My dedication to continuous learning fuels my passion for delving into the complexities of the cyber world. And if you liked this article, follow us on LinkedIn, Twitter, Facebook, and YouTube for more cybersecurity news and topics. When you’re done surfing or shopping on the dark web, don’t forget to shut down Tails. The major advantage of using a live OS such as Tails is that, on shut down, the OS wipes itself from the thumb drive you’ve installed it.
How To Get On The Dark Web: A Step-by-Step Guide
It’s somewhere Google and Bing don’t index, and you need special tools to get to it. Experienced blogger with a strong focus on technology, currently advancing towards a career in IT Security Analysis. I possess a keen interest in exploring and understanding the intricacies of malware, Advanced Persistent Threats (APTs), and various cybersecurity challenges.
Site operators can also submit their own .onion sites for indexing. The dark web is part of the internet that is not indexed by standard search engines like Google, Yahoo, and Bing. It means you cannot access websites on the dark web with regular browsers like Firefox or Chrome.
Report It To The Authorities (if It’s Safe To Do So)
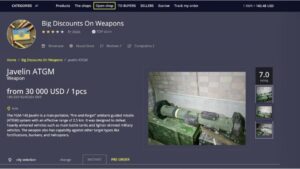
White House Market also led to other markets mandating PGP encryption and going walletless, says Eileen Ormsby, a lawyer and author of several dark web true-crime books. Those precautions disincentivize platforms and vendors from using so-called exit scams—where an established business stops shipping orders while receiving payment for new orders. Only, these industrywide best practices will make illegal online trades even harder to track for law enforcement. This is according to a review of black-market websites and interviews with dark-web users and experts who track the industry by Columbia University’s Brown Institute for Media Innovation and MuckRock. That final listing matches the site’s theme, which features Walter White from Breaking Bad on the banner. But unlike Walter White’s fictional operation, this one had a global presence, with vendors and buyers stationed all around the world, although most transactions were conducted in English.
Dark Web Sites Name List: Where To Find Secure Marketplaces
Each time you visit a website, you can be traced back to your exact location thanks to that IP address. It’s relatively easy for anyone to access this encrypted network. Swensen said the most common dark web networks are Tor, I2P, and Freenet, but “Tor is, by far and away, the most popular.” What’s submerged is the deep web — an anonymous online space only accessible with specific software. Then there’s the dark web, which is the part of the deep web that hides your identity and location.
Buy And Sell Items With Community Members For Steam Wallet Funds
When it comes to accessing the dark web (and safely), selecting a good dark web browser is critical. Tor Browser is the #1 in our list above for all the good reasons. We recommend that you use only the Tor browser to access the deep, dark web, if you must. If you fancy exploration, we’ve listed nine other options as well. In your browser settings (like the NoScript extension in Tor), you will want to disable JavaScript and other active scripts. By disabling, you reduce such attacks’ potential (especially on untrusted websites).
Is It Illegal To Visit And Use Dark Websites?
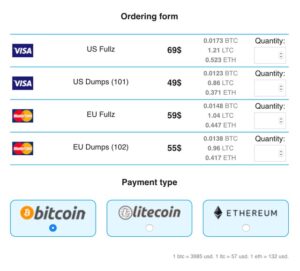
For obvious reasons—I don’t want to get you or me into trouble, after all—I’m not going to get too specific when it comes to what you can find for sale on the dark web. A lot of transactions are handled via cryptocurrencies such as Bitcoin, which is relatively (but not completely) private and anonymous. Another private cryptocurrency you’ll find being used is Monero, which prides itself on being untraceable. DuckDuckGo is the default search engine inside the Tor browser, and once you turn on the Onionize toggle switch in the search box, you’re able to use it to find dark web links. These typically come with “.onion” after them, rather than something like “.com” as on the standard web.
- When you’re on the dark web, you can unknowingly be taken far beyond just places of selling illegal substances or stolen data.
- Learn how to automate financial risk reports using AI and news data with this guide for product managers, featuring tools from Webz.io and OpenAI.
- Notably, the number of multisellers suffers the largest drop of \(-99\%\) by the end of the first quarter of 2018.
- The Tor Metrics is a good place to get more information about the Tor project.
- If you’re looking for a vast selection to explore, but not just for drugs, Point, originally titled Tochka Market, is easily the best place to go.
FOCUS FRIDAY: TPRM Insights On GoAnywhere MFT, SolarWinds Web Help Desk, Cisco SNMP, And DNN Software Vulnerabilities
Your ISP, and possibly the authorities, may decide to start monitoring your activity more closely to look for threats or illegal activity. That’s why we always recommend using a VPN over Tor—even if you feel you have nothing to hide. This just involves turning on your VPN before you open Tor and connect to dark web sites.

Stolen Data And Identity Theft
Therefore, the U2U network connects different market star-graphs. Previous studies have shown that, although the number of users and transactions is larger in markets, the trading volume in the U2U network is larger than that of markets13. We use data of DWM transactions on the Bitcoin blockchain pre-processed by Chainalysis Inc. Although other coins are used, such as Monero recently, Bitcoin is still the mostly used in the ecosystem, being supported by more than 93% of markets7,9. The pre-processing relies on established state-of-the-art heuristics to cluster addresses into entities, such as cospending, intelligence-base, and behavioral clustering39,40,41,42. The resulting data set includes for each transaction the source and destination entities, the time, and the value of the transaction.
What Was The Silk Road?
For several years, Yahoo was at the apex as the internet’s best web service provider, offering… A piece of tape over your webcam essentially prevents any possible remote activation by malware. Assume that everyone and every site is trying to take advantage of you. Avoid giving up real information, don’t log into your personal accounts, and don’t engage in conversations that could identify you.
In 2008, the first Tor Browser was released, making it easier for any internet users to access the dark web. In 2002 the dark web began to grow significantly when researchers backed by the U.S. The Tor Network provided a way to open safe communication channels for political dissidents, while also offering a channel for American intelligence operatives to communicate from around the globe.
Network Structure Of Transactions
As we stated earlier, the Hidden Wiki is an unreliable platform. ProtonMail is a Swiss-based email service that is very easy to use. You are not required to provide your personal information to create an account. The email service is available both on the surface and on the dark web.