These systems can connect data across multiple platforms, even when users try to hide behind different identities. While this does not break Tor’s encryption, it does make the ecosystem less forgiving for careless users. AI brings efficiency to monitoring efforts and raises the stakes for anyone trying to stay anonymous online. The deep web is a part of the internet that isn’t indexed by search engines, like your email accounts or online banking. Artificial intelligence is now being weaponized to conduct more effective attacks. Threat actors can execute highly targeted and scalable attacks with minimal effort as more tools become accessible and easier to use.
- Keep in mind that you’ve to use very specific keywords when searching.
- High-volume vendors launch standalone shops using Tor and Monero, reducing dependency on marketplaces.
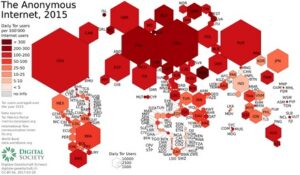
- In Asia, restrictions are stricter in places such as China and Iran.
- This page may contain sensitive or adult content that’s not for everyone.
- On the other, they remind us of the importance of privacy and the double-edged nature of anonymity tools.
What Is Insider Threat?
ASAP is a tech nerd’s playground—accepting BTC, LTC, ZCash, and Monero, it’s got options for days. Listings aren’t public, but it’s steady—think drugs (weed, pills, some synthetics), a few digital extras like cracked accounts. They’ve got 2FA and encryption that’s tighter than a drum, which I’ve tested against crash-prone sites and found solid. Word’s out they’re going decentralized in 2025—less downtime, more trust, right in line with where things are headed.

Accessing Onion Sites On Android
- Due to law enforcement, many markets now require invites, referrals, or verified PGP identities.
- Global law enforcement agencies face mounting challenges in tracking and dismantling dark web operations.
- For instance, you can choose the preferred security levels for enhanced protection.
- Onion sites (aka Tor sites) are websites only accessible on the dark web; you can’t view them using a regular browser.
The US Naval Research Laboratory developed The Onion Routing (Tor) project in the late 90s. A network browser gives you access to sites with the ‘.onion’ registry operator. Some of the deep web sites do not use standard top-level domains (TLD) such as .gov, .com, .net, etc.
Predictions, Episode 1: Financial Cyberthreats
Activists and government critics prefer to remain anonymous, fearing repercussions if their identities are revealed. Besides, victims of crime may want to hide their identities from their perpetrators. Nonetheless, if whatever you do is deemed illegal in your country, you can get into trouble. Therefore, the legality of the dark web will mainly depend on how you use it. You can quickly get into trouble for acting illegally, such as infringing on other people’s safety and freedom. Furthermore, it’s critical to understand that Whonix is not a stand-alone browser.
Best Dark Web Sites 2025 – Detailed List
AI-powered monitoring will help identify scams faster, but it will also give law enforcement stronger tools to track criminal activity. For users, the safest path is responsible use—treating hidden services as tools for privacy, research, and free expression rather than reckless exploration. The dark web will not vanish, but it will keep evolving under constant pressure from both technology and regulation.
The Mysterious World Of onion Dark Web
STYX Market focuses specifically on financial fraud, making it a go-to destination for cybercriminals engaged in this activity. Some marketplaces also establish parallel channels on Telegram to expand their reach, further complicating monitoring efforts. Ultimately, this disruption to accessibility is not a unique event. In fact, it is routine for individual’s participating in these dark web communities, par for the course of engaging in the markets.
Part 2 How To Be Safe On Darknet Markets
It asks you to pay the merchant fee if you want to sell something, preventing the buyers from getting scammed. The marketplace has a pleasant, user-friendly interface built from the ground up. Its interface makes it easy to identify clone websites and ensures that users always use the authentic site.
Without these tools, many cases of abuse might never reach the public. Nothing here should be seen as a push to join illegal markets or unsafe sites. If readers choose to explore further, they should use tools like the Tor Browser, a VPN, and privacy-focused operating systems.
Alright, let’s get into the meat of it—the darknet markets that are ruling 2025. I’ve been poking around these places for a while now, from the giants like Abacus to the old-timers like Vice City. This isn’t just a quick list; it’s the full scoop on what they offer, how they keep things tight, and why they’re worth your time—or not. Whether you’re new to the dark web or a vet who’s seen it all, you’ll find something here to chew on. Below, I’m breaking down each market with everything I’ve picked up—listings, quirks, the works. The next big shift came with peer-to-peer networks like Napster, LimeWire, and BitTorrent. mark it means it has been verified as a scam service and it should be avoided. Get the latest in privacy news, tips, tricks, and security guides to level-up your digital security. Activists, whistle blowers, and journalists also use the dark web to communicate securely with sources and news organizations. These domain names are not registered with a central authority but are instead derived from cryptographic keys.|This same technology also protects the websites themselves, keeping operators and visitors anonymous. The dark web is a hidden part of the internet that isn’t indexed by search engines like Google and Bing, meaning you won’t find links to dark web sites in mainstream search engine results. Instead, it uses its own search engines – we’ll get to that later.}
To fully understand what the dark web is and whether there’s any reason for you to go there, we’ll break down the different layers of the internet and how they relate to one another. We’ll also dig into common questions like how to access the dark web and whether or not it’s safe. We’ll also share some tips for protecting your personal data if you decide to explore it. The deep web is the part of the internet you can’t access through search engines like Google and Bing.
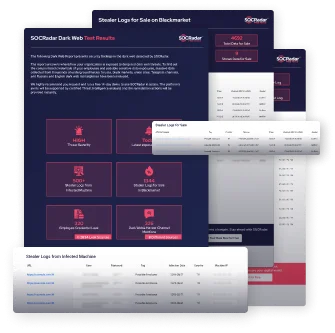
Ransomware gangs are also expected to diversify their tactics, targeting smaller companies and individual users to maximize their reach. Businesses should prepare for more sophisticated ransomware campaigns, potentially leveraging AI to exploit security gaps. The takedown of major groups like LockBit, AlphaBay and Hansa in 2024 demonstrates improved global collaboration among law enforcement agencies.
In response to escalating cyber threats, governments worldwide are enacting stringent regulations aimed at curbing dark web activities. Initiatives include enhanced monitoring of cryptocurrency transactions and international collaborations to dismantle illicit online marketplaces. While these measures have led to the shutdown of several high-profile platforms, the decentralized nature of the dark web poses ongoing challenges to regulatory enforcement. Markets and unverified directories will keep surfacing and collapsing.