Deep web refers to anything on the internet that is not indexed by and, therefore, accessible via a search engine like Google. Deep web content includes anything behind a paywall or requires sign-in credentials. It also includes any content that its owners have blocked web crawlers from indexing.
International policing groups are working to disrupt several major platforms through joint efforts. The Australian Federal Police (AFP) participated in a Europol-led investigation that in 2024 shut down LockBit’s primary platform along with 34 servers across the US, the UK, Europe, and Australia. Continuous monitoring of stealer logs, credential leaks, and dark web chatter should be a core function of threat intelligence, not an occasional sweep after an incident. “It’s a live reconnaissance zone,” says Ensar Seker, CISO at SOCRadar. There are also some excellent ways to protect your privacy from most bad actors. Take some time to decide if this is the right option for you before downloading the Tor browser.
How To Access The Dark Web
The freedom to communicate, publish, and read anonymously is a prerequisite for freedom of expression online, and thus a prerequisite for democracy today. Using and supporting Tor helps support freedom of expression around the world. Technically sophisticated users are encouraged to donate bandwidth to the Tor network by running a relay. Tor Browser routes all your web traffic through the Tor network, anonymizing it. As the images below illustrate, Tor consists of a three-layer proxy, like layers of an onion (hence Tor’s onion logo).

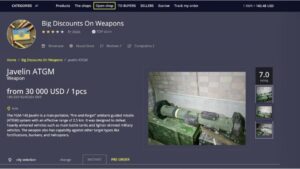
Dark Web Tools And Services
- Many people use it for privacy-focused communication, whistleblowing, or accessing restricted information in censorship-heavy regions.
- The majority of Dark Web sites use the anonymity software Tor, though a smaller number also use a similar tool called I2P.
- Instead, download Tor, the most secure and user-friendly option for accessing .onion sites.
- Alfred Liggins, Urban One’s CEO, acknowledges that there’s work to be done on the technical side.
- These services look at your IP address and guesstimate your country and language, but when using Tor, you will often appear to be in a physical location halfway around the world.
I think the first step to understanding others is to admit that you don’t, and I made a densely Black coded layered video knowing that it was very culturally opaque. But I wanted to use that dissonance and understanding between the viewer and the work as artistic material itself. I think the fullest form of understanding that can exist between two people is knowing that no such thing actually exists. There are things that you simply cannot understand and that’s okay. I think the term “Black body,” for example, is a violent racist term because there’s no equivalent “white body” term. You don’t use the word bodies to describe the living, you use it to refer to the dead.
Related Content
The idea that technology, a technological system, is in and of itself useful, important, and has value. I think a lot of it really, for me, comes back to this sense of value, right? I’m wondering why you think that is, because from the jump, the opportunities look the same, right? Here’s some money, build some community on this dominant networked platform. He saw the opportunity, and that didn’t leverage itself into the next thing.
“Bitcoin has been a major factor in the growth of the dark web, and the dark web has been a big factor in the growth of bitcoin,” says Tiquet. The affiliates distribute the ransomware packages through the dark web. These attacks often include stealing victims’ data and threatening to release it on the dark web if the ransom isn’t paid. If it weren’t for the work of our next Black internet pioneer, life during the pandemic would’ve been a nightmare. Marian R. Croak, Vice President of Engineering at Google, opened up the possibility of simultaneous live audio and video sharing on the Internet with the Voice over Internet Protocol (VoIP). So in your next Zoom meeting or impromptu FaceTime session, don’t forget to thank the MVP of VoIP.
Part 2 How To Access Black Web/Black Internet

“Identity fraud is enhanced through synthetic persona generation and deepfakes, aiding criminals in bypassing know your customer (KYC) and biometric checks,” says Kroll’s Currie. “Threat actors are wanting to drive focus on their own brand names to gain more notoriety for themselves, such as the regular launching of new ransomware group brand names and leak sites,” says Carroll. Popular malicious tools or services also include OTP bypass bots that automate voice or SMS to steal 2FA codes, crypto drainer kits that empty victims’ wallets, and deepfake services, according to Ian Ahl, SVP at P0 Labs. “In parallel, some actors are experimenting with blockchain-based hosting, decentralized DNS, and peer-to-peer marketplaces, which offer greater resilience against takedowns and surveillance,” Salom says.
More In Technology
The internet opened the door to a realm of possibilities that permanently changed the business landscape and our personal lives. When you click through from our site to a retailer and buy a product or service, we may earn affiliate commissions. This helps support our work, but does not affect what we cover or how, and it does not affect the price you pay. Neither ZDNET nor the author are compensated for these independent reviews.
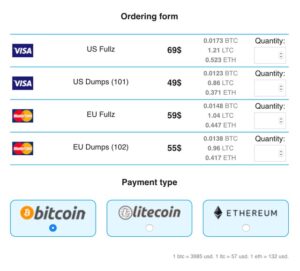
Get Early Warnings Of Targeted Attacks
You don’t need to prove your identity before using the Bitcoin network the way you do with credit cards. But that doesn’t necessarily mean the authorities won’t be able to trace buyers and sellers. Indeed, information about every Bitcoin transaction is publicly available; by examining the pattern of transactions, the authorities may be able to tie a Bitcoin transaction to a real-world identity. If you tried to set up an illicit drug marketplace that used conventional credit cards, it wouldn’t last very long. For one thing, Visa and Mastercard rules would likely bar you from getting a merchant account.
Should You Use A VPN And Tor?
Slide up to the “safest” level, and as well as those settings, JavaScript is disabled on all sites. While strong encryption, VPNs, proxy servers, and hidden web addresses can all contribute to a more anonymized experience, there is no singular system available that is completely private and secure. If you want to access the Tor network on your iPhone or iPad, you can use the Onion Browser app. The mobile app uses DuckDuckGo as its default search engine and is supported by the Orbit framework to provide secure access to the Tor network. Our goal is to deliver the most accurate information and the most knowledgeable advice possible in order to help you make smarter buying decisions on tech gear and a wide array of products and services. Our editors thoroughly review and fact-check every article to ensure that our content meets the highest standards.
Unpacking these layers of encryption is sort of like peeling an onion. In attempting to access the Dark Web, there’s an invisible line that a person acknowledges they’re crossing – or maybe they don’t. Either way, no one is accessing the Dark Web with a sense of optimism. The Dark Web was leveraged by the United States Department of Defense as a means of communicating anonymously. Its talent for keeping activity anonymous remains, but now protects malicious actors instead of innocent citizens of a given country.
The service had only about 1,000 users; Wasow made his actual living by building websites for magazines. So he was excited when he met Sun, then the president and CEO of the social-networking firm Community Connect, which in 1997 launched an online forum for Asian Americans called AsianAvenue. Tor (“The Onion Routing” project) network browser provides users access to visit websites with the “. This browser is a service originally developed in the latter part of the 1990s by the United States Naval Research Laboratory. Tor is both a type of connection – with the extended relays – and a browser.
We have degree and certificate programs in Information Technology, Cyber Defense, and Cybersecurity Management that can teach you how to protect internet users online and prepare you for a number of rewarding career paths. Learn more about our various degree and certification programs today by requesting more information. Given its anonymous nature, the dark web is also used for illicit and even illegal purposes.