This knowledge assists in troubleshooting connection issues and recognizing potential vulnerabilities. Researchers should maintain updated antivirus and anti-malware solutions on their devices, although traditional software may have limited effectiveness against some dark web threats. Sandboxing or using virtual machines can isolate risky activities from the main operating system. Due to the anonymous nature of the dark web, verifying the authenticity and accuracy of information is a significant challenge. The presence of fake news, misinformation, and deliberate deception means researchers must apply rigorous evaluation methods. The challenge lies in navigating a space rife with illicit activity while maintaining personal and professional integrity.
This process doesn’t work on the dark and deep web, where most sites are not interlinked. Plus, many .onion websites are created to be temporary or invite-only, so they may not even be active long enough to be indexed. Recon Dark Web Search Engine is a new entrant in the category of “Top Dark Web Search Engines” 2025. The platform claims to be the largest Dark Web market vendor archive service and multi-marketplace search engine.
AVG Secure VPN masks your IP address from other internet users, the websites you visit, and even government surveillance. And thanks to ultra-secure, end-to-end encryption, your online activity is obscured. Tweak Library is a dedicated repository of information about technology. Here, tech lovers can find troubleshooting articles, software reviews, guides, tips & hacks etc. to resolve everyday tech issues. Though based on meticulous research, the information we share does not constitute legal or professional advice or forecast, and should not be treated as such.
This is a great resource for users looking to refer to old prices or job listings that have changed or are outdated. It saves a select version of each page and preserves it even after upgrades have taken effect on the original site. Read about the adventures of modern-day explorers who have made it their mission to venture into the tunnel network of huge American universities. The site is different from our whole list, but still worth a mention. However, not all books on this site are legally available, so they don’t have copyrights. That means you may violate copyright laws while downloading books, so use a VPN to protect yourself from any legal repercussions if you have a dire need to use it.
How Do I Safely Access And Use Dark Web Search Engines Without Compromising My Security Or Privacy?
- Using the Tor Browser with VPNs is a foundational step, but additional precautions enhance anonymity.
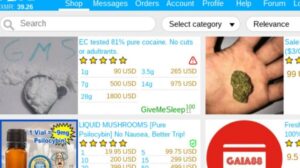
- Because of its anonymity, the dark web is filled with illegal services and is used by numerous criminal groups, including ransomware gangs.
- It aims to preserve the internet’s scientific and cultural heritage.
- SecureDrop is designed explicitly for journalists trying to preserve the privacy of their sources.
- The search engine allows you to look for old V2 onion addresses, images, and content on I2P.
Let’s start by demystifying how dark web search engines actually work. Using a dark web search engine is not illegal, and accessing dark web sites and services is generally legal. However, engaging in illicit activities on the dark web is illegal—just as it would be anywhere else—and punishable by law. LibreY is a secure dark web search engine that prioritizes privacy by operating without JavaScript, a commonly used programming language that can be used to track web activity. Candle is a web crawler and dark web search engine for Tor’s onion service websites. Candle’s index contains over 100,000 web pages, including dark web marketplaces and forums.
How To Construct Effective Search Queries And Safely Navigate The Dark Web
It’s generally recommended for enhanced privacy, particularly when exploring potentially sensitive topics or using dark web search engines. Because of its anonymity, the dark web is filled with illegal services and is used by numerous criminal groups, including ransomware gangs. It is also used by whistle-blowers, journalists, and other individuals who are not involved in illegal activity but need to protect their communications and identities.
Additional Tools

You can archive any site you want, or retrieve historical records wherever available. The Candle search engine is effective but minimalistic—it gives you only the top ten most relevant results for your search queries. And the search box can’t read certain characters like parentheses or quotation marks, which can be limiting. Avoid using your real name or repeating patterns that can be traced back to you, such as favorite usernames, writing style, or posting schedule. Even small details, like the time of day you’re active, can be used to connect the dots between your real and anonymous identity.
Separate Your Real Life From Your Online Persona
Its clean interface and lack of ads make it much easier to use than other dark web search engines. The ‘dark web’ is a section of the internet not indexed by popular search engines like Google, Bing, and Yahoo. Its anonymity and access through special software like Tor (The Onion Router) often link it to cybersecurity breaches and illicit activities. While many private search engines don’t log your IP address themselves, your Internet Service Provider (ISP) can still see which websites (including the search engine site) you visit. A VPN (Virtual Private Network) encrypts your entire internet connection and masks your IP address from your ISP and the websites you visit. Using a VPN adds an extra layer of privacy and security, especially if you are concerned about surveillance or wish to bypass geographic restrictions.
What Kind Of Information Can I Find On Dark Web Search Engines?

It provides all the same resources—contacts, services, and information—that are available on the official CIA website. Those who wish to provide information to the spy agency in an anonymous manner, yet run the danger of being followed, are the target audience for the .onion website. However, while using the black web for browsing won’t get you into trouble with the law, doing illegal things would. For instance, it is against the law to buy narcotics or weapons on the dark web, and you risk legal repercussions. First get the setup ready by downloading the tor browser from the official website. Install it, check the settings and head out to torgol or any other tor search engine of your choice.

The Best Dark Web Search Engines For Anonymous Browsing
The BBC news website has a special .onion site, which you need to access via the dark web. Its goal is to offer anonymous access to the content without being censored, no matter where you live. The good news is that the BBC Onion site is an international edition. As a result, it not only focuses on the UK but also provides worldwide news.
We advise using a reliable VPN, such as iProVPN, which protects your IP address with military-grade encryption and monitors the dark web to warn you in the event of identity theft. One web browser that provides improved privacy and anonymity is the Tor Browser. It encrypts internet traffic and routes it across several relays using the Tor network, making it challenging to track down your exact location or identity. The deep web includes any unindexed content like academic databases or private company portals. The dark web is a small part of the deep web that requires Tor to access.

Search engines and corporate websites might be OK, but even a popular Tor website like Hidden Wiki can show illegal deep web links that jeopardize your online safety. So, I’d just sign off this list consisting of the best dark web search engines saying they’re all worth it. Just be sure you know what you’re searching for, make sure you use a VPN and stay away from straight up illegal content. One of the earliest and most well-known dark web search engines is called Torch.
Use it to link your GitHub account, Twitter, Bitcoin address, and Facebook. This .onion link makes it impossible for hackers to impersonate your profile. ZeroBin is a wonderful way to share the content you get from dark web resources.
Essential Safety Practices:
You’ll need a dark web search engine, and we’ve compiled the best ones for you to try. Complementary tools such as encrypted communication apps, secure note-taking programs, and offline data analysis software enhance the research workflow. Utilizing password managers ensures the safe storage of credentials used for dark web accounts, reducing the chance of breaches. Conducting research on the dark web requires navigating a multifaceted landscape where ethical and legal issues are intertwined. The inherent anonymity of the dark web offers protection but also creates opportunities for illicit and harmful activities.
Unlike many imitators, this is the official Hidden Wiki that maintains a curated directory of legitimate .onion services. During my testing, I found its categorized index particularly helpful for discovering trustworthy sites across various topics. DuckDuckGo is primarily known for its strong privacy stance (not tracking searches). Users may encounter illegal or highly disturbing content, scam websites, phishing attempts, and malware. LibreY is noted for operating without JavaScript, enhancing security. This discussion highlights how mainstream search engines might filter or prioritize information based on commercial interests, political leanings, or opaque algorithmic decisions.
You can access DuckDuckGo on the surface web, but a Tor version is also available. You’ll get unbiased, organic search results without getting any of your browsing behavior logged. Using DuckDuckGo over Tor will also let you see onion sites and normal pages in your search results. While many dark websites appear sketchy, The New York Times is an exception.
Yes, DuckDuckGo has a .onion version that works through the Tor browser for anonymous searching. By following these precautions, you can explore the dark web with a greater degree of safety and security. Lastly, users can stream public videos and access government resources through a standard web browser. Dark web surveillance involves monitoring information on the darknet, such as to identify compromised credentials being sold, or to track forums to anticipate (and prevent) cyberattacks. The dark web, on the other hand, is a small part of the deep web that requires special tools like the Tor browser to access.