Interestingly, darknet sites also offer stolen documents and passports from around the globe. For example, you could find a passport from a UK citizen there for under a million dollars. Due to its hidden nature, the dark web is also famous for the names underground internet and black web. However, don’t fret yourself about this frightening concept, than the actual meaning of the dark web. Using the Tor browser is simple, but knowing when to fire it up is more complicated. Another challenge is CAPTCHAs; because Tor behaves differently than other browsers, it’s more likely to trigger the bot-hunting system, so be prepared to face more of them than usual.
- Hidden services can operate while keeping the physical location of the server hidden, which makes tracking and shutting them down considerably more challenging.
- The dark web is a controversial part of the internet, famous for being a hotbed for illegal and criminal activity.
- Not just Tor alone, there are official sites for downloading every similar web browser APK.
- Nonetheless, if whatever you do is deemed illegal in your country, you can get into trouble.
- As noted by Andy Greenberg at Wired, while the deep web makes up approximately 90% of the internet, the dark web makes up only around 0.1% and is designed to provide anonymity for users and site owners.
Instead, it uses its own search engines – we’ll get to that later. Norton 360 Deluxe provides a comprehensive suite of protection that can help block malware and dangerous links in real time, and even detect scams using cutting-edge AI detection. Plus, it features a built-in VPN to encrypt your connection, hiding your IP address and online activity, for more anonymous and private browsing. The deep web can also be termed an “Incognito Mode” of the web which cannot be accessed by search engines. There are possible chances that you all must have heard of the Deep web, Dark web, and Darknet, and sometimes people get confused while differentiating between them. Did you know that we can only access 4% of the resources from some of the most popular search engines like Google, Bing, etc.

Anonymity Through Tor
The dark web presents various threats, including malicious software and computer viruses, posing risks to users’ systems and data security. Users also face the potential danger of government monitoring and surveillance — or scams and fraud, and other activities that can lead to financial loss and identity theft. Yes, the darknet still exists and continues to operate through networks like Tor, I2P, and Freenet. While law enforcement regularly shuts down illegal marketplaces, the underlying infrastructure remains functional. New darknet sites and markets continuously emerge to replace those that get shut down.
Even one of the best search engines, called Grams, returns results that are repetitive and often irrelevant to the query. Link lists like The Hidden Wiki are another option, but even indices also return a frustrating number of timed-out connections and 404 errors. The dark web is a subset of the deep web that is intentionally hidden, requiring a specific browser—Tor—to access, as explained below. No one really knows the size of the dark web, but most estimates put it at around 5% of the total internet. Again, not all the dark web is used for illicit purposes despite its ominous-sounding name.
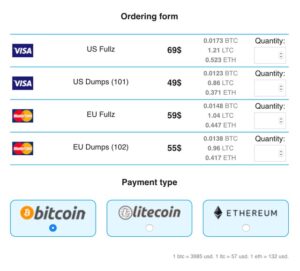
Many experts advise against using third-party mobile browsers that utilize the Tor Network. As long as users take the necessary precautions, no one knows who anyone else is in the real world. Users’ identities are safe from the prying eyes of governments and corporations. Dark web commerce sites have the same features as any e-retail operation, including ratings/reviews, shopping carts and forums, but there are important differences. When both buyers and sellers are anonymous, the credibility of any ratings system is dubious.
Myth: It’s One Huge Unified Network
We take a deep dive into what the dark web is and the dangers it poses. The technology behind this anonymous connection is known as “onion routing,” which utilizes a layered approach to obscure data and protect users’ locations on the network. Yes, you definitely need a VPN if you want to access the dark web on your phone.
Myth 4: The Dark Web Is Inherently Dangerous To Visit
You should also make sure your device is protected by strong antivirus software, and consider using a VPN to mask your activity on the dark web. The Tor Onion Browser is essential for accessing the dark web, designed for user anonymity. Unlike the regular internet, the dark web doesn’t use standard URLs or search engines. Instead, sites have complex .onion addresses, making them difficult to find without the exact URL.

Is It Illegal To Access The Darknet?

The dark web comes with its own set of tools and services, including web browsers and search engines (which I’ll get on to in a moment). Part of what makes the dark web the dark web is that you can’t access it through your normal web browser, nor can you look something up on it via a Google search. TOR is the most popular way to access the Dark Web while shielding a user’s location.
With the creation of Tor, users could now browse the internet completely anonymously and explore sites that were deemed part of the “dark web.” Anonymity on the dark web may be attractive to government critics and victims of harm who want to keep their identities private. However, criminals and malicious hackers also use the dark web to hide their illegal activities. However, it’s illegal if you venture into the dark web to commit unlawful actions such as downloading child porn, buying fake documents, drugs, credit cards, and more. Fortunately, it’s not a criminal offense if you simply search the dark web, but if you use it to carry out illegal activities, you get in trouble. Due to its anonymity, carding, fraud, and counterfeiting businesses are thriving on the dark web.
Other Ways To Access Dark Web Platforms
The Dark Web is not easily accessible and one has to go through some extra steps to locate it. Unlike other conventional browsers, it is impossible to type .onion addresses directly. However, there are browsers that are developed for the dark web, such as the Tor Browser. But the process is not as simple as that, there are safety measures and privacy concerns that should be taken into consideration. Once a user installs a dark web browser on a device, it functions like a regular browser.
Roundup – Best VPNs For The Dark Web
Ratings are easily manipulated, and even sellers with long track records have been known to suddenly disappear with their customers’ crypto-coins, only to set up shop later under a different alias. These groups develop their own sophisticated malware, sometimes combined with pre-existing tools, and distribute them through “affiliates”. Cybersecurity has to also cover everything physically on your computer too—which law enforcement or government authorities might have the right to seize if they come calling. If you want to be untraceable and undetectable, connecting to the dark web via the Tor browser is a major step towards that, but not the only step you’ll need. To get on the dark web, you need a browser built for the job, and the best in the business is Tor.
Verify onion URLs
In the same vein, online scams are much more prevalent on the dark web than on the surface web. Scammers are bolder and much more daring because they know they’re untraceable. Add to that the fact that Bitcoin is the preferred currency on the dark web. If you think eBay transactions aren’t safe, dark web transactions are far worse. Identifying specific individuals who use the dark web can be quite tricky.
How SentinelOne Protects From Dark Web Threats
You can never be sure of the motive of the person operating the node that your traffic is routed through. To better understand how the dark and the deep web work, you must first understand how the open web operates. Web crawlers run the regular internet, scouring the web to discover newly published websites or pages in a process called crawling.
We gather data from the best available sources, including vendor and retailer listings as well as other relevant and independent reviews sites. And we pore over customer reviews to find out what matters to real people who already own and use the products and services we’re assessing. The dark web is content that exists on dark nets, which require specialized software (like the Tor Browser), configurations and authorization to access. These can include the previously mentioned illegal offerings, but can also include ultra-private information designed to be shared only with certain parties.
These techniques, over time became public and thus led to the emergence of the hidden networks. As the features of dark web tools developed, the criminal mind saw the possibility of anonymous trade, leading to markets. The most common of these browsers is Tor, which launched in 2002 and serves millions of users. Another is the Invisible Internet Project (I2P), which specializes in the anonymous hosting of websites on the dark web.
If a breach is detected, BreachGuard will notify you right away and help you take the steps you need to secure your data immediately. By monitoring known dark web marketplaces, Avast BreachGuard will alert you immediately if and when your data is found. That way, you can change your passwords and lock down your accounts to help block scammers from using your data against you. You can access the dark web on mobile with a dedicated dark web browser app.