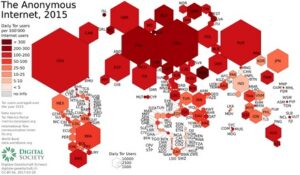
A reliable, fast, and user-friendly VPN service offering lots of customizable options for privacy geeks. It is imperative to stay alert and trust your gut when on the web. Today, many organizations exist that are created only to handle these reports anonymously and effectively. They know how to process the information and get it to the correct law enforcement agencies internationally.

The Best Dark Web Search Engines In 2024
It is the dark web’s version of Wikipedia with a massive links directory. You will find all the necessary .onion links to access any content or service on the dark web. You can choose the best darknet (.onion) website that suits you and start surfing. For safer browsing, it is highly recommended to also use a VPN and antivirus software. If you know the right websites, you can easily access a tremendous amount of information, including research articles, news stories, and more.
How To Access onion Sites Safely
SecureDrop is a site that protects the privacy of journalists and whistleblowers. SecureDrop is a dark web link that allows whistleblowers on the dark web to communicate and share information with journalists safely and without being tracked. Sci-Hub is a massive database that eliminates the barriers to getting scientific knowledge. It contains millions of scientific research documents from around the world. The site seeks to liberate information by making it free to individuals and institutions. Moreover, due to its popularity, many copycats of the Hidden Wiki exist.
Keep Your Data Off The Dark Web
Examples of the deep web include any websites that are behind a paywall or require login credentials. Most internet users access the deep web several times a day to perform common tasks, such as checking email, accessing a bank account, or reviewing health or school records. The deep web constitutes over 90% of online content and is inaccessible via search engines. You can’t just boot up Google; you’ll have to use specific darknet search engines and your dark web URLs will look noticeably different to their conventional counterparts. Notorious ransomware groups are the ones that use onion.ly links most often. This is because when a victim’s computer is infected by ransomware, attackers demand ransom through dark websites.
Tips To Stay Safe When Using The Dark Web
Use cryptocurrency to buy anything, and use a disposable email address for any type of communication on the dark web. Opennet connections are easier to use, but darknet connections provide more security against attackers on the network. But remember, it’s essential to take all the necessary and important security steps before entering such sites on the dark web.
Caution: Safety Comes First When Visiting Dark Web Links
While the Tor browser gets updated automatically, you should manually check whether updates are available from time to time. However, since it is so popular, you will find several versions of the program on the internet. These are unreliable copies that can cause you to download malicious content on your computer.
Using The Tor Browser
As a result, you can be exposed to different malware types, including botnets, ransomware, keyloggers, and phishing. With rising online privacy concerns in the current digital age, the Tor network’s anonymity is becoming essential. It is a good way to prevent third parties from tracking online activities. People in countries with heavy internet censorship must get a VPN or Tor browser to access the surface web. These sites are a hybrid tutorial-underground where wannabe hackers ask questions and professionals sell their services or stolen data.
You can either sell or buy goods on the dark web, but both present difficulties. The dark web is also a place for scammers to attract vulnerable and unwitting victims. The platform is also used by governmental cyber departments to identify and track potential criminals or offenders.
The Onion Router (Tor) also made the technology available in 2002. It is a relatively new provider but offers better features than most established VPNs. On top of that, the provider offers perfect forward secrecy (PFS).
BBC Tor Mirror
In rare cases, attackers can exploit an unsecure node to monitor Tor users or gain unauthorized access to accounts. Tor is slower than standard browsers because it routes your traffic through multiple servers. This routing, through at least three nodes distributed worldwide, introduces latency, especially when there’s congestion on specific nodes. However, the most secure way to use Tor is via .onion sites, which are built exclusively for the Tor network. The entry node knows your IP address but not the intended destination.
- By using Tor and a reputable VPN, along with being careful and having the right tools, you can browse the dark web legally and safely.
- To understand the Dark Web, it’s important to first grasp the broader concept of the Deep Web.
- This enables individuals to form groups and only share content in a highly anonymous network of darknet users who they know.
- Developed in the mid-1990s to keep U.S. intelligence communications from prying eyes, the Tor Project is the preferred method to access Dark Web content.
- Initially, the dark web was mainly used by government agencies, big businesses, hackers, and cybercriminals.
Navigating Ransomware Attacks While Proactively Managing Cyber Risks
Journalists can use the dark web to publish articles while protecting their source identity using particular browsers. Unlike Tor, I2P is designed for peer-to-peer services like file sharing, email, forums, and even decentralized websites — all within its own closed network. Its distributed nature makes it more resistant to central points of failure. Even with Tor and a VPN, you’re not fully protected unless you also lock down your behavior. Most dark web leaks happen when users skip basic safety steps or reveal too much without realizing it. Use the tips below to patch common blind spots and avoid easy-to-make mistakes.

When browsing dark web sites, it is critical for users to engage in safe online behaviors. This includes turning off JavaScript within the Tor browser to obstruct tracking and reduce security risks. As there are no regulatory mechanisms governing these sites, one must ensure the legitimacy of any dark web site prior to accessing it.

The tradeoff is that you don’t get personalized search results, as DuckDuckGo doesn’t collect user data. But this tradeoff is worthwhile when seeking to browse with the utmost privacy. To surf the web privately, you need to connect to the Tor network from your browser.
You can also take a look at the blogs & essays section if you want to find some nifty coding resources. Well, now it’s time to fire up Tails and do a little bit of tinkering. Note that the process can take anywhere from 5 to 30 minutes depending on your machine.
Accessing the dark web can be a fascinating and educational experience, but it’s important to exercise caution and use a reputable VPN. Remember that not all .onion sites are legitimate or safe, so it’s crucial to do your research and use common sense when browsing the dark web. With the right precautions, you can explore this mysterious corner of the internet safely and securely. Users of the dark web should also realize that although their activity is technically anonymous, associating with people who are conducting illegal activities can have legal implications.