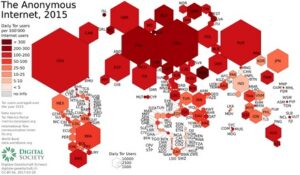
Again, people who live in countries where the freedom of the internet is limited, for example in China, can really benefit from using Tor. Later on, the underlying Tor code was released into the wild under a free license, leading to the formation of the Tor Project. In 2008, the first Tor Browser was released, making it easier for any internet users to access the dark web. The dark web is infamous for containing sites such as Silk Road and other marketplaces where users could potentially buy drugs and/or weapons, stolen credit cards, IDs, and much more. The dark web (often referred to as the “dark net”, “black web”, or “black net”) is a small section of the deep web that is hidden and kept inaccessible to regular internet users on purpose.
So, you risk being flagged or investigated for visiting certain sites, even without criminal intent. The surface web is the open part of the internet, which includes publicly accessible websites and resources. Search engines index all the web resources on the surface web, so you can search for them online. You just need standard browsers like Chrome, Edge, and Safari to open websites on the surface web. Because of this reason, it is quite easy to encounter fraudulent or malicious websites and you need to take a cautious approach to manually avoid them. That is why you should always check the URLs you visit carefully and avoid entering any personal information on a website unless you’re sure it is trustworthy.

Search The Web
I strongly advise doing your own research to make sure you’re not breaking any local laws by visiting the dark web. Also, even in countries where accessing the dark web is legal, it’s still against the law to use or host sites that promote criminal activities. Torch is one of the oldest dark web search engines, and it’s generally considered one of the safest. It has some advertisements on its home page, but they’re for popular searches and services to help get you started.
How To Get On The Dark Web Safely & Anonymously In 2025?
While accessing the dark web using Mozilla Firefox is possible, you must first adjust its settings. Initially, the dark web was mainly used by government agencies, big businesses, hackers, and cybercriminals. However, technological advancements such as encryption and privacy-focused browsers like Tor enabled the general public to access it. Some whistleblowers and journalists use these portals to safely leak information, especially when a source requires complete privacy.
Access The Dark Web Safely

Tor, short for The Onion Router, is a privacy-focused network that allows you to browse the Internet anonymously. It works by routing your encrypted traffic through multiple volunteer-operated servers, known as onion routers. Tor is by far the most widely used dark web network and is the biggest network in terms of content and activities. The dark web is a hidden part of the web that is not indexed by traditional search engines like Google and requires specialized software to access. Before we explain how to venture into this part of the internet, we need to see what you’re setting yourself up for.
Unfortunately, it’s slower than NordVPN and ExpressVPN but overall, its performance is admirable in practice. While you can visit the obscure part of the internet without a VPN, it’s better to go with one. Here are our favorite choices that work well and support Tor Over VPN perfectly. We’ve clarified how to go on the dark web anonymously with the help of a VPN. A VPN is a confusing factor for many because there are two ways to use it with Tor. If you don’t know where to start, you can use The Hidden Wiki to find a few dark web domains.
Dark Web Tools And Services
To make things simpler, HTTP stands for Hyper Text Transfer Protocol, and this protocol governs communication on the world wide web. It’s what enables web browsers and servers to share information, including web pages and media files. Whenever you visit any website, click the circuit button next to the domain to open a menu displaying the servers through which your traffic passes. As illustrated in the screenshot below, our request was routed through servers in Luxembourg, Germany, and Austria when visiting TechRadar.com.
Use it to link your GitHub account, Twitter, Bitcoin address, and Facebook. This .onion link makes it impossible for hackers to impersonate your profile. It has a feature called CoinJoin that combines multiple coins from different users into a single transaction. This makes it extremely difficult to find out who you are transacting with. Also, you can set a strong password to protect your message and choose how long it will take to expire.
Is Tor Browser Free?
Just like Google, the dark web has some search engines present on it. Though they have their limitations, most of the time you’ll see irrelevant or spammy links for your search results. The biggest and most frustrating part about dark websites is that they live for a short span of time.
- The deep web refers to anything that search engines can’t crawl.1 These pages aren’t public — not because they’re illegal, but because they require a login or special access.
- The standard dark web browser is Tor Browser, which directs your browser traffic through the Tor network so you can reach the darknet.
- It’s like an iceberg – The visible tip above water, known as the “surface web” represents the familiar, searchable content.
- Whenever you enter any domain into the address bar, your browser uses HTTP to find and request the data from the relevant server.
- The dark web can certainly be dangerous — with no regulation, it’s a riskier place to hang out than the surface web.
Accessing The Dark Web Without Tor: Setting Up I2P And Hyphanet

It’s impossible to access the dark web with a regular browser like Chrome or Safari. But again, your ISP won’t be able to see any of the content you’re reading or what you are sending and receiving through the Tor network. It has been estimated that a large percentage of dark web traffic is related to illegal pornography that includes underage victims. There are a number of services and tools available on the dark web, many of which can be used for nefarious purposes. The release of Freenet in 2000 is considered by many as the start or founding of the dark web.
Unlike Tor, however, it cannot be used to access the public internet. It can only be used to access hidden services specific to the I2P network. I2P cannot be used to access .onion sites because it is a completely separate network from Tor.
The company has an independently audited no-logs policy and its comprehensive server network is RAM-only. It comes with DNS leak protection and works well if you’re aiming to improve online privacy. Surfshark is a low-cost provider that ticks all the boxes for use with the dark web.
Simply copy the URL of the site you want to visit, press Enter, and you’re all set. On top of that, Tor’s nodes can also malfunction because they’re owned by volunteers, which will expose your traffic and sensitive information. This is where a VPN comes in, and a reliable VPN like NordVPN (read our NordVPN review here) can do wonders for you. You might’ve heard of the domain extension called “.onion“, which sits at the end of each dark web website. Indeed, these websites use “atypical” names and domains to present themselves.
How To Access The Dark Web Or Deep Web Using Tor

The U.S. Army developed “onion routing” to protect intelligence communications online. Staying safe on the unregulated dark web requires vigilance, and its seedy reputation, fostered by controversy like that surrounding Silk Road, is well-earned. Among the many benefits of using a VPN vs a proxy or Tor is that it provides full encryption for all the data you send and receive online. So not only is your web activity hidden, but you can mask your IP address by connecting via a wide range of global VPN server locations.

However, make sure you’re careful which links you click on — some of them lead to sites that contain illegal content and services. So, I put together a list of the best dark web sites in 2025 to help you get started. I also included instructions on how to access the dark web, and outlined how to stay safe when browsing dark web links (the dark web is also home to many scams and malicious sites). Though there are other ways to access onion websites, it is recommended that you always use Tor to access dark web websites. It offers better speed and security than other alternative methods.
This setting forces all website connections to use the secure HTTPS protocol rather than HTTP, an insecure version that leaves you vulnerable to eavesdropping. To maximize security, you should avoid logging into personal accounts, such as Facebook and Gmail, via Tor. Although the Tor Browser is designed with strict privacy, logging into personal accounts can expose your real identity. Each server our request passed through had a distinct IP address.
Ensure that you’re aware of what is permissible in your jurisdiction. For advanced users, I2P offers configuration options for adjusting bandwidth limits, adding encryption layers, or even setting up your own eepsites. These settings can be found in the Router Console’s configuration panel. I2P (Invisible Internet Project) is an open-source network designed to allow anonymous and private communication. Although it’s not as widely used as Tor, I2P can provide robust anonymity and is well-suited for peer-to-peer file sharing. Be aware, however, that there are sites for absolutely everything, from the benign to the very illegal.
It has a large network of secure servers, the ability to keep connections private, and apps that are rich in security features. It’s important to use a VPN when accessing the dark web to protect your online safety and identity. The dark web is a controversial part of the internet, famous for being a hotbed for illegal and criminal activity. Read our comprehensive “what is the dark web” guide to understand how it works and the risks and benefits. If you want to learn all about privacy protection or cryptocurrency, the dark web has plenty to offer. There are a variety of private and encrypted email services, instructions for installing an anonymous operating system and advanced tips for the privacy-conscious.