatory two-factor authentication based on a word list, and the encryption of sensitive data. The market’s commitment to privacy extended to the minimal retention of plaintext information and the encryption of various elements, including messages, support tickets, and order details. With an estimated sales volume of up to $120 million, the administrators may have profited nearly $5 million. White House Market implemented user-friendly features, such as a bug bounty program, fast customer service, and a simple design without unnecessary elements. The market operated in English, with limited support in Spanish or French, and accepted Monero as the exclusive payment method.
Accessing Onion Sites On Android
Apart from the dark web markets that are operating online today, some raided platforms influenced many markets. The Abacus Market links to the new dark web marketplace sections and took over much of the vacuum left by the AlphaBay takedown. Believe it or not, some dark web marketplaces have pretty advanced systems for building trust. Sellers often need to pay a deposit to prove they’re serious, and they build their reputation through positive reviews.

Fraud And Hacking Services
Major entities (like governments or large corporations) may still analyze traffic patterns. Always remain vigilant about the risks involved with risky behavior, even when browsing through Tor. Downloading files from the Tor browser can compromise your anonymity. Malicious files might bypass Tor’s security, giving away your real IP address.
Best Practices For Safe Darknet Market Access
Consider the fact that cyber criminals routinely change their nicknames, e-mails, digital currency accounts, and the ICQ numbers they use in forums. Not only do they change these accounts and identifying numbers, but they also use different combinations of the information in each forum they participate in. We also learned that the communication methods used by these criminals are, to them, a social outlet as well. Just as often as they are speaking about malware, crimes, and goods for sale, they are talking about their families, their girlfriends, their vacations, and their cars.
Wallet-less mode available, optional wallet available as well. Vending allowed for $250.00 (waived for established vendors.) Very filter-rich search panel for faster and more specific product-searches. This is a categorized list of notable onion services (formerly, hidden services)1 accessible through the Tor anonymity network. Defunct services and those accessed by deprecated V2 addresses are marked. Wherever you go online, but especially if you’re on dark web websites, using a VPN helps you secure your communication data and protect personal information you send or receive.
This is particularly important as whistleblowers may face severe repercussions, including retaliation, legal actions, or harassment. In summary, the Tor Browser is your gateway to the darknet, providing a secure and anonymous way to explore and access resources that are otherwise hidden from the standard internet user. Whether for research, social interaction, or simply the allure of the undiscovered, understanding and utilizing the Tor Browser is crucial for anyone looking to venture into this obscure online realm. The Tor Browser is a unique web browser designed specifically to provide users with privacy and anonymity online. Built upon the Tor network, it allows individuals to browse the internet without revealing their location or identity by routing their connection through a series of volunteer-operated servers worldwide.



