The dashboard should open properly, indicating you’re ready to connect to any VPN server. This is just the first but also very important step to go to the dark web anonymously. We can say the same about private networks belonging to companies and other entities. Some hospitals even have classified medical records you can’t access just like that. Your traffic is relayed and encrypted three times as it passes over the Tor network. The network is comprised of thousands of volunteer-run servers known as Tor relays.
Safety Tips
Change your passwords and watch out for suspicious activity on your credit reports. Dark web domains tend to be inconsistent — new ones pop up and others disappear, which makes sense if they offer questionable or illegal goods and services. Identifying specific individuals who use the dark web can be quite tricky. However, we advise connecting to one of our recommended VPN services to stay anonymous. However, this does not provide any extra security for your device or information. There are a few reasons why the dark web isn’t stopped or shut down.
Install The Tor Browser
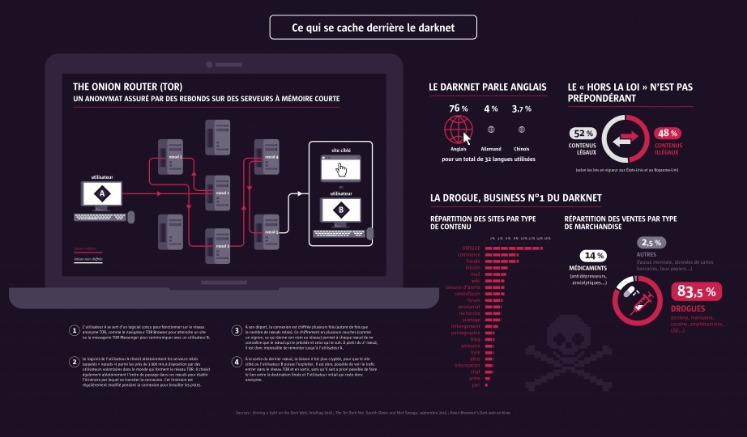
- From stolen credit cards and hacked PayPal accounts to hard and soft drugs, pirated copies of all kinds, and weapons — there is nothing that is not offered on the darknet.
- Privacy and anonymity are the core values of the dark web, and it hosts both harmless activities and illegal content.
- You should review access to your camera, location, and microphone regularly to ensure no website has unnecessary permissions.
- While you don’t need to log in to access any of the dark web links listed here, you can’t find them with a search engine like Google.
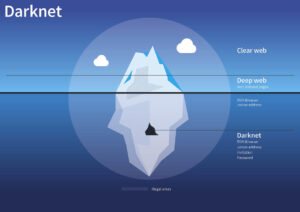
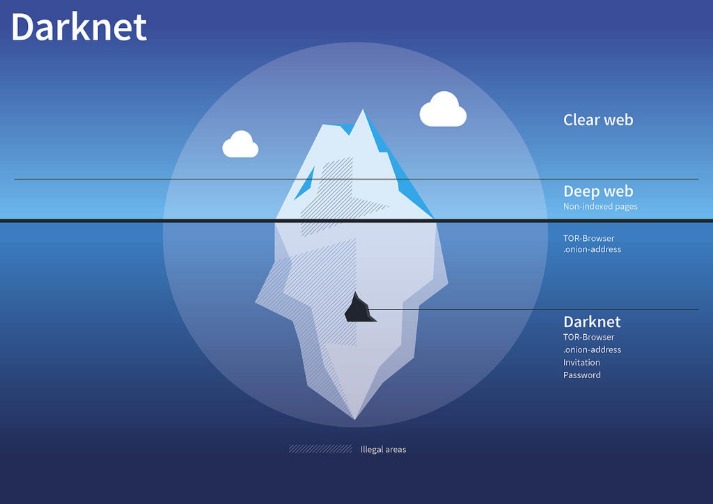
- So, when measuring the total network of live dark web sites alongside the surface web, only about 0.005% of the internet is the dark web.
- The good news is that the platform will not see what you copy/paste.
These websites will also use .onion top-level domain names, and many of them will be very long, random combinations of letters and numbers. You won’t be able to access .onion addresses using a standard search engine as they aren’t indexed by crawlers. There are many legitimate uses for dark web services and communication. To access those specific darknet networks, you will need to use the specific browsers developed for them. However, bear in mind that they are often less user-friendly than Tor (which makes accessing the dark web easy). The deep web refers to any part of the internet that is not openly indexed and made available via a web search.
They can be easily traced and even prosecuted if they share the information on the surface web. SecureDrop is a site that protects the privacy of journalists and whistleblowers. The official website of Archetyp Darknet Market, this website was created by the Archetyp Team to distribute trust onion links and URLs and publish articles about Archetyp Market. Step into the intriguing world of Archetyp Market, where anonymity meets opportunity. Join a vibrant community of users who share their experiences and tips. A VPN and Tor should be used together and it is advisable to connect via a VPN to Tor, rather than vice versa, for the best protection possible.
Is It Safe To Use?
This includes any private information held on the cloud that is not listed on the Web. This includes things like the data stored on private cloud servers, backup services, email accounts, etc. Freenet is one of the oldest anonymity networks, focused on providing censorship-resistant communication. Instead of simply routing traffic, Freenet stores encrypted chunks of data across nodes. Next, select a dark web search engine like DuckDuckGo that can help you find dark web websites that cannot be indexed by traditional surface web search engines, such as Google or Bing. Understanding how to access the dark web is valuable for IT leaders, cybersecurity experts, and professionals who need to monitor hidden threats or preserve online privacy.
How To Minimize Risks:
In this guide, we will look at some of those reasons and explain how to access the dark web if you need to. Finally, you need to enter website addresses to access content on the dark web since you can’t browse by entering a search query as you can on the clear web. In this guide, we’ll cover the dark web access guide, explain how to use Tor browser safely, and answer key questions like is it safe to browse the dark web. We’ll focus on secure, ethical practices tailored to cybersecurity professionals and IT leaders. The dark web can certainly be dangerous — with no regulation, it’s a riskier place to hang out than the surface web.
Download Tor Browser
Other porn-related content found on the dark web includes revenge porn and sexualized torture, and the killing of animals. There are reports of illegal services on the dark web, ranging from paid assassinations to the trafficking of sex and weapons. However, some of these alleged services, such as professional ‘hitmen,’ may be scams designed to defraud willing customers.
This is why many people prefer an identity theft protection service and a financial and credit fraud protection solution. It is designed to provide online anonymity and privacy to its users. Journalists, activists, and individuals concerned about online privacy and security often use it. However, it’s illegal if you venture into the dark web to commit unlawful actions such as downloading child porn, buying fake documents, drugs, credit cards, and more. This can lead to incrimination for other activities later in life.
#1 Install A VPN
In some countries, exploring new political ideologies can be considered an imprisonable offense, and those who visit restricted websites could be placed on a watchlist or targeted for jail sentences. China, for example, uses the “Great Firewall” to restrict access to popular sites and prevent citizens from evading government restrictions. PIA is popular in the USA because it offers servers in all 51 states.
- You’ll often see a sign in stores that says “look, don’t touch,” and it’s not a bad adage to bear in mind as you navigate around the dark web.
- PrivateVPN allows torrenting and has dedicated servers in its home country for just that purpose.
- Carding refers to the theft and illegal use of credit card information, and the dark web offers a platform for criminals to sell and buy such information.
- Learn how to safely access the dark web with this comprehensive guide for beginners.
- In any case, it can be used for any dark web activity thanks to various privacy features.
- It hosts encrypted websites, often used for privacy, anonymity, or illicit activities.
Even with Tor and onion routing in place though, you’re not suddenly completely invisible and free to do whatever you want, without repercussions. Certain details of your traffic can be intercepted at the entry and exit points of the node, by the people running those nodes, if they know what they’re doing and what they’re looking for. You’re also open to threats like end-to-end correlation attacks, so while Tor is a lot more secure and private, it’s by no means completely safe. You could try to visit a major site like Facebook’s onion site to check if your browser is working at all. This would verify if it’s a browser issue or just an issue with the site. A favorite of journalists and their anonymous sources, SecureDrop makes it easy to share confidential information without revealing your identity.
Your ISP only sees the encrypted VPN traffic and won’t know you’re on Tor. A logless VPN, which doesn’t store any traffic logs nor session logs is highly preferable. Traffic logs are a bigger concern than session logs, but neither are good.

Read on to learn more about the five main types of darknet websites and what they contain. In principle, the dark web is just a version of the internet that you can only access using a Tor browser and where it’s almost impossible to identify the users and owners of the websites on there. However, because it’s almost completely anonymous, there are a lot of illegal images, information, products, and services on the dark web. Attempting to even view these can be illegal in many countries and states, so stay well clear of them if you want to keep a clean record and conscience. Unlike other search engines, it does not collect or share web activities and personal data of users.
Is The Dark Web Illegal?
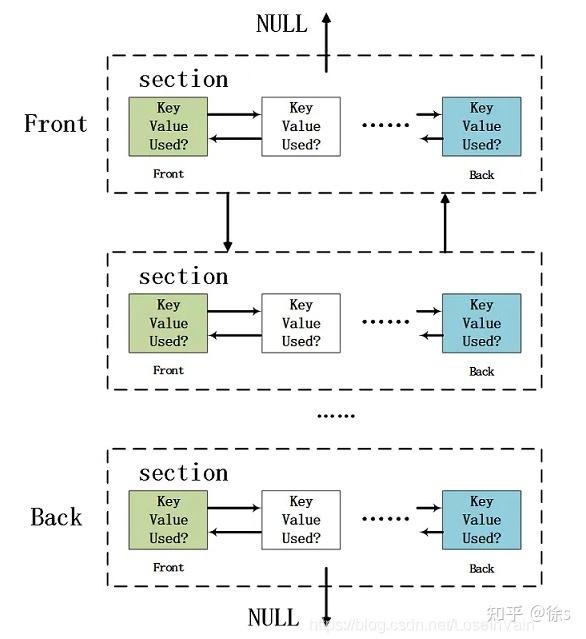
The peer-to-peer routing structure is more advanced, and it does not rely on a trusted directory to get route information. I2P uses one-way tunnels, so an eavesdropper can only capture outbound or inbound traffic, not both. Instead of “.com” or “.org”, dark web addresses can be distinguished by the top-level domain, “.onion“. NordVPN is offering a fully-featured risk-free 30-day trial if you sign up at this page.
Separate Your Real Life From Your Online Persona
And use a VPN for Android or a VPN for iOSto get a secure, private connection. Before accessing the dark web, install strong security software to help keep your device protected. The Tor network combined with a VPN is one of the safest ways to get on the dark web. Many internet service providers (ISPs) and governments are suspicious of Tor use, but a VPN will hide your internet activity and help prevent anyone from knowing that you’re using Tor.
As digital ecosystems morph, staying informed and agile will help you make the most of evolving privacy tools—or avoid stepping into ever-more complex traps. If your Social Security number is found on the dark web, take immediate action to protect yourself. Place a credit freeze or lock on your credit reports, monitor your credit reports and financial accounts closely for any unauthorized activity, and consider enrolling in a credit monitoring service. Additionally, contact the Social Security Administration to report the breach and discuss further protective measures. Tor Browser masks your IP address and routes traffic through multiple servers.