A VPN routes your online traffic through secure and encrypted servers to ensure you stay anonymous, unseen, and untraceable. It does this through high-level and top-quality encryption, providing you with an extra layer of protection at all times. When browsing the dark web on mobile, finding what you’re looking for can be tricky. These search engines can help you discover .onion sites related to your interests. However, note that dark web search engines don’t index as many sites as regular search engines, so results can sometimes be limited or outdated.
Phone 14 Launcher – IOS 16
If you seek utmost privacy when surfing the web, the Tor browser is your best bet. This free, open-source browser routes your traffic through multiple volunteer-run servers, scrambling your data and making it very challenging for third parties to track you. Justice Ekaeze is a freelance tech writer with experience working for specialized content agencies. Justice has acquired extensive content writing experience over the years. He’s handled several projects in diverse niches but loves the cybersecurity and VPN sectors the most.
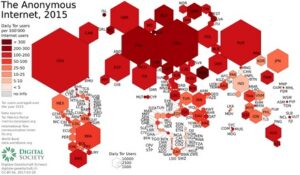
Best Dark Web Search Engines For Android & IOS
Not to mention the fact that you’ll get exposed to some stuff that will definitely make you take several cold showers. Fortunately, in Hidden Wiki, every website is followed by a brief description so that the user knows what to expect. You can also take a look at the blogs & essays section if you want to find some nifty coding resources. Chill, because nobody will ever find a record of you ever fiddling around the darknet. Note that Tails’ installation package is the .img format, which means that you’ll need software capable of burning images on your thumb drive.
- It forces all internet connections to go through the Tor network.
- Though it still requires being routed through Tor (it is not a deep web browser by itself), it provides a clean, quick, and privacy-respecting base to use for your anonymous browsing sessions.
- It is a mobile application that uses your Android or iOS device’s VPN mode to route all traffic through the Tor network.
- As mentioned earlier, many websites consider Tor suspicious and block users entirely.
- Orbot is free, open source, and can even replace your VPN, if you don’t mind slower browsing speeds.
For a limited time, new users who purchase any plan can claim 25% off their first order. The user will have the discount automatically applied after they click on it and check out. While you can’t install the Tor browser from the official website, Chromebook users can configure it via a few simple Linux commands. In many countries, the installation and use of Tor are perfectly legal.
Invisible Internet Project
Whether you are exploring academic content, legal data, or unique marketplaces within the dark web, the app’s structure ensures user safety and discretion. Remember to turn on your VPN and antivirus before attempting to visit the dark web. The deep web is full of risks, including malware that wants access to your data, as well as harmful advertisements and trackers that track your online activity. The technology behind this anonymous connection is known as “onion routing,” which utilizes a layered approach to obscure data and protect users’ locations on the network. This means that the identities and locations of darknet users are hidden from public view and remain anonymous, even when interacting with other users or engaging in any online activity.
DeNet Shares Vision For Scaling Decentralized Storage, AI Integration, And The Future Of Data Sovereignty

Although the Tor Browser is designed with strict privacy, logging into personal accounts can expose your real identity. For example, in Safer mode, JavaScript is turned off on non-HTTPS (insecure) sites, but in Safest mode, JavaScript is turned off entirely for all sites. Images load normally in Safer mode, but some complex images may not load in Safest mode. The Safer option disables all potentially dangerous website features, while the Safest option enables only the features necessary for basic website functions. Each server our request passed through had a distinct IP address.
How To Access The Dark Web Using The Tor Browser?
Fun fact is that Tor Browser (Tor network is a different thing than the browser) is built from Firefox ESR (Extended Support Release), a modified version of Firefox. So, it’s worth using Firefox if you’re up for the tweaks needed. Although it requires more work, it provides tech-savvy users with a more familiar interface with better security for accessing Tor through a proxy. To access the dark web, you must have specialized software, such as the Tor Browser. It creates a space for staying anonymous, which itself is kind of a double-edged sword. Orbot is free, open source, and can even replace your VPN, if you don’t mind slower browsing speeds.
Tails – An Operating System That Forgets Everything You Did
To provide anonymity, Tor is generally quite effective, but not completely foolproof. If the person tracking you is very advanced and has unlimited resources, they could conceivably de-anonymize you when you make certain mistakes, like downloading files or enabling scripts. Using a dark web-specific browser such as Tor or I2P itself is legal in virtually all countries. But using these tools for illegal purposes constitutes a criminal act either way. Don’t be fooled into going to a malicious clone site that is designed to extract your information.
Because of this, we recommend using Hidden Wiki before you use the dark web. Hidden Wiki is a directory of the various dark web links, with detailed explanations of where each link takes you. When you see a suspicious link, especially one containing seemingly random characters and numbers that cannot be resolved using public DNS, steer clear. These links containing said random characters and numbers are hard to verify as legitimate or safe. While this should go without saying, many links pose as legitimate, and you may unknowingly click and invite harm to yourself. And since the dark web lacks any real regulation or indexing like the regular web, there is no telling who or what might be waiting in the shadows.

Top Downloads Utilities & Tools For Android
The user who signs up will get a free basic plan, and also have a 25% discount when upgrading. All you need to do is visit the Tor browser webpage and click the Windows icon, leading to the installation process. The Windows process is simple and requires you to allow or toggle certain settings. You can start your journey to a safer online experience for $4.99/month for a yearly plan, which allows you to connect 10 devices simultaneously and with a 30-day money guarantee. You are spoilt for choice with an extensive server network of over 7,600 in more than 118 countries.
While they can provide unparalleled anonymity and access to information, users must navigate with caution and awareness of the inherent risks involved. There are multiple search engines on the dark web that can help you find what you’re looking for. DuckDuckGo’s no-track dark web search service can be accessed in the Tor browser and is an excellent resource for information about the dark web. Other dark web search engines include Not Evil, Torch, Haystack, and Ahmia. Unlike the surface and deep web, you can’t access the dark web via a standard or specialized search engine. To access the dark web, you’ll need a specific set of tools – more about that later in the step-by-step section.
The release of Freenet in 2000 is considered by many as the start or founding of the dark web. University of Edinburgh student Ian Clarke created Freenet as a thesis project. Freenet was originally intended to provide a way to anonymously interact online, providing ways to communicate, exchange information and files, and to otherwise communicate incognito. But human trafficking, illegal pornography featuring underaged victims, money laundering, and assassinations are also examples of the darkest corners on the dark web. Silk Road became one of the most famous online black markets on the dark web for illegally selling drugs.
It also comes with several secure pre-installed software programs, including the Tor Browser. It can access the regular internet through “outproxies,” but that’s not its strongest suit. I2P’s most attractive angle is to access its own internal eepsites, which are its version of .onion sites.
By hiding IP addresses and sending traffic through encrypted tunnels, darknet browsers like Tor offer a high level of anonymity. The desire of intelligence services to de-anonymize Tor users highlights the necessity of taking strict security measures. The phrase “dark web” refers to a region of websites and content found on overlay networks known as darknets, to which access requires particular software, setups, or authorization.