The marketplace has an intuitive interface and offers powerful search tools that make it easy for you to find products from both local and international sellers. All vendors are vetted before they are allowed to sell, so it makes sure of trust and quality. Launched in 2020, Cypher Marketplace sells fraudulent documents, stolen credit cards, fake IDs, and malware. Its emphasis on user anonymity and document forgery makes it a core tool for identity fraud. When people hear “Dark Web,” they often think of illegal activities. The Dark Web operates on encrypted networks like Tor, which obscure users’ identities.
How To Protect Your Identity While Browsing The Dark Web
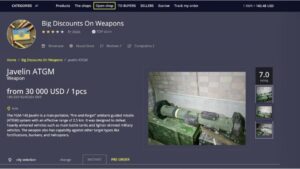
As such, they are normally under intense scrutiny from law enforcement and security professionals alike. In addition to counterfeit merchandise, MGM Grand Market offers access to stolen credit card information, compromised bank accounts, and other financial fraud-related services. These markets sell a range of illegal goods and services, including drugs, weapons, stolen data, and counterfeit items, and they typically require special software like Tor for access. There are some that focus on a specific niche, so it might be drugs or, kind of, digital products, hacking tools, malware, cracked software. BidenCash became known for regularly leaking huge amounts of stolen credit card data and personal information — often for free.
We The North Market (Best For Secure Transactions & Low Fees)
It’s important to know how these tools are used so you can perform reconnaissance and identify potential attacks or leaked information that can be used against you. Here is our list of 15 common technologies and tools used by cybercriminals to access and communicate via the dark web. Given the explosive growth of these markets, organizations must prioritize proactive threat monitoring.
Abacus Market (Best For Cryptocurrency Transactions)

All of this has made it one of the most reliable markets still active in 2025. The Dark Web presents significant cybersecurity risks for businesses, as stolen credentials, intellectual property, and sensitive data are frequently traded on illicit marketplaces. This approach enables businesses to conduct cybersecurity risk assessments and mitigate potential threats before they escalate into financial losses or compliance violations. With the rise of technology and the internet, a whole new realm of online marketplaces has emerged, including the infamous Dark Web. The Dark Web is a hidden part of the internet that is not indexed by search engines and can only be accessed through specific software or networks. It has gained notoriety for being a hub for illicit activities, such as selling drugs, weapons, stolen data, and other illegal goods and services.
Current State Of Dark Web Markets

It’s like entering a masked ball where everyone’s identity is hidden. A multi-layered cybersecurity strategy incorporating Dark Web monitoring, cybersecurity risk assessments, and employee training can significantly reduce vulnerabilities. The first category includes classic marketplaces, which serve as one-stop shops for a wide range of illegal goods. These platforms sell everything from drugs and fake IDs to weapons and hacking tools, resembling a digital black-market bazaar.
Choosing A Safe And Trusted Dark Web Marketplace
When a user and a website send data to each other over Tor, the data packets are randomly routed through a massive network of volunteer computers. Each of these nodes only knows where the packet just came from and where it’s going next, as each layer of an encryption onion is stripped from the packet contents. It’s only when the packet reaches the final destination that the last layer of encryption is removed and the intended recipient gets the original data. If you plan on venturing into the dark side of the internet, take added security measures to ensure private information like your passwords, bank details, and credit card numbers are protected.
Protector Ring
Some dark web listings claim to offer services like hacking-for-hire or even hitmen. One of the most common types of illicit goods is stolen login credentials, often collected from data breaches. These “credential dumps” allow criminals to access online accounts, steal identities, and commit fraud. Many listings involve stolen personal information, including credit card data, Social Security details, and full identity profiles. In this article, we’ll explore what dark web markets are, how they work, and why they’re so risky. We’ll also discuss examples of major marketplaces, myths about the dark web, and tips on staying safe in case your personal data ever ends up there.
- Dark web marketplaces are online marketplaces where people can buy and sell illicit goods and services under the protection of the anonymity of the dark web.
- But human trafficking, illegal pornography featuring underaged victims, money laundering, and assassinations are also examples of the darkest corners on the dark web.
- With all of that in mind, you need to tread carefully when browsing, in terms of the sites you visit and the other users you interact with.
- We highly recommend using a strong VPN like NordVPN to stay safe and private.
- Supreme Court will allow the FBI to search and seize any computer that’s using the Tor browser or VPN.
These days, it can seem increasingly difficult to protect valuable assets and data from the reaches of threat actors. This is particularly true for enterprise organizations working with sensitive data in key sectors like healthcare, energy, and finance. There are many authoritarian governments across the globe, and people living under such regimes often need to anonymously communicate. In fact, it can often be much safer for people in such circumstances to use the Dark Web over a virtual private network (VPN).
- One option is to try DuckDuckGo’s .onion version, which is great for privacy.
- Many listings involve stolen personal information, including credit card data, Social Security details, and full identity profiles.
- These marketplaces offer a wide range of counterfeit items that are designed to resemble the genuine products as closely as possible.
- Criminals prefer the dark web because it offers anonymity like never before.
- We’ll also explore how you can safeguard your organization against cyber threats by proactively monitoring illicit vendors and their activity on the dark web.
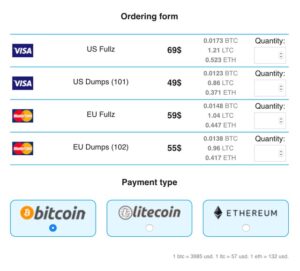
Various cryptocurrencies such as Bitcoin and Monero can be used to make purchases. If you ever decide to explore the dark web, protecting your identity is crucial. Most people start by using the Tor Browser, which hides your IP address. Some markets are invite-only or have strict registration rules to keep out scammers and law enforcement. One of the most common is the exit scam, where a marketplace suddenly disappears and takes everyone’s money with it. Many governmental organizations, several newspapers, and myriad tech organizations have a presence on the Tor network, which keeps their identities anonymous when interacting with the Dark Web.
Is The Dark Web Getting Safer Or More Dangerous?
It can also reside in web archives, non-HTML pages, and so forth. For businesses and individuals alike, understanding these threats is the first step in securing their digital assets. However, combating dark web risks requires more than just awareness—it demands proactive and comprehensive protection. The very first of these marketplaces to pair the darknet with Bitcoin was the Silk Road. Over the next two years, the Silk Road set the standard for darknet marketplaces. By the time it was shut down in October 2013 and Ross Ulbricht arrested, the site had traded an estimated $183 million worth of goods and services.
The email service is available both on the surface and on the dark web. It is the dark web’s version of Wikipedia with a massive links directory. You will find all the necessary .onion links to access any content or service on the dark web. You can also use it within the dark web, as it has .onion links. It will offer you an additional layer of encryption to access the deep parts of the internet. Check out these best onion sites to access the dark web securely and anonymously.

Pocket chainsaws can be useful for outdoor activities but may be illegal in some areas. Transactions on these platforms use an escrow system, where funds are held by the marketplace until the buyer confirms receipt of the goods. This layer of trust, though among criminals, helps ensure a safer exchange and mitigates risks of fraud.
Among the changes was Reddit’s decision to charge some developers for access to the site. The move sparked a boycott among thousands of Reddit communities angered that the change would kill off third-party apps many use to read and post on the site. The trade of fake identities and passports poses significant risks, not only to individuals whose identities are stolen but also to national security and public safety.
This criminal activity exploits and harms vulnerable individuals, perpetuating their exploitation and violating their rights. Together, we can work towards ending human trafficking and ensuring the safety, dignity, and freedom of every individual. The demand for organs, such as kidneys, livers, and hearts, far outweighs the available supply through legal transplantation channels. This demand creates an opportunity for criminal networks to capitalize on the desperation of those in need of life-saving organ transplants. Counterfeit goods are often produced using substandard materials and methods, resulting in poor quality and potential safety hazards.