Just Another Library is one such service, with a wealth of books covering computer programming, science, and niche hobbies (sailors’ knots, anyone?). It also offers works of art, course material, and audiobooks for download. Following the NYT, the BBC launched a dark web “mirror” of their international edition in 2019.
Cryptocurrency

With listings denominated in both Bitcoin and Canadian dollars, and a valuation around $3 million, it provides a microcosm of how local cybercrime ecosystems thrive. Telegram channels now host everything from combolist dumps (email-password pairs) to botnet rentals and credit card fraud tutorials. Botmasters use Telegram to rent access to zombie device networks, while criminals market phishing kits, SIM swap guides, and malware deployment tools.
What To Do If You See Something Illegal
While some of these markets were shuttered by law enforcement agencies – some took the easy way out with exit scams. Here are some of the now-defunct dark web markets that were notorious for cybercrime. Some are looking for illegal stuff they can’t buy elsewhere, like drugs or counterfeit documents.
What Happens On Dark Web Forums?
Readers interested in ethical and legal perspectives can look to investigative outlets such as ProPublica or The Intercept. Both cover censorship, surveillance, and the ways journalists use onion domains to protect sources. For those studying technology, academic research papers on anonymity networks provide technical depth and highlight ongoing developments.
It’s divided into commercial links (from crypto services to gambling sites) and non-commercial links (like social media). As always, use Tor Links with care, as it includes onion links to dubious or illegal activity. The return or influx of cybercriminals to dark web forums is expected to intensify competition among these resources. To stand out and attract new audiences, forum operators are likely to start introducing new features and improving conditions for data trading. These may include automated escrow services, streamlined dispute resolution processes, and improved security and anonymity measures. Data released by social media companies shows that millions of pieces of drug-related content are already taken down every year.
- Smaller boards exist as well, many serving journalists, researchers, or activists.
- A top-of-the-line VPN network that ensures maximum security while accessing dark sites online.
- These cases reveal both the risks of relying on anonymous markets and the determination of authorities to shut them down.
- Also, it offers discussions about software vulnerabilities, malware, and leaked databases.
- She yearns to know everything about the latest technology developments.
The 10 Biggest Dark Web Markets In 2025 – Updated List & Security Insights
When you use the Tor Browser to visit a dark web site, your data doesn’t take a direct path. Instead, it’s wrapped in several layers of encryption and sent through a chain of at least three relays. The region has seen an increase in these threats due to the current geopolitical situation, which is likely to continue to rise if tensions do not ease. Both stealers and drainers are likely to be increasingly promoted as services on the dark web. Malware-as-a-Service (MaaS) – or “subscription” – is a dark web business model that involves leasing software to carry out cyberattacks. Typically, clients of such services are offered a personal account through which they can control the attack, as well as technical support.

How To Access Onion Sites
It helps us stay more vigilant, better protect ourselves, and make informed decisions online. For several years, Yahoo was at the apex as the internet’s best web service provider, offering… Moreover, it’s essential to provide the company staff with enough training as well as defined objectives of what they should look for to bolster the monitoring efforts. It’s a platform for both beginners and elite hackers where they share knowledge on a wide range of topics like carding and advanced hacking techniques. Perhaps that’s their option for generating consistent traffic and a steady influx of new members.
For example, you can find information unavailable to the public and share data privately while protecting your online identity. Note that most dark web transactions are carried out using Bitcoin or other cryptocurrencies. The Silk Road was a famous dark web marketplace where users could buy and sell goods and services anonymously. All the payments were made through cryptocurrency, further enhancing marketplace anonymity. The users on this site can review and rate the products that promote reliable and fraudster vendors.
We expect to see the number of attacks through contractors leading to data breaches at major end targets to continue to grow in 2025. Cloud platforms and IT services often store and process corporate data from multiple organizations, so a breach at just one company can open the door to many others. It is worth noting that a breach does not necessarily have to affect critical assets to be destructive.
In 2025, the darknet continues to provide a secure platform for the exchange of goods, with drug trade being one of its most prominent sectors. The best darknet markets have evolved to prioritize user safety, transaction efficiency, and product quality. These platforms rely on advanced encryption and decentralized systems to ensure anonymity and reliability for both buyers and sellers. In 2025, dark web markets continue to grow more sophisticated, leveraging cryptocurrency as their backbone for financial transactions. These hidden digital spaces host a variety of illegal and illicit activities, from drug trafficking and weapons sales to data breaches and financial fraud.
Is It Worth Monitoring Dark Web (and Deep Web) Forums?
Other countries take a neutral view, punishing only crimes committed through hidden services. Because of this variety, users should always check their local laws before exploring the hidden web. By giving both publishers and readers a safe meeting point, onion services extend the principle of free speech into the digital age.
- This diversification reduces dependence on centralized markets and increases the resilience of criminal networks.
- Although the Tor browser has sufficient encryption, combining it with a VPN offers better protection.
- Moreover, this shop provides detailed statistics about each user profile on the platform, giving users a better idea of the vendors for the buyers and vice versa.
- The shutdown of Archetyp, a major dark web drug market, demonstrates that law enforcement takedowns have only short-term effects, as such markets quickly re-emerge and adapt.
- These platforms keep changing their addresses to avoid DDoS attacks or law enforcement agencies.
- These groups use dark web platforms to sell stolen secrets, acquire hacking tools, or coordinate with other criminal organizations.
The integration of multi-signature wallets and escrow services further minimizes risks, ensuring that both buyers and sellers are protected throughout the transaction process. These features have significantly reduced instances of fraud, making darknet markets a reliable option for drug trade. One of the key features of top-tier darknet markets is their use of Tor networks, which provide users with a high level of anonymity. By routing traffic through multiple nodes, Tor ensures that IP addresses are concealed, reducing the risk of exposure.

Acronis Cyber Protect Cloud: New Version C2505

The deep web refers to all online content not indexed by search engines, such as virtual private networks and internal business systems. Ransomware threat actors use malware to lock users out of their systems, demanding payment to restore access. These groups often operate on a ransomware-as-a-service (RaaS) model, renting their tools to affiliates in exchange for a share of the profits. Cybercriminals want platforms that are there to stay and not taken down by authorities anytime. Dark web community channels are always evolving to ensure that they evade law enforcement agencies.
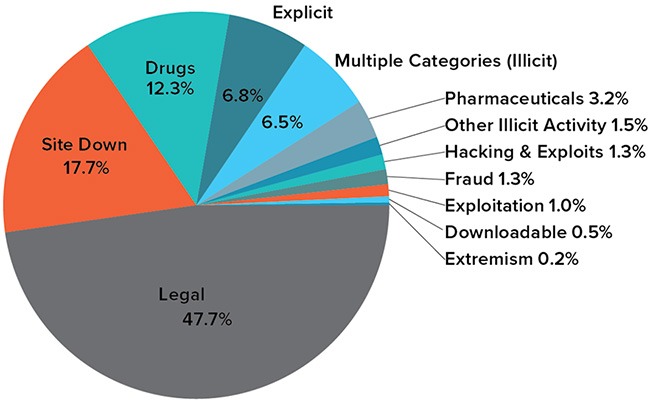
Several media productions, intelligence companies, hackers, snoopers, and whistleblowers use the dark web for their respective tasks. Moreover, some users use this hidden part of the internet to stay away from prying eyes. However, as the name indicates, this shady part refers to hosting illegal and inappropriate activities, including drug selling, hacking, etc.
These platforms utilize cryptocurrencies to conduct anonymous transactions, complicating efforts by law enforcement to trace illicit activities. The proliferation of such marketplaces has led to a 60% increase in untraceable illegal transactions since 2023. One of the key features of these markets is their use of Tor networks, which anonymize user activity by routing traffic through multiple nodes. This ensures that transactions remain untraceable, providing a layer of security unmatched by traditional online platforms. Additionally, many markets now integrate PGP encryption for communication, further safeguarding sensitive information.
Although Telegram introduced AI-powered moderation in late 2024, its impact has been limited. Many cybercriminal groups have simply migrated to platforms like Signal, Discord, or decentralized communication protocols. Get the latest updates on privacy, plus expert tips, and security guides to up your digital protection game. Behind the big revenue numbers are thousands of individual vendors, each running operations that range from small side hustles to large-scale enterprises.
Saheed Aremu passionately advocates for digital privacy and cybersecurity in the modern digital age. As one of PrivacySavvy’s resident VPN experts, he guides readers on protecting their online information and anonymity. Saheed earned his degree in Technology and Ethics from the University of Lagos in Nigeria. Since then, he has dedicated his career to writing extensively about crucial infosec, data privacy, and cybersecurity topics.